Spliced feed for Security Bloggers Network |
| Vendors aren't changing focus, you were just blissfully unaware [StillSecure, After All These Years] Posted: 08 May 2008 07:09 AM CDT My friend Michael Farnum besides being a comic book nerd, blogs over at ComputerWorld. Michael writes today about his opinion that vendors have changed focus from concentrating on the tech geeks to focusing on the business decision maker. Michael's proof is rather subjective, but revolve around the fact that when he was a geek not in management, vendors use to wine and dine him to influence him to support their technology and tell his boss to buy their products. As he moved up to become a geek in management, he noticed the vendors shifting focus away from the technical stakeholder to the business stakeholder. Michael has a theory on some of the reasons for this shift of focus. The dotcom bubble, the evolution of IT, people making decisions on sound business principles, not on what technology is cool. |
| May 3rd 1978 - The First Spam Email [Commtouch Café] Posted: 08 May 2008 03:18 AM CDT A notable anniversary slipped by at the weekend with the announcement that the very first ’spam’ email was sent on May 3rd 1978. Long before the Internet became part of everyday life there was Arpanet developed by the US Department of Defense. According to The Times on May 3rd 2008, it was a marketing person [...] |
| ScanlessPCI.com – Joke or Scam? [PCI Blog - Compliance Demystified] Posted: 07 May 2008 10:33 PM CDT You have to love the ingenuity of some people. While at the ETA show in April, I was informed of ScanlessPCI.com (http://www.scanlesspci.com) by another QSA. If you go to that site, the following is posted to the right hand side of the page.
From what we can ascertain, ScanlessPCI.com is just a scam. Their "patent pending" scanless technology is just what it says, it is scanless – meaning they do NOT scan anything. They are merely providing a certificate that you post on your Web site that indicates that you are PCI compliant. However, since they do not say that they provide you any vulnerability scanning reports, there is no way you can comply with the PCI DSS's quarterly vulnerability scanning requirement.
This just appears to be legal speak for go ahead and try to take us to court, you are required to go to arbitration. Oh, and by the way, any damages are so limited, that you will be wasting your time. The larger concern is the fact that they require you to insert code into your Web site to get a copy of their certificate. Since you are inserting code into your Web page for a GIF, it is anyone's guess as to whether or not they are hacking your site at the same time they are supposedly protecting it. |
| Store and Forward PCI Compliance [PCI Blog - Compliance Demystified] Posted: 07 May 2008 08:50 PM CDT Many people ask about storage of data pre-authorization (that is before the authorization for the transaction has occurred) and what it means for PCI DSS compliance. First, we should point out that PCI DSS does not address pre-authorization data storage, this is managed by the individual card brand Operating Regulations. But we know that many merchants will use Store and Forward (SAF) for transactions, “typically ISO 400 messages with many of these containing field 35 (Track II Data)“. This is where a merchant is offline either intentionally or not, and they queue up transactions that are stored locally. Later when the merchant goes back online they send these transactions off to their acquirer (and transitively onto the issuer) for processing. These transactions are also sometimes called “on us” transactions, because if the response from the issuer is ‘denied’ then the merchant must absorb the cost of the bad transaction. Aside from all this, it’s important to point out that sooner or later the transaction will go through and be completed. This means that any data stored in a pre-authorization style will eventually be authorized and this the responsibility of the merchant to protect. If the cardholder data is ever compromised from the merchant and fraudulent transactions are traced back to the merchant, as the Common Point of Purchase (CPP), the responsibility still falls on the merchant. This is why I advise merchants to protect cardholder data that is stored in pre-authorization transactions the same as they would for other cardholder data (i.e. PCI DSS Requirement 3.4). Of course they should always check their card brand Operating Regulations for official statements. The Payment Systems Blog points out:
AndrewJ also points out that:
|
| CEOs of large companies targeted in new whaling wave [Security4all] [Belgian Security Blognetwork] Posted: 07 May 2008 08:39 PM CDT |
| Video: Hak5 Episode 3×10 Released: Disaster Finale [Security4all] [Belgian Security Blognetwork] Posted: 07 May 2008 08:25 PM CDT |
| Treasury Institute PCI workshop [PCI Blog - Compliance Demystified] Posted: 07 May 2008 08:18 PM CDT I got back last night from presenting at the Treasury Institute PCI Workshop that Walt Conway puts on every year. It was a great success with over 130 participants from just about every major university and higher education facility. It was nice meeting both TouchNet and infiNET, sponsors of the event and companies that I performed their first PCI assessment many years ago. I also saw Breach Security a sponsor and company that helps prevent against bad things. I gave a presentation talking about “Heroes, Chorus Lines, and Community”. The three parts translate shortly into:
This event was focused around the implementation of PCI DSS compliance projects for Higher Education. In between were presentations such as mind, those from Benita Kahn on the legal aspects of PCI, and Bob Russo, Chairman of the PCI SSC. |
| Billion pound UK CCTV solves 3% of crimes. Efficient? [Security4all] [Belgian Security Blognetwork] Posted: 07 May 2008 08:10 PM CDT |
| The Oracle speaks [StillSecure, After All These Years] Posted: 07 May 2008 07:55 PM CDT No not Larry Ellison. StillSecure's oracle of NAC, Dave Greenstein, Chief Security Architect at StillSecure. I write and speak a lot about NAC, but Dave actually lives NAC. He led our development team that developed Safe Access. Now he is way out in front researching and designing the next generations of Safe Access and our other products. Dave doesn't comment on my posts a lot. I am always bugging him to start his own blog. The best I get is occasionally he will write an article or white paper. So when he commented on Joel Snyder's article on NAC and my comments, I figured it would make sense to give it some main column play. Here is what Dave had to say:
BTW, if you think Dave makes some sense here and would like to hear more from him, let me know and I will coax him into writing some more! I should also add that I twisted his arm to give Safe Access a plug at the end there. Thanks Dave! |
| ebizQ with Mike Rothman [StillSecure, After All These Years] Posted: 07 May 2008 07:41 PM CDT
|
| PCI Council Hosting Webinar on PA-DSS [PCI Blog - Compliance Demystified] Posted: 07 May 2008 07:39 PM CDT Today the PCI SSC (Council) announced it will host a webinar titled ” "Understanding the Payment Application Data Security Standard” on Thursday May 22, 2008 at 11:30 a.m. EDT and a second session the same day at The event will cover the following topics:
I highly recommend you attend to get all the information you can about this new standard. Also, if you did not view the last webinar you can see it online at: Navigating and Understanding the PCI SSC Self Assessment Questionnaire. |
| PCI pentesting from the inside: it's open season [Security4all] [Belgian Security Blognetwork] Posted: 07 May 2008 07:31 PM CDT |
| Data Classification and PCI [PCI Blog - Compliance Demystified] Posted: 07 May 2008 07:24 PM CDT I’m going to step out on a limb here and contradict what others have been saying about data classification. Data classification is not dead! PCI DSS Requirement 9.7.1 says, “Classify the media so it can be identified as confidential.” This is in reference to distribution of electronic media (i.e. backup tapes). The previous wording was to “Label media…” but we knew what this meant and didn’t all go out buying label guns to stock along side the duct tape we already had. Data classification + change control = a great way to get a handle on global/enterprise data access and contain the spread of cardholder data. I think this is the congruence with what Rich Mogull says on his Securosis blog. You do not need to meta-tag ever data element, but there should be some process to classify your data. More importantly you need a way to alert others who are accessing that sensitive data that they need to (1) contact the regulatory compliance person for that group or (2) take the necessary action to protect how they are storing it that is in-line with corporate and regulatory requirements. Setting up an initial classification system is only good until the next change control where someone you never thought would access your cardholder data now can. It was Michael Cook of Wal-Mart who said, “our perspective is, we are always one chance control event away from being non-compliant.” This can be taken in many different contexts because it can apply to many different contexts. Having a solid change control program that is tied into your data classification system is critical. |
| Viddler and Rev3 sitting in a tree [Srcasm] Posted: 07 May 2008 06:51 PM CDT K-I-S-S-I-N-G! Great news for both teams, Revision3 and Viddler have decided to team up — errr, Rev3 has decided to host all of their videos on Viddler’s system. See a tidbit from Colin’s latest post on the Viddler blog:
Not only is this great for Viddler (as any publicity is good publicity and this is surely great) but this also means a great new feature is rolled out (at least I think it’s new), Digg right in the Viddler videos. (Forgive me if it’s not but if it’s new to me, it’s new because it’s my blog and I said so.)
So go ahead, behold the beautiful new child that is Vidiggler and bask in its glory — or at least give it a whirl on your own videos. What do you think of Viddler and Rev3 joining forces? Or better yet, what are your thoughts on Web2.0 companies joining forces in general? |
| Yet another sql injection detected (Updated) [Security4all] [Belgian Security Blognetwork] Posted: 07 May 2008 06:45 PM CDT |
| Eronious charge to merchant account [PCI Blog - Compliance Demystified] Posted: 07 May 2008 05:45 PM CDT Yesterday a reporter called me asking if I knew anything about a “PCI compliance” charge tacked onto their merchant bill. I didn’t, but went back and checked on our merchant ID, and found something strange. It seems an ISO (independent sales organization) had billed us at $20/month for some scanning service that (a) we did not request and (b) was not from an ASV. Has anyone else been billed for something like this? The ISO we used said it was “a Visa charge” but this is totally false. I’d like to know if this is affecting others. Update: The Merchant Account Blog covered this yesterday. Read their post and the comments they left. We need to get to the bottom of this. |
| Notacon 4 conference videos [Security4all] [Belgian Security Blognetwork] Posted: 07 May 2008 04:52 PM CDT |
| Ooops! I Made a Boo Boo! [/dev/random] [Belgian Security Blognetwork] Posted: 07 May 2008 04:49 PM CDT
Do you have a good backup? Read the following story. Having redundant disk systems (RAID), database replicas and high-availability servers is not enough! More than third of data lost is caused by human mistakes! A good backup procedure is mandatory, with off-site storage of course. Last advice: the procedure must include a full-restore test! |
| Mid-Week Spywareguide Roundup [Vitalsecurity.org - A Revolution is the Solution] Posted: 07 May 2008 03:10 PM CDT Here we go again! * I just called, to say.....nothing, actually: Strange and annoying phonecalls. We all hate them, don't we? Especially when you can't decide if they're trying to sell you things (bad) or just steal all your personal data to sell on (worse). * It's a trap: Hot chick adding herself to my Myspace friends list = Disaster. Mind you, I have plenty of real hot chicks on my list so that's okay. * Hackmemes: Did you ever want to see a DDoS tool whose sole purpose for creation was as part of a meme war? Even better, a DDoS tool that's actually stuffed full of memes purely so it'll gain acceptance with the groups involved in the battle in the first place? Then here comes Christmas.  ....you do like Mudkips, right? |
| Protecting the global Internet routing infrastructure [tssci security] Posted: 07 May 2008 02:16 PM CDT Arbor Networks has a blog post up today about Using RPKI to Construct Validated IRR Data. Resource PKI (RPKI) is an extension to X.509 to allow for IP address (prefix) and AS identifiers (autonomous system numbers — the organization-based assigned number used by the Border Gateway Protocol to get you or your ISP “online”). My first introduction to hijacking traffic at a global level was in 1997. A certain ISP that I knew would typically test their attack theories and concepts live by re-routing, redirecting, and outright stealing traffic using BGP-4. It was often done to spammers, typically those already in a customer relationship with the provider. By using a TCP/IP routing concept known as a “more-specific route”, or MSR as I like to refer to it — a route injected into the RIB (routing information base, or “routing table” as most people call it) that has a shorter-prefix (a /24 instead of a /23) will be selected by the RIB to be the destination of all traffic that is categorized by that prefix. If, say, the 2 /24’s that make up a /23 are both injected into the RIB, then all traffic destined to that /23 is now directed instead to the /24 MRS’s. Historically, there has been little to nothing to prevent this from happening at a global level. As we spoke about in the Day 12: ITSM Vulnerability Assessment Techniques post, even YouTube was recently hijacked by Pakistan using the exact concepts above. Note that this is different than regular IP/ASN hijacking. The YouTube incident was BGP traffic hijacking. The difference (and they are even worse when combined) is that IP/ASN hijacking involves modifying the RIR (Regional Internet Registry) database records to new information, such as contact, DNS, RWhois, and other ownership rights. The world was first officially introduced to this style of attack in 1999 when CERT released an advisory detailing the Potential for False Authentication in Registry Transactions aka the “MAIL-FROM:” attack, which works just like regular domain hijacking. Typically, the defense to these types of attacks has had one major stop-gap: ISP filtering, in particular — customer filtering, which is typically/historically applied only on the customers. When L0pht presented to Congress in 1998 and told them that they could “take down the entire Internet in 30 minutes or less” — Mudge and company were likely referring to the fact that route filters were applied at the customer level (and not even always there), but not in between ISP peering relationships. Route-filters on ISP peering, especially “default-free zone” (DFZ) peering, often used the IRR (Internet Routing Registry) information to build a preventative measure. Hoewver, the IRR system itself (the primary vendor/organization being the RADB — or the Routing Arbiter Database, or now known as the “Router Assets Database”) was typically vulnerable to the same “false authentication” attack and other abuses such as social engineering. RPKI looks like it goes a long way towards ensuring an easy path for ISP’s and other BGP-speaking organizations to protect their routes and deliver an infrastructure that could withstand simple attack vectors such as these. |
| Users Learn More with Fun [/dev/random] [Belgian Security Blognetwork] Posted: 07 May 2008 01:49 PM CDT
From a end-user point of view, security is boring. It’s part of the human behaviour: if it’s too much annoying, people will not follow the rules! Even more in the IT security domain. I read the following story on the CISSP forum today. The question was: “We are doing a campaign on why users should secure their desktop when they are not at their desk. Does anyone know of a good tale where an unattended/unlocked desktop was used to steal personal information, send an e-mail using the owner’s identity, etc?” and one of the answers was: “This is not exactly what you’re asking for, but I can tell you what I’ve seen to be very effective. I worked in an organization where open season was declared on unsecured desktops. What we did was anyone spotting an unattended desktop that wasn’t locked would send an email to everyone in the organization announcing they were buying doughnuts the next morning. It was good natured fun but VERY effective. I do not recall a single second offender.“. Conclusion: Add some fun (but not too much) into your security presentations or campaign, users will be more receptive! |
| To believe or not - new research from Ponemon [Data Protection, Management and Leakage] Posted: 07 May 2008 12:52 PM CDT New research from Ponemon on consumer behavious post breach breach - apparently over 31% of those surveyed terminated ties with an organization that had a breach. Not sure to fully believe it when consumers say such stuff (I did not mean the Ponemon research itself:)) - I think consumers say what they think is the right thing to say. I think folks are still lukewarm when it comes identities getting stolen, card numbers being breached. There is not yet enough pain directly resulting from this. However, I do hope this is true though - high time we took such breach information more seriously. |
| Commtouch Research Center – A Cool Botnet Tool [Commtouch Café] Posted: 07 May 2008 07:29 AM CDT Last month we released our new service – GlobalView Zombie Intelligence. Commtouch Zombie Intelligence is a real-time feed of data containing zombies IPs along with rich information about their activity and behavior. As a result of our research and development in the field of zombies and bots, we are constantly gathering a vast amount of data [...] |
| Posted: 07 May 2008 06:20 AM CDT |
| PGP for free on Windows [Wouter Vleugelen Blog] [Belgian Security Blognetwork] Posted: 07 May 2008 05:47 AM CDT Here is the software you need to install if you want to use PGP for free on your Windows PC: - GnuPG for Windows - http://www.gpg4win.org/ - FireGPG Firefox Extention - http://getfiregpg.org/ GnuPG for Windows included GPGee, a tool that is accessible when right-clicking on files to encrypt or decrypt. It also includes WinPT, a graphical tool that can be used to manage keys and files. The FireGPG extention adds nice buttons in your Gmail web interface to sign/encrypt/verify emails which is quite handy when using gmail.
|
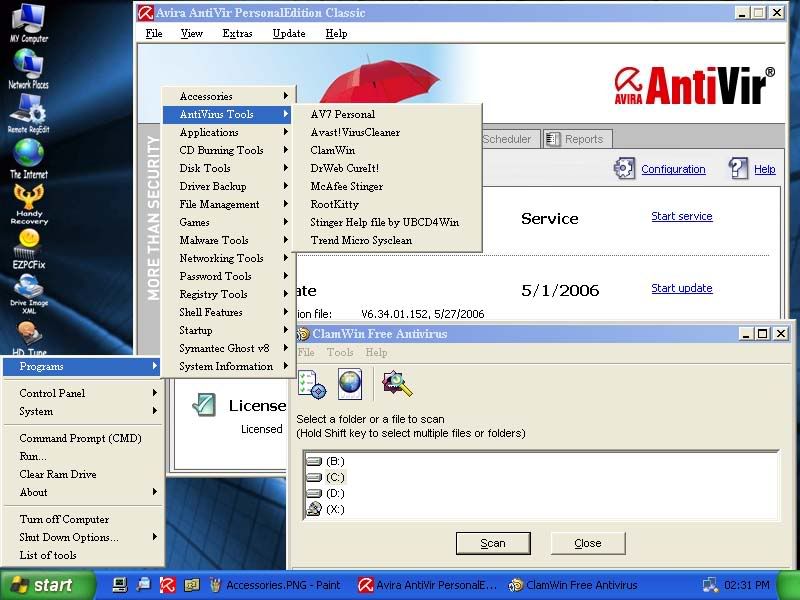
| Ultimate Boot CD for Windows (UBCD4Win) [Wouter Vleugelen Blog] [Belgian Security Blognetwork] Posted: 07 May 2008 05:36 AM CDT UBCD4Win is a bootable recovery CD that contains software used for repairing, restoring, or diagnosing almost any computer problem. Its goal is to be the most complete and easy to use free computer diagnostic tool. Almost all software included in UBCD4Win are freeware utilities for Windows. A list of tools included on the cd: http://www.ubcd4win.com/contents.htm
Some links for those in need of the good old bootable floppydisks: |
| Splunk [Wouter Vleugelen Blog] [Belgian Security Blognetwork] Posted: 07 May 2008 05:33 AM CDT Splunk is can be used to earch, navigate, alert and report on all your IT data in real time. Logs, configurations, messages, traps and alerts, script, code, metrics and more. Splunk is the perfect complement to Nagios. Nagios monitors your network for problems and Splunk helps you get to the root cause.
|
| Alternate Operating System Scanner (AOSS) [Wouter Vleugelen Blog] [Belgian Security Blognetwork] Posted: 07 May 2008 05:30 AM CDT Alternate Operating System Scanner (AOSS) is a bootable anti-spyware scanner which is able to run independently within its own self contained operating system. AOSS is not dependant on Microsoft Windows to be running on the PC, which enables AOSS to more effectively check, detect and remove deeply embedded spyware, adware and other malware, such as rootkits. |
| You are subscribed to email updates from Security Bloggers Network To stop receiving these emails, you may unsubscribe now. | Email Delivery powered by FeedBurner |
| Inbox too full? | |
| If you prefer to unsubscribe via postal mail, write to: Security Bloggers Network, c/o FeedBurner, 20 W Kinzie, 9th Floor, Chicago IL USA 60610 | |
 ebizQ published a podcast that Mike Rothman invited me on dealing with vendor consolidation and "big is the new small". It is always fun talking with Mike and we had a good time. I like that they also transcribed the podcast if you just want to read it. You can get it
ebizQ published a podcast that Mike Rothman invited me on dealing with vendor consolidation and "big is the new small". It is always fun talking with Mike and we had a good time. I like that they also transcribed the podcast if you just want to read it. You can get it 






No comments:
Post a Comment