Spliced feed for Security Bloggers Network |
| Security Briefing: May 6th [Liquidmatrix Security Digest] Posted: 06 May 2008 07:57 AM CDT  Nothing witty to say. And now, the news…
Click here to subscribe to Liquidmatrix Security Digest! Tags: News, Daily Links, Security Blog, Information Security, Security News |
| Have You Seen This Douchebag? [Liquidmatrix Security Digest] Posted: 06 May 2008 07:32 AM CDT  Interpol has sent out a request for help this morning and we’re only too happy to pass the word along. From INTERPOL:
If you have ANY information on who this jackhole might be please contact your local police department who can refer to INTERPOL. Pass it on. |
| That didn't take long [StillSecure, After All These Years] Posted: 06 May 2008 06:33 AM CDT Over the weekend I wrote an article about what a Yahoo shareholder would do with a copy of Steve Ballmer's letter to Jerry Yang. Well, it didn't take very long for a class action law suit being filed, led by two pension funds. Attorneys for the pension funds said, "The actions taken by Yahoo's CEO this past weekend confirm that the |
| VAR does it come from? CISCO Hardware Espionage [BlogInfoSec.com] Posted: 06 May 2008 06:00 AM CDT When an organization looks that the threats to their infrastructure, they generally categorize them into two main headers: internal and external. And when they think about the internal threats they generally consider the rogue employee as the highest threat, and outsiders being their competition. I want to discuss another threat that is a combination of the two that is presented to all organizations by one of their trusted sources. This threat is the Nation State, the trusted source is your Value Added Reseller and the method is counterfeit hardware. I will not get into the motives or justifications as to why a Nation State would have interest in infiltrating a Mom and Pop shop as there is no solid information to report; as this is all speculative. However, the Mom and Pop shop should be just as concerned as the US Government and large corporations are about the problem at hand. There is an unclassified FBI presentation that I confirmed is legitimate that has been released discusses the fear that China is intentionally having counterfeit Cisco hardware sold in the United States. In the presentation, the FBI discusses four cases that they had investigated where this hardware has been discovered even in classified networks. The more serious statements made in this presentation are on slide 30, where they claim about 10% of the information technology hardware that is sold globally is counterfeit and it is being sold through legitimate channels (KPMG is the cited source) for the past couple of years. In the case of Cisco, this counterfeit hardware is sold through their Cisco Gold and Silver Partners program. Other vendor vetting processes are just as flawed allowing this hardware to enter into your IT infrastructure. Why should the Mom and Pop shops be concerned? Short of having hardware in your infrastructure that is not working as advertised, there are issues regarding warranties, support and the products lifetime (according to the FBI report, some of these counterfeit devices catch on fire). For the larger organizations, you don't know for sure that the highly secured VPN tunnel you've configured really and truly is what you just configured. Is the problem limited to Cisco equipment? Of course not as indicated by the report released by KPMG. Even the raw components, such as memory and CPU's, are being copied for inclusion into your infrastructures devices. So though that device really may be from the vendor who is standing behind it, the storage medium within the device is counterfeit. Furthermore, counterfeit equipment is not just coming from China, but it also comes from many other countries as well. So enough with the FUD, what can you do to protect against this growing threat? Here are a few suggestions that I have been able to gleam:
More Resources: FBI Criminal Investigation: Cisco Routers – http://www.abovetopsecret.com/forum/thread350381/pg1 KPMG Managing the Risks of Counterfeiting the Information Technology Industry – http://www.agmaglobal.org/press_events/press_docs/Counterfeit_WhitePaper_Final.pdf Chinese Counterfeit Cisco Network Routers Targeted In North America – http://www.chinatechnews.com/2008/03/03/6443-chinese-counterfeit-cisco-network-routers-targeted-in-north-america/ Fake network gear – http://www.networkworld.com/news/2006/102306counterfeit.html Copyright © 2008 BlogInfoSec.com. This feed is copyrighted by bloginfosec.com. The feed may be syndicated only with our permission. If you feel that this feed is being syndicated by a website other than through us or one of our partners, please contact bloginfosec.com immediately at copyright()bloginfosec.com. Thank you! Again, please contact copyright@bloginfosec.com so we can take legal action immediately. |
| Oregon Offers Tuition Waiver [Room362.com] Posted: 06 May 2008 01:42 AM CDT Oregon’s State Legislature passed a law that provides a full-tuition waiver for a bachelor’s or master’s degree at an Oregon University System institution for children or spouses of service members who died on active duty, became 100 percent disabled in connection with military service, or died as a result of a disability sustained on active duty My home state rocks. |
| Posted: 06 May 2008 12:23 AM CDT For those who read my blog via feed reader and not on the web site itself, you may not have noticed the new ads and member badge from the Forbes Business and Finance Blog Network. I received an invitation to join an elite list of 400 blogs handpicked by Forbes. They will syndicate content and sell advertising for the site. There are some other cool benefits that go along with the membership. I was very proud to be selected for this, but frankly was worried about too many ads. If you get a chance, check out the site and have a look. I know it means I am going commercial, but am hoping it will lead to a broader audience. |
| Lucky for NSM — Extracting files from TFTP packets in Wireshark [tssci security] Posted: 05 May 2008 11:29 PM CDT So the other day I get a call from the forensics team at work asking for help with some packet analysis. A client’s users had reported phishing activity, so they decided to run a full-content capture using Wireshark on the external and internal network interfaces. Upon doing so, they witnessed suspicious activity; commands such as cmd.exe were triggering alerts on their Snort sensors as well. Oh boy… After the attack was contained, the client’s internal security team had reconstructed the attack and learned that the attacker had compromised a server, downloaded tools to C:\Windows\system32\, including Foundstone’s SuperScan and Sysinternal’s PsExec, and then uploaded three RAR files via TFTP. My goal: see what was in those RAR files. Whether it be intellectual property, client information, etc, the most important task was to identify the sensitivity of the data inside. I opened the raw capture in Wireshark and identified the three TFTP streams. I thought I would right-click and select “Follow UDP Stream,” then save the raw data as a RAR file. Unfortunately, when I did this, I could then not extract the contents of the archive. Looking for an alternative, Landon pointed me to tcpxtract (as detailed on Bejtlich’s blog), which at the time sounded good, but I couldn’t get it to compile under Cygwin and I wanted to get this done quickly. Oh well, with a name like tcpxtract, can it even handle UDP streams? So, looking at the packets again, there were only about 20 per stream, I decided to do this task manually. Who knew if it would work, but I gave it a try. I manually selected each individual TFTP Data Packet (not acknowledgments!) and selected the TFTP Data portion which began at the 47th byte in the packet. I did a Ctrl-H (or select File > Export > Selected Packet Bytes) and saved as block01, block02, block03 for each packet in the stream. I then cat all the files and redirected stdout to file01.rar like so:
I opened the RAR file and extracted the contents without a problem. I admit I was a bit excited at this point, interested to see its contents. I later spoke with Richard about this, who pointed me to a blog post from last year about TFTPgrab. Remembering this post now, I find it interesting that there was no way to rebuild files transferred through TFTP before TFTPgrab. Yet, I successfully managed to do so here. Anyways, here are some lessons learned. The attacker was sloppy, amateur at best. To call it amateur would be an insult to amateurs everywhere. For the client, it was sheer luck they ran a full-content capture at the moment of the intrusion and our adversary used a non-encrypted medium to transfer data. Had he encrypted his files or used an SSL tunnel, we wouldn’t have anything. Not to mention, if this is the kind of stuff that gets picked up during a random packet capture, who knows what kinds of malicious activity they have been or are currently subject to. Even more so, why are companies not doing egress filtering of traffic? TFTP should have been blocked at the firewall no ifs, ands or buts. One last lesson. When you outsource IDS monitoring activities to an MSSP (who probably has one or two analysts per 30-35 clients like yourself), attacks against you will not be treated with the same diligence you would expect of your own staff. They just don’t care as much as you do. |
| Security First, Requirements Later [Liquidmatrix Security Digest] Posted: 05 May 2008 09:15 PM CDT  I find it interesting to watch the mad rush to beef up security at the US border points without any real thought to requirements. Sure, keep out the baddies. But, how exactly? There is the constantly escalating method or there could some semblance of a plan? From IDG Norway:
So, by running in circles waving our hands in the air are we providing better security? Or have we played into the ne’er do wells hands? |
| OK, So, Now What Yahoo? [Liquidmatrix Security Digest] Posted: 05 May 2008 08:10 PM CDT  OK, so the date has ended. Microsoft didn’t get to second base. Yahoo was jilted for being too high maintenance and their stock dropped 15% today. So, what now for Yahoo? From Internet News:
Read on. |
| Suggested Blog Reading - Monday May 5th, 2008 [Andrew Hay] Posted: 05 May 2008 07:52 PM CDT
Here is the list: Virtual server sprawl highlights security concerns - This is a security risk that management really needs to be made aware of.
Interpol: Olympics cyberattack not a major threat - I’m still not convinced. I think that the Olympics would be a prime political target to make a statement.
The Hunt for the Kill Switch - How scary is the thought of this?
88,000 Patients at Risk After Computer Theft - Tsk, Tsk…should have protected the data better.
Radio Free Europe hit by DDoS attack - Ironic that a CIA sponsored project, started to prevent the spread of Communism during the cold war, wasn’t better prepared to deal with an attack.
UCSF Patient Information Available Online - Tsk, tsk again.
Botnet attacks military systems - I wonder just how much spam you would have to receive before you considered it an “attack”? I get around 300-400 per day right now
Stepped Up Cyber Role for Spy Agencies - I suspect that this has been going on for years but the government is probably making it public as a token offering to show their “commitment to fighting the great cyber threat”.
Cubans able to shop for PCs - Good for residents of Cuba. I’m glad to see that things are starting to turn around down there.
China mounts cyber attacks on Indian sites - I’d be interested to see the logs and traffic to determine their capabilities and attack vectors.
|
| Online Fraud: Start with the "Why" [Online Identity and Trust] Posted: 05 May 2008 05:37 PM CDT By Yohai Einav, Senior Fraud Analyst
But Kipling knew something about the 6 W's, something that we, in the security industry, often forget: starting with the "Why."
Well, fraudsters constantly look for new hacks in banks' security, and once they find one they attack with full force (by the way, when I say "hack" I don't necessarily mean technological hack, but a "hack" in the bank's security procedures). This means that if you see your bank has a sudden increase in phishing attacks - start looking for loopholes in the bank's perimeter security.
|
| Another new blog over at NSS Labs [tssci security] Posted: 05 May 2008 05:32 PM CDT Not to be outdone by Neohapsis Labs, NSS Labs also enters the fray with their blog, Security Product Testing. Again, I think that NSS Labs (like Neohapsis Labs) has been blogging for awhile, but it has picked up more pace lately. In the past, the TS/SCI Security blog staff were invited as guests by Martin McKeay for the Network Security Podcast. Rick Moy of NSS Labs got the opportunity to speak his mind with Martin while at the RSA Conference. Rick was additionally interviewed by the Bank Information Security Podcasts on Product Testing. Both of these might be worth a listen for the discerning security professional. Last week, NSS Labs approved the Radware DefensePro 1020 for attack mitigation purposes. They claim that, “The DefensePro 1020 blocked 100 percent of attacks while passing 100 percent of legitimate traffic without need for user intervention”. I really like what NSS Labs wrote on Security Products & PCI Compliance, where they state that:
We’re hoping to see/hear more from NSS Labs in the future! |
| Information-Centric Security Tip: Know Your Users and Infrastructure [securosis.com] Posted: 05 May 2008 04:51 PM CDT I was on a client reference today learning about someone’s DLP deployment, and it highlighted one of the biggest issues we often face when moving to an information-centric model. No, it’s not a failure of content analysis techniques, data classification, or over-hyped tools, it’s that we often don’t even know who owns what, who’s supposed to have access to what, or our own infrastructure. I often start my data security/information-centric rants by mentioning you need to have good identity management in place, but I don’t normally spend a whole lot of time talking about the details. The truth is, this comes up all the time when I’m talking with end users who are implementing this stuff. Oftenthey don’t have a good directory infrastructure, or one that reflects the org chart, and thus they can’t do everything they want with their DLP, DAM, or other tools. Sometimes they don’t even know where all their assets/servers are, or how to access them for scanning. Thus the tip- if you have a good directory infrastructure that accurately reflects your organizational structure, you’ll be in much better shape for any of these projects. Many of these tools can directly integrate with AD/LDAP, allowing you to build role-based policies. You can’t inform someone’s manager they’re sending customer lists home or running weird DB queries if you don’t know who they work for. |
| Dirty secret #2 - the perimeter is dead! [Data Protection, Management and Leakage] Posted: 05 May 2008 11:51 AM CDT Just came across an interesting article in Network World on the dirty secrets of security vendors. While I agree with some, disagree with a few, it was #2 that caught my eye. The author, Joshua Corman, claims, "There is no perimeter". Paraphrasing him - Vendors say that the network perimeter must be defended, but most data that is actually lost doesn't go through the firewall. Half of all breaches are the result of either lost laptops or lost thumb drives or other removable media. Businesses need to tighten up their business processes at least as much as they need to tighten up network perimeters, he says. "If you still believe in perimeters, you may as well believe in Santa Claus," he says. Not sure I believe in Santa Claus, but that's not the reason I agree with Mr Corman. I do believe that a data-centric or information-centric approach to security is the right one. Protecting devices, ports, networks, perimeters might become a thing of the past. Security vendors will evolve towards offering protection at the data level.. When? Now that's a completely separate discussion, though some are further along in reaching this goal than others.... |
| Cyberwar: PRC vs. India? [The Dark Visitor] Posted: 05 May 2008 11:14 AM CDT Someone passed on an article on the Times of India website this morning regarding ongoing attacks from the PRC to various government and private entities in India. From the article:
The article is short on technical details but is interesting anyway. Comments (especially from Indian readers) welcome. Article link. |
| Hiring Fraudsters? [Emergent Chaos] Posted: 05 May 2008 11:00 AM CDT  PARIS — Jérôme Kerviel, the Société Générale trader who used his knowledge of the French bank’s electronic risk controls to conceal billions in unauthorized bets, has a new job — at a computer consulting firm.First let me say that I'm fond of the phrase "paid his debt to society." It's out of fashion, but it used to mean that someone, after their sentence was carried out, was done. That they ought to be allowed to get on with their lives. I've publicly commented on Frank Abagnale being in this class. Kerviel clearly understands how to get around IT controls. I expect that there's a great deal which he might be able to teach people about what's important in security design, and some about what isn't. (His ability to generalize his approach hasn't been tested yet.) At the same time, he hasn't yet been tried for his actions. What would be the right framework for making a hiring decision like this? Photo: REUTERS/Benoit Tessier |
| Interesting Bits - May 5th, 2008 [Infosec Ramblings] Posted: 05 May 2008 09:03 AM CDT Well, I didn’t check my feeds this weekend, so we have quite the list of interesting bits to check out today. Happy reading. » Product Maturation and your business Vuze, TCP RSTs, and Educated Guesswork · Security to the Core | Arbor Networks Security IT Security: The view from here: A position of power Don’t even bother investing in Network Admission Control | NetworkWorld.com Community WhiteHat Luncheon | Infosec Events React Faster, And Better, With The A B Cs | securosis.com StillSecure, After All These Years: Stiennon says NAC is dead - I must be in heaven! Security4all: What is Black PR? A tour of the black arts. IT Security: The view from here: Encryption does what? Credit card thieves target small merchants, flawed POS systems, study finds Robert Penz Blog » Insecurity of Virtual Appliances and some thoughts on 7-zip compression Rational Survivability: Welcome To the Information Survivability/Sustainability/Centricity Circus… Rational Survivability: Asset Focused, Not Auditor Focused 1 Raindrop: GRC - To Be or To Do Rational Survivability: The Five Laws Of Virtualization - Not Immutable Any More? JJ’s Security Uncorked - Security Uncorked - 802.1X Terminology- Port ‘Closed’ JJ’s Security Uncorked - Security Uncorked - Layered Security: Solving the Cube Security4all: Website Security Strategies that work JJ’s Security Uncorked - Security Uncorked - Grasping Security thru Visualization Rory.Blog: Are we Secure yet? (Part 1) Live Mesh - Good or Bad Idea? | GNUCITIZEN Digital Soapbox - Security, Risk & Data Protection Blog: Airport Security: Should This Worry Me? Airport evacuated!! Found handgrenade in luggage! | Roer.Com Information Security Proposed SEC Rules Broaden Scope of InfoSec Compliance Responsibilities | BlogInfoSec.com PortSwigger.net - web application security: Null byte attacks are alive and well Computerworld - Do you have what it takes to be a converged CSO? RSA president shares risk management secrets - News - SC Magazine Australia Have a great day! Kevin  |
| Desparate for attendees [Network Security Blog] Posted: 05 May 2008 08:48 AM CDT I’ve attended my fair share of conventions, but this is a first: CTST 2008 is offering up a free night’s stay if you’ll attend their conference. Their event is next week and I’m pretty sure the offer isn’t transferable, but I find it very interesting that they feel like they need attendees badly enough that they’re willing to make this offer at all. Add this to the fact that my name showed up on the list of last year’s attendees and I think we have a convention that’s truly suffering and may not make the 2009 season. I receive a lot of phone calls from vendors, but in general only from vendors who have access to the lists of events I’ve actually attended. This year I’m showing up on the list of people who attended CTST, despite the fact that I’ve never attended and have never been to Florida, where the event is held. It makes me wonder how much of the list of attendees is based on people who actually attended last year or if it’s based on the people who were invited. I may be a statistical outrider, but from what I know of the convention biz, I also won’t be surprised if I find out I’m not the only one. CTST looks like a convention I’d be interested in; it’s all about payment cards and the ways in which different credit and debit cards can be secured. It’s a natural fit for just about anyone in the PCI arena. But right now I don’t have the time to attend, nor the energy to fly cross country even if I did. But listing me as an attendee for something I never showed up at is annoying, and if it happens again this year, I’m going to be more than annoyed; I might have to blog about it in an snarky, sarcastic manner. |
| Chinese Hackers Attack Indian Sites [Liquidmatrix Security Digest] Posted: 05 May 2008 08:37 AM CDT  The Chinese army’s hackers continue to grab headlines. From The Times of India:
Now I would have chalked this up to media FUD at one point. With every passing day it appears that this is in fact more real than I thought. Don’t get me wrong. I’m not naive enough to think that it doesn’t happen. I just thought that Bush and Co. were using China in an attempt to divert attention from their own failings as an administration. |
| Security Briefing: May 5th [Liquidmatrix Security Digest] Posted: 05 May 2008 07:24 AM CDT  Monday of my last week at work. I can see that the realization is beginning to set in with my co-workers. Well, I hope that I can share all I can before I’m off to carousel. I’d also like to say thanks to the folks who discovered the “donate” button on the next column over to the right. We really appreciate the donations! And now, the news…
Click here to subscribe to Liquidmatrix Security Digest! Tags: News, Daily Links, Security Blog, Information Security, Security News |
| BaySec Wednesday, May 7th [NP-Incomplete] Posted: 04 May 2008 11:50 PM CDT BaySec is this Wednesday, May 7th at Pete's Tavern. As usual, you can find us by looking for the crowd of socially inept nerds to the left side of the bar. |
| Personal Data Anyone? [Liquidmatrix Security Digest] Posted: 04 May 2008 07:51 PM CDT 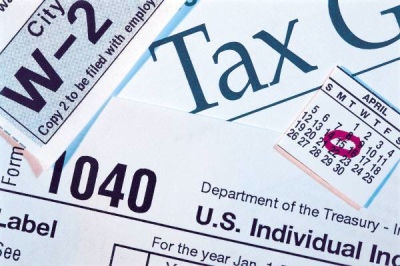 Morning mail call. I may already be a winner, check. $10,000 from Publishers Clearing House, indeed. Ah, tax forms…with the social security number on the label. WTF? From Tulsa World:
Sloooowly things improve. Yet, still not fast enough. |
| New Security Tools [Infosec Events] Posted: 04 May 2008 03:02 PM CDT Over the last week, here are some of the new security tools released.
While there are other sites that track tools on a daily basis, these are tools that I actually use. Is this list of any use to you? Would you like to see this on a weekly basis or not at all? |
| Spending to Protect Assets [Emergent Chaos] Posted: 04 May 2008 01:02 PM CDT  There's a story in the New York Times about a bike rental program in Washington DC. It's targeted at residents, not tourists, and has a subscription-based model. There's a story in the New York Times about a bike rental program in Washington DC. It's targeted at residents, not tourists, and has a subscription-based model. Improved technology allows programs to better protect bicycles. In Washington, SmartBike subscribers who keep bicycles longer than the three-hour maximum will receive demerits and could eventually lose renting privileges. Bicycles gone for more than 48 hours will be deemed lost, with the last user charged a $200 replacement fee.$4,500 is 22.5 bikes. Put another way, they could buy 2,500 bikes, rather than the 120 they're buying. That would require a lot more space if you bought them all at once, but you might just buy them as bikes are stolen. Looking at it another way, if you took the $500,000 being spent on technology, and invested it at 5%, you would make $25,000 per year, enough to completely replace the fleet annually. This is (obviously) an incomplete analysis. But the cost of protection jumped out at me. Maybe it's typical for how people in Washington think about asset protection. |
| Spam is now 30. [NP-Incomplete] Posted: 04 May 2008 01:17 AM CDT |
| You are subscribed to email updates from Security Bloggers Network To stop receiving these emails, you may unsubscribe now. | Email Delivery powered by FeedBurner |
| Inbox too full? | |
| If you prefer to unsubscribe via postal mail, write to: Security Bloggers Network, c/o FeedBurner, 20 W Kinzie, 9th Floor, Chicago IL USA 60610 | |
 I went and played my first round of golf yesterday…and boy am I sore. I probably won’t be posting a SBR next weekend as I’ll be busy at
I went and played my first round of golf yesterday…and boy am I sore. I probably won’t be posting a SBR next weekend as I’ll be busy at 

No comments:
Post a Comment