Spliced feed for Security Bloggers Network |
| .be hacked today : some supported by flemish government [belsec] [Belgian Security Blognetwork] Posted: 05 Nov 2008 06:32 AM CST |
| THese are the Humo pics you may not see in Belgium [belsec] [Belgian Security Blognetwork] Posted: 05 Nov 2008 05:21 AM CST We did not place these pics ourselves. We found the links somewhere inside an article. If the link doesn't work anymore, please post new ones in the directory. This computer or connection will and can not place those pics because it would be too easy for others to shoot the pianist. We are only reporters. What is here to report ? THat by their courtcase the interest at these stupid bad taste pics that are in fact childish and just disgustful will have much more publicity than they in fact would have had before. And that even legally they would have won more going to court for damages and that these damages would increase with each number sold.... This would make any publisher think twice because even the cost of such a courtcase may be not worth the trouble publishing such rubbish stuff they call satire. If that is satire I am Shakespeare. I think there are smarter things to do with that situation than these pics It is also quite astonishing to see now some people making claims about liberty of the press and so on but this ain't a case for which you should storm the barricades. The unilateral decision by the judge is a scandal and should be abolished. THe judge should always be obliged to hear all concerned parties before making any decision because that is why he is called a judge. To hear all parties, experts and the evidence and to take a decision. Even if those are preliminary and can be revoked afterwards, but all parties should be heard so he can have an informed judgment. In the age of the internet such judicial actions are mostly worthless. |
| Banned Humo magazine for sale online [belsec] [Belgian Security Blognetwork] Posted: 05 Nov 2008 04:59 AM CST |
| what is the present cybersecurity level ? [belsec] [Belgian Security Blognetwork] Posted: 05 Nov 2008 04:53 AM CST |
| 6000 emailadresses available from Belgian students [belsec] [Belgian Security Blognetwork] Posted: 05 Nov 2008 04:50 AM CST |
| Yes, we also can [belsec] [Belgian Security Blognetwork] Posted: 05 Nov 2008 04:30 AM CST The secure internet won't come by itself. The malware gangs won't give up by themselves and the insecure applications and installations won't become secure overnight and by themselves. They will only become safe if enough people, movements and politicians believe together that something has to be done for the good of the people whoever they are and whatever they are. A safe and secured internet is a basic necessity for all so that all can use it to communicate, learn and trade with an acceptable level of trust and security without additional costs or a steep learning process. It is for this reason that we have to believe that in the end we have a possibility to prevail, to achieve something, to push things in the right direction and to make way for those behind us that in the footsteps of this 'ideology' of public service and responsability will make the safe and secure internet someday somehow a reality for an ever growing number of people. Because I have also a dream. A dream that every man, women or child can use the internet without being confronted by viruses, spam, fraud or attacks at the present levels. And maybe we can say someday 'yes we can' because the internetsecurity needs also a change we can believe in. |
| Beginner’s guide to OpenID phishing [/dev/random] [Belgian Security Blognetwork] Posted: 05 Nov 2008 02:18 AM CST
I already talked about OpenID (here or here). OpenID is a web based solution which provides single sign-on to other websites: once authenticated via a “provider“, you are able to use a lot of services (websites) via “consumers“. This system is very user-friendly but is also a good target for phishers! Why? A lot of commercial or financial websites are victims of phishing attacks. Today, there is a business behing malicious activities. You’ve money or personal data which also have a price on the underground market (SS#, CC#, …). As more and more services are compatible with OpenID, the risks of phishing attacks are much more critical. If you loose your OpenID credentials, you’re potentially vulnerable on *ALL* the compatible websites! Marc Oslot wrote a good paper about OpenID phishing: Beginner’s guide to OpenID phishing. |
| [Chinese]小心!黑客隔墙“偷听”你的键盘 [Telecom,Security & P2P] Posted: 05 Nov 2008 01:14 AM CST 我们知道电磁辐射总是显示着它不好的一面,在国家和军事层面的信息安全都要考虑电磁泄露的,通常在商业领域和个人层面就不再考虑电磁泄漏和相关的Hacking。下面的报道带来了一些忧虑,一旦这样的设备或者技术变得普及,就得烦请大家在铁丝网、电磁屏蔽室中工作了! 几个来自洛桑联邦理工学院安全和密码学实验室的家伙,对劣质有线键盘的键击信息进行偷听,他们最大的帮手就是电磁辐射。他们发现了四种不同的偷听方式,从2001-2008年生产的,11款包含PS/2,USB接口乃至笔记本键盘的键盘中他们都至少找到一种攻击方法。这些攻击方法可以穿透65英尺的墙壁。 点击看报道视频,点击看Hack Eye的报道。 Share To: |
| Been to the mountaintop and seen the promised land [StillSecure, After All These Years] Posted: 05 Nov 2008 12:12 AM CST
Could it be only 40 years ago that Martin Luther King, Jr. spoke these words? America is a country that continually reinvents itself. The election of Barak Obama is chance once again for us to seize the imagination of the world and remind them why America is really that shining city on the hill. Whether we voted for him or not, we are all filled with optimism for a new generation to take charge and make our mark on this new century. Congratulations and God's grace to President elect Obama! Related articles by Zemanta |
| Links for 2008-11-04 [del.icio.us] [Anton Chuvakin Blog - "Security Warrior"] Posted: 05 Nov 2008 12:00 AM CST |
| F-Secure report new worms through MS08-067 [Telecom,Security & P2P] Posted: 04 Nov 2008 11:41 PM CST F-Secure is now reporting on a worm which exploits the critical vulnerability addressed in Microsoft’s MS08-067 bulletin which target English versions of Windows XP (SP2 and SP3) and Windows 2003 SP2. The exploit payload downloads a dropper that they detect as Trojan-Dropper.Win32.Agent.yhi. The worm component is detected as Exploit.Win32.MS08-067.g and the kernel component as Rootkit.Win32.KernelBot.dg. [...] |
| Grecs’s Infosec Ramblings for 2008-11-04 [NovaInfosecPortal.com] Posted: 04 Nov 2008 10:59 PM CST
|
| I hope you voted [Network Security Blog] Posted: 04 Nov 2008 10:29 PM CST |
| Quick Update [The Security Shoggoth] Posted: 04 Nov 2008 08:35 PM CST Hello all - I haven't posted in a while and for good reason. I've been busy with a very interesting job at work that I hope to be able to talk about some day. Right now I can't (client privacy and such) but I can guarantee it will make an amazing story some day. It is because of this job that I was unable to make it to the NE Ohio Information Security Summit. I apologize to everyone who thought I would be there and I have to commend and profusely thank Greg for taking over our presentations by himself and coming up with one at the last minute. Greg is an amazing speaker and friend and I'm glad he had packed crowds in both sessions. As for the malware challenge, we were supposed to announce the winners at the summit. However, due to my being absent we decided to (wisely I think) postpone announcements until the next NE Ohio Information Security Forum meeting on November 19th. I invite everyone to come out as we will be giving out prizes there and announcing the winners (and will announce them on the site shortly after). I will have some interesting news in the next couple weeks and am starting on a few projects I will be blogging about. For those who have stuck with my blog, thanks. I hope not to disappoint you. :) |
| Riverbed release RiOS 5.5 to support Domino Notes [Telecom,Security & P2P] Posted: 04 Nov 2008 07:51 PM CST Riverbed is a widely used appliance that can help accelerate the Wide Area Network (WAN) performance of mission critical applications. At the same time, it can help compress the traffic so that the cost savings of your expensive backbone network. However, before this release, it can not support Domino Notes, which means typically the biggest [...] |
| AT&T, Lenovo and Ericsson to offer internet service on ThinkPad notebook [Telecom,Security & P2P] Posted: 04 Nov 2008 07:45 PM CST AT&T, Lenovo and Ericsson have formed a new alliance to enable business PC users to access broadband-speed internet via their ThinkPad notebook PCs. The collaboration is expected to lower the price premium usually associated with built-in mobile broadband technology by up to $150 per PC from previous pricing. Click to read more. Share To: |
| Posted: 04 Nov 2008 05:57 PM CST  The European Network and Information Security Agency has just released their latest position paper on "Security and Privacy in Virtual Worlds and Gaming". Malicious programs that specifically target online games and virtual worlds aimed at stealing online game passwords are becoming a serious problem. Such malware is invariably aimed at the theft of virtual property accumulated in a user's account and its sale for real money. The failure to recognise the importance of protecting the real-money value locked up in this grey-zone of the economy is leading to an exponential increase in attacks targeting online MMO/VWs. (Photo under creative commons from thms.nl's photostream) |
| Hack in the Box slides are online [Security4all] [Belgian Security Blognetwork] Posted: 04 Nov 2008 05:56 PM CST  HITBSecConf2008 organized in Malaysia is another excellent conference which has published their presentations. They are now available for download. (Photo under creative commons from leduardo's photostream) |
| Toorcon X presentations online plus a video interview [Security4all] [Belgian Security Blognetwork] Posted: 04 Nov 2008 05:55 PM CST  ToorCon, has had its 10th year running, and is San Diego's hacker conference bringing together the top security experts to present their new tricks of the trade. For those not present and interested in the topics; you can now download the presentations from the ToorCon X Conference . Hour Presentations
20 Minute Presentations
Related posts:
|
| Interesting Information Security Bits for 11/04/2008 [Infosec Ramblings] Posted: 04 Nov 2008 05:44 PM CST Good afternoon everybody! I hope your day is going well. Here are today’s Interesting Information Security Bits from around the web.
That’s it for today. Have fun! Subscribe to my RSS Feed if you enjoy these daily Interesting Bits posts. Kevin Posted in Interesting Bits |
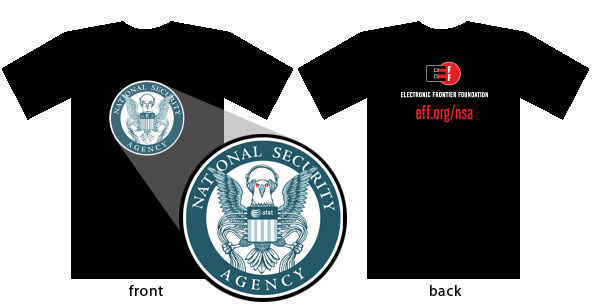
| EFF NSA shirt...I gots mine! [Carnal0wnage Blog] Posted: 04 Nov 2008 04:52 PM CST |
| Posted: 04 Nov 2008 02:15 PM CST @GeekGrrl posted a note on her blog asking this question: 1) How would you recommend getting started on a career toward Network Security/Network Pen Tester? She has some follow-up questions to that first one requesting some specific information. Go read her post and then come back. Here is a good blog post that might help. http://www.leune.org/blog/kees/2008/10/-tips-for-getting-started-1.html 1) Certs -
2) Cons
3) Associations
4) Books
5) Other
Finally, VirtualBox is a great free virtualization platform for Windows and Linux that will let you setup VMs like DVL to hack against. Go ahead and offer up your suggestions in the comments. UPDATE: On the drive home I today, I was still thinking about this question and I realized I left off one things that an individual can do that will probably reap more benefits than any of the items listed above. Find a mentor. Find somebody who has been in the business for a while who is willing to let you bounce questions off of them and is willing to give you the benefit of their experience when you hit situations that you are not familiar with. Somebody who can offer you those second opinions that can be so helpful. Here is a link to a bunch of articles on finding a mentor and the mentoring relationship. The articles are not infosec related at all, but still apply. http://www.inc.com/guides/growth/24509.html Kevin Posted in career |
| On Small Companies and PCI Compliance [Anton Chuvakin Blog - "Security Warrior"] Posted: 04 Nov 2008 01:49 PM CST Read this post ("E-Commerce Startups deal with PCI compliance" at "PCI Anwsers" Blog) and weeeeeeep: "I once was talking with a small business owner who was reading through the Self-Assessment Questionnaire (SAQ) and stopped at the first question, which basically said, Do you have a properly configured firewall? The business owner called into the back room and asked the store manager, "Hey, do we have a firewall?" The store manager replied that he thought they had a fire extinguisher which was up to date. I then watched as the store manger checked the "In Place" box on the form stating they had a properly configured firewall in place." Wonna "sell PCI compliance" to small businesses? One need to get smart in a very special way! :-) |
| Where were they when I needed them? [StillSecure, After All These Years] Posted: 04 Nov 2008 01:14 PM CST VNUnet today reports that network security vendor Network Box has come out with a white paper on best practices for corporate blogging security. The paper talks about comment spam and SQL injection attacks as leading ways that blogs could be compromised. Of course I don't see anything in there about passwords and reusing the same passwords, but hey its better than nothing. Might be worth your time to take a quick read. |
| Man-In-The-Browser Mitigation Advice That Companies Won't Follow [Articles by MIKE FRATTO] Posted: 04 Nov 2008 10:59 AM CST |
| Follow the election results tonight on this blog [StillSecure, After All These Years] Posted: 04 Nov 2008 09:54 AM CST |
| E-voting Glossary [Network Security Blog] Posted: 04 Nov 2008 09:36 AM CST If you’re wondering what some of the acronyms around electronic voting mean, here’s a glossary of terms for you. I know I learned a couple of new terms by reading it. Thanks to digiphile on Twitter. |
| How the Death of Privacy and the Long Archive May Forever Alter Politics [securosis.com] Posted: 04 Nov 2008 09:00 AM CST Way back in November of 2006 I wrote a post on the impact of our electronic personas on the political process. I was thinking about re-writing the post, but after reviewing it realized the situation is exactly the same two years later… if not a bit worse. As a generation raised on MySpace, FaceBook, and other social media starts becoming the candidates, rather than the electorate, I think we will see profound changes in our political process. I’m off in Moscow so I’m pre-posting this, and for all I know the election is in the midst of a complete meltdown right now. Here again, for your reading pleasure, is the text of the original post: *** As the silly season comes to a close with today’s election (at least for, like, a week or so) there’s a change to the political process I’ve been thinking about a lot. And it’s not e-voting, election fraud, or other issues we’ve occasionally discussed. On this site (and others) we’ve discussed the ongoing erosion of personal privacy. More of our personal information is publicly available, or stored in private databases unlocked with a $ shaped key, than society has ever experienced before. This combines with a phenomena I call “The Long Archive”- where every piece of data, of value or not, is essentially stored for eternity (unless, of course, you’re in a disaster recovery situation). Archived web pages, blog posts, emails, newsgroup posts, MySpace profiles, FaceBook pages, school papers, phone calls, calendar entries, credit card purchases, Amazon orders, Google searches, and … Think about it. If only 2% of our online lives actually survives indefinitely, the mass of data is astounding. What does this have to do with politics? The current election climate could be described as mass media shit-slinging. Our current crop of elected officials, of either party, survives mostly on their ability to find crap on their opponent while hiding their own stinkers. Historically, positive electioneering is a relative rarity in the American political system. We, as a voting public, seem to desire pristine Ken dolls we can relate to over issues-focused candidates. No, not all the time, but often enough that negative campaigning shows real returns. But the next generation of politicians are growing up online, with their entire lives stored on hard drives. From school papers, to medical records, to personal communications, to web activity, chat logs (kept by a “trusted” friend) and personal blogs filled with previously private musings. It’s all there. And no one knows for how long; not really. No one knows what will survive, what will fade, but all of it has the potential to be available for future opponent research. I’m a bit older, but there’s still an incredible archive of information out there on me, including some old newsgroup posts I’m not all that proud of (nothing crazy, but I am a bit of a geek). Maybe even remnants of ugly breakups with ex-girlfriends or rants never meant for public daylight. Never mind my financial records (missed taxes one year, but did make up for it) and such. In short, there’s no way I could run for any significant office without an incredibly thick skin. Anyone who started high school after, say, 1997 is probably in an even more compromising position. Anyone in the MySpace/FaceBook groups are even worse off. With so much information, on so many people, there’s no way it won’t change politics. I see three main options:
Realistically we’ll see a combination of all the above, but my biggest concern is how will this affect the quality of candidates? We, as a society, already complain over a lack of good options. We’re limited to those with either a drive for power, or a desire for public good, so strong that they’re willing to peel open their lives in a public vivisection every election cycle. When every purchase you’re ever made, email, IM or SMS, blog post, blog comment, social bookmark, WhateverSpace page, public record, and medical record becomes open season, who will be willing to undergo such embarrassing scrutiny? Will anyone run for office for anything other than raw greed? Or will we, as a society, change the standards by which we judge our elected officials. I don’t know. But I do know society, and politics, will experience a painful transition as we truly enter the information society. |
| CSI 2008 [How is that Assurance Evidence?] Posted: 04 Nov 2008 08:50 AM CST How is that Assurance Evidence is proud to announce that will be giving away one pass to CSI 2008. This is not the free expo pass, this is a conference pass worth serious coin. I will be there on various days depending on work, life, etc. The rules are these: The winner will need to answer a question regarding Information Assurance (probably FISMA related). The question will deal in facts, or at least my interpretation of the facts. The question will be posted Noon tomorrow (November 5th), and the first person with the correct answer will be the winner. Please leave a way for me to contact you. Good Luck!   |
| You are subscribed to email updates from Security Bloggers Network To stop receiving these emails, you may unsubscribe now. | Email Delivery powered by FeedBurner |
| Inbox too full? | |
| If you prefer to unsubscribe via postal mail, write to: Security Bloggers Network, c/o FeedBurner, 20 W Kinzie, 9th Floor, Chicago IL USA 60610 | |




![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=47fec5c7-b72e-4635-848e-56c56dc0adb8)
No comments:
Post a Comment