Spliced feed for Security Bloggers Network |
| Business Continuity and Disaster Recovery in a Time of War [Andrew Hay] Posted: 13 Aug 2008 07:23 AM CDT
Can we, as information security practitioners, really hope to build a business continuity plan (BCP) that would allow us to keep our business running in a time of war? How could you plan to move operations to a cold/warm/hot site if its located in the same town/city/country/region? Could you draft a disaster recovery (DR) plan to ensure the restoration of your business operations? What makes you think that you’ll be able to get the hardware/software/people/location/internet/power needed to get your business back up in a timely manner? I know most will argue that keeping your business going in a time of war is very low on the priority list and that human life is a greater concern. I completely agree. The fact is, however, that business continuity is a requirement of business operations and we must, during our risk exercises, plan for the worst case scenario. I think that war is really the worst case scenario but I have yet to see a BCP/DR that has a section on “Dealing with Armed Conflict“. |
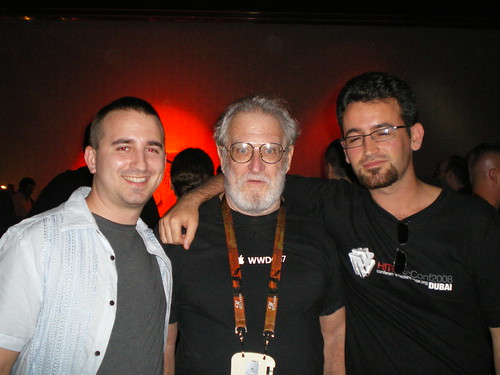
| Posted: 13 Aug 2008 01:19 AM CDT Defcon 16 was awesome! I’d like to congratulate Dark Tangent and all the Defcon goons for such an awesome event. This year somehow I managed to meet more people, attend more parties and see more presentations than during previous years. I had the pleasure to meet other fellow researchers for the first time such as Nathan McFeters, Billy (BK) Rios, RSnake, id and many others! All of them are security warriors whose research I was familiar with, but had never met in person. It’s always nice to put a face to a name! Although meeting the aforementioned individuals was of course a pleasure as I enjoyed having a nice chat with all of them, perhaps the most special and unexpected encounter was running into Captain Crunch! In short, while chilling at the freak show party, I saw an elderly gentleman who appeared to be having a great time at the dance floor. This gentleman called my attention as he appeared to never run out of energy despite his active dancing activity. Eventually, I started noticing his resemblance with Captain Crunch. So I told my wife: you know, it’s funny, but there is this man on the dance floor who looks a lot like a big icon from the early history of hacking: captain crunch. My wife was familiar with such legend of the hacker culture thanks to having seen The Secret History of Hacking and kind of agreed with me regarding his resemblance with Captain Crunch. To me it was kind of surreal to find Captain Crunch raving at a Defcon party. Eventually I approached him and said: excuse me, have you ever been told that you look like Captain Crunch?. And he goes like: I am Captain Crunch! Amazing, I guess anything is possible at Defcon! Also, I got to hangout with several friends including pdp which is great. Regarding presentations, I saw quite a few, some more relevant to my profession as a pentester than others. My favorites were Time-Based Blind SQL Injection using heavy queries, Sniffing Cable Modems and The World of Pager Sniffing. All of them really fun talks! Finally, I really enjoyed the showing of the original Wargames movie for its 25th anniversary. Not only is Wargames one of my favorite (and perhaps more accurate) hacker movies, but David Scott Lewis - a.k.a. Lightman - was there himself to answer questions made by DT and anyone in the audience. For those who don’t know who David Scott Lewis is, he was the model for Matthew Broderick’s character in the movie Wargames. PS: excuse my sleepy face in the picture! |
| My Karma Just Ran Over Your Dogma... [Rational Survivability] Posted: 12 Aug 2008 11:57 PM CDT From AndyITGuy who summed it up perfectly: Per the article above "Now he's one of the first victims of such an attack. Yeah, real funny. /Hoff * There's lots of thrashing going on as to the veracity of HD's quote rearding being owned. Regardless of the theatrics involved, it's interesting food for thought when the result of exploit research might be turned against the researcher... |
| Further Reflection On Virtualizing Security Appliances... [Rational Survivability] Posted: 12 Aug 2008 11:21 PM CDT
In my session I discussed some detailed scenarios of the architectural adjustments to infrastructure that virtualizing physical security appliances require and what that means to the overall resiliency, Specifically, I highlighted some of the limitations of using security virtual appliances and demonstrated how relying upon virtual security appliances can actually decrease the security posture and increase risk in our environments today. One of my examples illustrated how it may become necessary to combine multiple security virtual appliances on a cluster separate from the VM's they are protecting in order to achieve the availability, performance, scalability, and resiliency that we get out of dedicated in-line physical appliances today. If you prefer a simpler example, I also presented the simpler example of a firewall virtual appliance front-ending 10 production VM's. I like the former because it directly contrasts the physical and completely virtual. For the sake of illustrating a point, imagine if one were actually able to satisfy business, security and compliance requirements using this virtualized security architecture in a production environment built upon the same virtualization platform as non-security guests.* Not to pick on my friends at VMware, but today's license timebomb issue delivered by a VMware patch is pretty nasty and sends my hackles skyward when contemplating what it would mean were one to virtualize the security infrastructure. Basically, this issue caused by an update rendered certain VMs unusable after the update. If one or more VM's on an updated host happened to be a security appliance or security control taken down for patching or rotated for re-purposing, etc. imagine your surprise post-patch. Remember that security applications are very topology and state-sensitive and unlike other apps. that just care about an IP address with which to spew packets ethereally, security appliances/applications need to bind access policies with affinity in order to protect assets behind them. As we all know, when something doesn't work, we invoke the SysAdmin prime directive: "Blame the firewall!" ;) Events such as this may cause some to give pause to enterprise security architects before migrating security functions to virtual appliances, especially given where we are today with what I presented in terms of high-availability options within single-cluster hosts with virtual security appliances. In reality, it will probably cause people to consider what virtualization means as an overall contributor to operational risk for any physical system conversion -- regardless of vendor -- since any VA/VM would be affected, but let's think about this as if one had virtualized the security infrastructure. While it's true that for guests we have DR options and snapshotting that would make roll backs an easy affair, this shines a spotlight on the difficulties with patching the underlying virtualization platform and what that means to operational resilience. The notion of a homogeneous virtualization platform are certainly compelling; easier administration, patching, configuration, standardization, reduced costs, etc. However, the notion of a monoculture "operating system" has its downfalls also. This issue clearly highlights one of them. I'm not suggesting that there are not opportunities for virtualizing certain security functions, but as I pointed out in my talk, many of the required topologies and high-availability options present in mature physical security appliances are not available in the virtual appliance world. Today's issue highlights the need for very careful planning when comes to what, when and if one should When in doubt, refer to Hoff's Corollary: /Hoff * You might want to look at what a platform like the Crossbeam X-Series can give you that "normal" virtualization security platforms cannot, as it mitigates some of the issues mentioned in my talk. ** Of relevance is my blog post from back in January titled "On Patch Tuesdays For Virtualization Platforms" |
| Network Security Podcast, Episode 115 [Network Security Blog] Posted: 12 Aug 2008 08:12 PM CDT Rich and I are both back from a week at Black Hat/Defcon and thankful to be home in one piece. While the event is a ton of fun and educational, it’s also physically and emotionally exhausting. Tonight we talk about some of the talks we attended, what we learned, both in and out of the talks. Dan Kaminsky’s talk on DNS was probably the biggest talk at both events, but there was still a ton of other talks worth attending. There’s still a couple more microcasts to come out of the events. Please let us know how you like those and if there’s anything we can do to make them better in the future. Show Notes:
Network Security Podcast, Episode 115, August 12, 2008 This posting includes an audio/video/photo media file: Download Now |
| Posted: 12 Aug 2008 05:21 PM CDT Alright. If you have been following the Full-disclosure mailing list, you have probably stumbled across several emails which claim that one of my GMail accounts have been compromised. That is right. It did happen but I am not that surprised since I’ve been expecting it after being unsuccessfully attacked for so many times during the last 3 years. It is interesting to me that shady characters from across the Net see me as a quite important person although I would say otherwise. Why I am not pissed? Ever since I’ve stepped in the position of a public figure with the GNUCITIZEN blog and the numerous speaking engagements and other things around those, I have never hidden any information regarding my work and personal life. I have always tried to be honest with you about the things I do and care about. As a side note: I realize it it impossible to satisfy everyone in the community, so those of you, who have some personal issues regarding the blogs I write, can simply stop following my work. The posted details are not a threat to me as they are very much outdated and irrelevant. I am quite surprised that from all the information out there, my private life is considered as the most valuable and interesting one. I would say that it is as useful as some tabloid junk. Funny enough only the name of my wife is correct :) sort off. I would also like to thank the attackers for putting me on the spotlight. As people say, every crisis is an opportunity and I will take it as such. Now is better time then ever to raise some serious questions to the information security community and our industry in general. The problems in the Information Technology field are many and this particular case is a living proof for that. It is not a problem that my GMail inbox has been compromised. It is a problem that this can happen to anyone. Even doctors can catch viruses, right? I have never seen a network, application or website that did not surrender after persistent poking. I’ve always said that hacking is not about skill set. It is mostly about dedication, patience and a lot of motivation. These elements speak a lot about the personal characteristics of the attacker. Tackling today’s e-crime industry is a very, very hard challenge because it is not knowledge of technology that is the problem but our human nature which is easily corruptible by less controllable factors in our societies. Here is the time to state that I am taking a full responsibility of what has happened and I am going to fully collaborate with the legal authorities regarding this matter. I was ensured that the problem can be easily resolved, since the attackers made many amateurs mistakes. I will let you know more as soon as I get an official confirmation. In the meanwhile, I hope that everyone had as good time at Black Hat and Defcon as I had. Adrian has prepared a smoking post coming next and I will upload my updated slides soon. |
| Getting lock picks home [Network Security Blog] Posted: 12 Aug 2008 03:32 PM CDT One of the things I picked up at Shmoocon 2007 was some lock pics. I’ve played with them some, but really the set I picked up at Shmoo was too small and I wanted a bigger set to play with. So when I found out that they weren’t going to charge for the press passes at Defcon this year, I spent most of the money on a really nice set of picks from Southern Ordanance. That only left me with one minor problem: how to get them home. Ax0n has a nice article on how he got his picks home, but my solution was even simpler. The central post on my tripod lost the bottom plug and all of the picks fit easily within. A piece of duct tape over the bottom of the post and I was done. When I got home, all I had to do was take the tape off and they came right out. I did have to rely on the TSA not noticing the pick case, but seeing how it’s just a case with a small bar of metal in it, I wasn’t too worried, and rightly so. I rested the leather case on top of the tripod and they never even questioned it. I did have my bags re-scanned several times on the way home, but the tripod and the picks it contained didn’t get a second glance. For whatever reason the TSA did feel like checking out the dirty laundry in my checked luggage, but if that’s what makes them happy, more power to them. That’s why I almost never check luggage anyways. |
| A clash of cultures [Phillip Hallam-Baker's Web Security Blog] Posted: 12 Aug 2008 02:07 PM CDT Readers of this blog are probably aware that lawyers for the MBTA recently obtained an injunction to prevent two MIT students presenting a security analysis of the MBTA 'Charlie Card' payment scheme at Black Hat.
|
| Podcasters Meetup at Defcon [Network Security Blog] Posted: 12 Aug 2008 12:08 PM CDT The video of the Podcasters Meetup at Defcon is up and you can watch us in our full glory. Be warned, we had Dragnet Driftnet playing on a computer projected on the wall behind us and the images were graphic at time. Not that you can see it, but don’t watch it if you’re easily offended. The podcast officially begins at about 10 minutes and unluckily the computer hosting the video died at about 45 minutes. The podcasts represented were Sploitcast, Securibit, Pauldotcom and Security Justice. Thanks a ton to the sponsors (escpecially i-hacked.com) and thanks to Mubix for setting this whole thing up. And if you are wondering what that stuff on my face is, I went to the IOActive/StillSecure Freakshow before the meetup and had my face painted tribal style. No, Mike Tyson and I were not separated at birth! (thanks Byte_bucket) |
| That's an address I haven't used in a very long time. [Emergent Chaos] Posted: 12 Aug 2008 11:41 AM CDT Well, I got a letter from BNY Mellon, explaining that they lost my data. The most interesting thing about it, I think, is where it was sent, which is to my mom. (Hi Mom!) I had thought that I'd moved all of my financial statements to an address of my own more than a decade ago. I've been meaning to call BNY and ask questions, but haven't had time. The letter is dated June 9, regarding a February 27th loss by Archive Systems, Inc. The three-plus month delay annoys me. Archive Systems isn't named in the letter. I had to look at Data breach at New York bank possibly affecting hundreds of thousands of CT consumers to discover that. The signup experience for the "Triple Alert Monitoring" from Experian was not awful, but it was pretty poor. It demanded lots of personal information, wasn't clear how it was going to be used. Experian stuffed a long terms and conditions into a three line at a time scroll box, clearly indicating that they don't expect anyone to read it. Their web site silently relied on Javascript, and it wasn't at all clear how long I'm enrolled for. I have little doubt I'll start getting renewal notices in three months. Incidentally, I've Been Mugged has a review of Triple Alert. |
| Posted: 12 Aug 2008 10:48 AM CDT Over the years I have typically seen metrics that mean something to the network/IA staff but not to senior management. When these metrics are given to C-Level executives they glass over and don’t really understand what they are being told. They rapidly try to figure out if a larger or smaller number is bad so they can attempt to put what they are given in some sort of context. The problem is that they become use to this and begin to rely on these numbers without really understanding what the numbers are really telling them. They think they understand but they don’t and as a result don’t give the priority to IA in the way they should if they really understood what they were being told. We, as IA professionals, become complacent with this arrangement because that is what we are use to and our executives appear to understand. We confuse acceptance for understanding. As IA professionals, we often only answer half of the question and totally forget about the business side of the equation. We need to understand our audience and frame our metrics in terms that they understand rather in terms that we understand. We need to find a way to both qualitatively and quantatively measure our success and translate that into business speak each and every time. Think about it this way - we can create the business case for what we do each and every time we generate metrics without having to continuously try to convince others. I believe it is important to measure what our management wants to see, it is equally important that we tell them what they need to measure. Now this may seem straightforward but I don’t just mean giving them answers to questions they haven’t asked and then trying to convince them that this information is important. What I mean is that we aim to provide the appropriate metrics with every project proposal we submit to management for funding. That would mean not just telling management that we want to be able to correlate and filter x number of log entries from y number of devices but that we want to be able to say reduce the number of false positive incidents by 25% resulting in a savings of z dollars per year by implementing a SEIM project. As with most of our IA duties, the qualitative nature of our job makes the development of useful metrics often difficult. Yes we can calculate the number of viruses our desktop AV catches a week but is that really meaningful in the long run? It may be if we can tie that number into a formula that calculates response, recovery, and lost productivity numbers per virus outbreak. I guess what I’m saying is that the actual measurement isn’t as important as constantly linking that information with figures that mean something to management. This is probably in line with Deming’s emphasis on controlling the process as it ties the process into terms that resonate in business terms. Thoughts? |
| WabiSabiLabi - Hacks for Sale? [Digital Soapbox - Security, Risk & Data Protection Blog] Posted: 12 Aug 2008 10:47 AM CDT A year or so back a site called WabiSabiLabi generated a lot of press and buzz when it announced that it would auction potentially zero-day vulnerabilities on an "open market" much like eBay. That being said there was some interesting press a little later where one of the co-founders [Roberto Preatoni] was arrested for some alleged spying on a Brazilian CEO. Lots of press, lots of buzz... then they flat-lined. Today, if you google "WabiSabiLabi" you get results that mostly date to 2007, and then you find many write-ups about this gem... a hardware-based UTM platform. I challenge you to find something relevant from those WabiSabiLabi folks, within the last few months... anything. I am probably among the majority when I say that an online marketplace for supposed 0-day vulnerabilities is a bad idea, as a concept. Obviously it's not flourishing quite as well as they had hoped, judging by the screen shot here - so what happened? Is there simply not a market for 0Day vulns?  I honestly don't know the answer to that question, but I suspect it lies somewhere between ethics and finances. Some have a hard time ethically with this idea, while others just don't feel like paying for vulnerability disclosure... at least publicly. Whatever the reason, it looks like this was an endeavor that never had any wind in their sails... too bad, so sad. |
| links for 2008-08-12 [delicious.com] [Andrew Hay] Posted: 12 Aug 2008 08:00 AM CDT |
| Defcon Microcast 10: Mike Murray and Lee Kushner [Network Security Blog] Posted: 12 Aug 2008 12:01 AM CDT Mike Murray and Lee Kushner have a lot of experience in helping people direct their careers in the security field and shared this experience at Defcon this year. They’d like your help by having you take an anonymous survey about your own career. The survey can be found at http://infosecleaders.com/survey. Defcon Microcast 10: Mike Murray and Lee Kushner This posting includes an audio/video/photo media file: Download Now |
| Who trusts any network at Black Hat? [Network Security Blog] Posted: 11 Aug 2008 10:31 PM CDT I almost felt a little silly at Black Hat and Defcon using my 3G card, even in the press room. But it turned out I had the right instinct: some ignorant psuedo-journalists decided they’d spend some time sniffing the network in the press room and tried to get the folks hosting the Wall of Sheep to include the journalists traffic on the Wall of Sheep. Not a good move, since the folks they went to just turned around and told the organizers of Black Hat. The guys doing the sniffing were summarily kicked out of Black Hat and told to never bother applying for a press pass to the event again. I call them psuedo-journalists because these guys apparently weren’t really journalists and weren’t really bloggers either. Instead they exist in a role somewhere between the two, sometimes blogging and sometimes writing pieces for serious magazines. I guess that places me in a very similar position, since I blog prolifically and occasionally write articles myself. One of the big differences between me and them is that I realize I’m acting as a bridge between the two communities and that what I do could have long term repercussions in how bloggers are treated at events like this in the future. My friend Michael Farnum points out that any journalists who are whining about this violation of the sancrosanct network in the press room are fools who should know that all networks need to be considered hostile. Well, that may not quite be the words he used, but I know Michael well enough to suspect that might be how he really feels. And he’s right to a certain degree, especially at Black Hat and Defcon. You usually have no way of knowing who’s listening on the network and need to act accordingly. When you’re sitting on a network that’s sometimes called the ‘most hostile network on earth’ you have no excuse for not taking the necessary precautions in the necessary to keep you safe. This probably isn’t the first time someone’s been sniffing on the journalist’s network, just the first time it’s been one of our own doing it. I no longer feel like a paranoid for limiting my use of the press room at Black Hat. I only visited the room once myself and never connected to the network. I used the network in the press room at Defcon a couple of times to upload podcasts and read my daily dose of online comics, but didn’t do any serious activities on it. Though now that I’m thinking back and reviewing Libsyn’s site, I’ve realized that the site doesn’t use https by default and needs to be forced into a secure mode. At least the site actually works using https. And I think I’ll be changing that password anyways now that I’m reflecting on it a bit more. All networks are hostile, something security professionals and journalists who follow security professionals can’t afford to forget. It’s only a little bit of egg on the face of some journalists, but it can be a lot more if you’re not careful. We tend to forget that it’s not just other people that get hacked, sometimes it’s us as well. |
| PaulDotCom Security Weekly - Episode 117 - August 10, 2008 [PaulDotCom] Posted: 11 Aug 2008 10:23 PM CDT Live from a hotel room in Boston and a hotel room in Las Vegas!
 Hosts: Larry "Uncle Larry" Pesce, Paul "PaulDotCom" Asadoorian Email: psw@pauldotcom.com |
| Posted: 11 Aug 2008 02:22 PM CDT What have you been up to this summer? Relaxing at the beach? Hosting a BBQ for friends? I have been traveling around the globe, talking to people about Network Access Control and network security in general. My next few posts will be a bit of a travelogue, a set of notes and observations and photos from my travels. Enjoy! Tags: General, general |
| Defcon Microcast 9: Johnny Long [Network Security Blog] Posted: 11 Aug 2008 01:24 PM CDT I chased down Johnny Long to his booth at Defcon and learned about his new project, Hackers for Charity. If you’ve got ‘l33t skillz’ and want to put them to use for a good cause while also getting some good references for your future job hunts, think about joining the Hackers for Charity organization. Or if you’ve got some skills that aren’t ‘hacker’ related and want to get into the security sphere, take a look at the site and see if you can contribute to Johnny’s efforts. Oh yeah, Johnny’s written a few books you might want to take a look at as well. Defcon Microcast 9: Johnny Long and Hackers for Charity This posting includes an audio/video/photo media file: Download Now |
| Davix: Suggestions [Security Data Visualization] Posted: 11 Aug 2008 11:48 AM CDT I have tried Davix. Impressed by an _excellent_ documentation to the specific DAVIX programs (needs a lot of time to read carefully - will do this later). Suggestions to a SLAX-based system: << I do not like the automatic activationg of all modules found by Slax, and prefer to activete only necessary ones myself (especially in the LiveCD model), but I do like to have such a possibility. As for me, a reverse lzm2deb will be fruitful:) It will also be great to add a file manager (e.g. Krusader). First seen in Linux: gedit in the KDE - _very_ nice! arK does not open 7z archives - needs To add a small IDE: smallbasic(.sf.net) - sbasic_fltk - less than a megabyte for one executable and dozens example programs. Others (GamBas for Basic; g95, gfortran for Fortran; Python; Lazarus/FreePascal - are much larger, so are to be installed separately, not in a LiveCD). These two programs will increase the memory usage not drastically even in a LiveCD mode. Another general possibility: to add a printer (e.g. I use HP DeskJet 520 on lpt), but it wants Internet for connection. With best wishes and thanks, |
| Watchlist Cleaning Law [Emergent Chaos] Posted: 11 Aug 2008 10:58 AM CDT (Dan Solove, "U.S. Government Finally Recognizes that Nelson Mandela Isn't a Terrorist.") I fully agree with what Dan says, and would extend it to creating, maintaining and using such lists. But I wanted to comment on something which struck me. The story says (accurately) that the law "gives the State Department and the Homeland Security Department the authority to waive restrictions," and also states the sense of Congress. Why doesn't the bill simply order the removal of all such people, and give them actionable rights if they aren't removed?Former South African President Nelson Mandela is to be removed from U.S. terrorism watch lists under a bill President Bush signed Tuesday... The bill gives the State Department and the Homeland Security Department the authority to waive restrictions against ANC members.This demonstrates that greater scrutiny must be placed on the decisions about who gets placed on terrorist watch lists and other government blacklists. It took a long time for Nelson Mandela to get off the list, and I wonder whether anybody who isn't of Mandela's stature stands a chance getting off the list. The story also raises questions about just who is designated a terrorist. There must be greater accountability in creating these lists. The bill is HR 5690. |
| SSAATY site compromised Sunday [Network Security Blog] Posted: 11 Aug 2008 09:38 AM CDT Update: It appears that Alan has regained control of his DNS. Hopefully more good news to follow. Yesterday morning the Still Secure After All These Years website was compromised and defaced. The attackers compromised Alan Shimel’s blog, posted personal information to a mailing list and have basically made some very hateful attacks on Alan as a person. This has not been a joke, it’s been a targeted attack on one person and it’s being treated as a serious event. Alan is in recovery mode and thanks to a number of contacts is in the process of recovering his blog, his DNS and other accounts that were also compromised. However, the DNS of his site was compromised for several hours and as of this writing the SSAATY DNS was still pointing to a site most of us would rather not visit and we do not know if the site hosts any malware. The DNS has been fixed, but as we all know, it can take days to propagate through the Internet. I’ve talked to Alan, he will be responding, but I can’t say when. He’s talking to the appropriate authorities, which may delay his response significantly. |
| Surf Jacking [un-excogitate.org] Posted: 11 Aug 2008 06:11 AM CDT Just finished reading about Surf Jacking from Ronald van den Heetkamp (and Sandro Gauci and Mike Perry), the demonstration movie that Sandro published really set in stone how interesting this vulnerability is. Sandro’s whitepaper describes the attack in detail, the primary attack scenario being the following:
The first thing I did after reading this paper was to check my online banking, and I was relieved to see that the session cookies sent by the server were set to “Encrypted Only”. |
| From the "Sucks To Be Me" Department... [Rational Survivability] Posted: 11 Aug 2008 03:04 AM CDT
Despite the positive feedback from folks, it seems the foreboding narrative of the apocalypse has carried over into the real world due to a rather unfortunate journalistic misinterpretation of the facts. It's only fair to state that I have been critical in the past of others in our line of work who have complained of their inability to control the output of their direct interviews with the press and analysts as misquotes and misunderstandings arise. Perhaps this is a little karmic payback for my outspokenness, as after my talk at Blackhat, I have now enjoyed the fruits of journalistic distortion firsthand. It's important to note that this was not the result of a direct interview, but rather the inaccurate reporting of a reporter sitting in the audience of my talk. I was never contacted with questions or asked for clarification or review. Many of the points I made in my presentation were reflected upon poorly and my perspective butchered, but one specific item is causing me some serious grief in a professional capacity. It cast a rather crappy pall on the rest of my Blackhat and Defcon experience (more on that later.) One of the "Four Horsemen" which represents a critical issue in virtualization security is that of the hidden costs involved in virtualizing security. The point I made, and the language I used to consistently describe it multiple times appears below: What Ellen Messmer reported in her Network World article was that I said "Virtualization will not save you money, it will cost you more." Now, this may not seem like much of a difference, but it's a profoundly impacting dissimilarity. It's a dangerous rephrase that has now caused significant pain for me that I'm going to have to deal with once I return from vacation. It's been picked up and re-printed/adapted so many times without validation that I can't keep count any longer. You see, I work as the security architect for the division of a company who is maniacally focused on designing, deploying and supporting heavily-virtualized realtime infrastructure for our customers. One of the (obvious) value propositions of virtualization/RTI is cost savings/reduction/avoidance which I specifically referenced during my presentation as a well-established fact and reasonable motivation for virtualization. You can probably imagine the surprise of folks when they read Ellen's article which is written in a way that directly contradicts our corporate messaging and the value proposition offered to our clients. It reflects rather poorly on me and my company. And just to be clear, my scorn was not directed at the "network industry" or the "virtualization industry" as reported in the article; the context of my entire talk was the security industry, a point sorely missed. This article reads like the output result of a bad game of "telephone." I intend to contact Ellen Messmer and ask for a retraction as well as corrections of multiple other mistakes in the article, but as we all know, there's no real retraction on the Internet. All I can offer is my presentation, the video recording of it and the recollection of the 500+ others that were in the audience when I presented (including numerous other reporters.) The only other thing left to do is to sheepishly admit that despite the fact that this was not an interview that I or anyone else could control or influence for correctness, Joanna Rutkowska was essentially correct in her assertion during our last debate that you cannot control the press, despite best efforts. Even though I've never had a problem of this degree in the almost 15 years of doing this sort of thing, I humbly submit to her on that point. /Hoff |
| Chinese hackers eating Chinese hackers…with a side of government [The Dark Visitor] Posted: 10 Aug 2008 06:48 PM CDT This is the official Chinese government website for Longgang Emergency Management: This is also the official Longgang Emergency Management website, when you add xiaozi.html: You would think, with the recent earthquake in Sichuan and the ongoing Olympics, that government websites dealing with emergency management would be inspected rather thoroughly. Not so much. Google spiders crawling the internet, show that the website has been hacked since at least 31 July 08. Is it unusual for a Chinese hacker to attack their own government’s website? The first-generation of Chinese hackers had very strict rules about not hacking inside China but the current crop doesn’t seem to adhere to the same code. Doing a pull on Zone-h.com.cn, gives 1,952 known Chinese government websites that have been hacked. A fairly large number of those attacks appear to be carried out by Chinese hackers. So, from the URL extension on the hacked page of the Longgang Emergency Management website, who or what is a xiaozi? It is a who, or to be more precise, a him. Meet Network Boy (Wanglu Xiaozi): Blog name: Network boy’s BLog Hacker Not to get in a battle over Zodiac signs but isn’t someone born on 13 December a Sagittarius? Maybe something to do with the Chinese Lunar Calendar but trying to figure it out hurts my head about as much as International Date Line conversion. I have Chinese friends I give birthday gifts to five times a year just to be on the safe side. Moving on. Going through Netboy’s website reveals that government websites are not his only target, he also has an affinity for fellow hacker websites as well. 1) First target, zgmuma.com (China’s Trojan Base): According to Netboy, he was bored and went to his favorite hacker site (hackol.com) to study but the website was down. He did notice a link toward the bottom of the page that connected to zgmuma.com and for reasons unmentioned decided to see if he could break into the site. Zgmuma.com is another Chinese hacker website that boasts the largest collection of online game trojans around. It also provides hacker training. I have to give Netboy credit, he provides a step-by-step account of his exploits, to include screen shots and the tools used to perform reconnaissance on the intended victim. With this one he was able to find a fatal flaw in the server to crack. While Netboy was breaking into zgmuma, his buddy, who goes by the name of Ice Sugar, contacted him to say that he had gained access to cnhacker.com and posted a hacked page: Ice Sugar passed over the info on cnhacker.com to Netboy, who said he also posted a hacked page on the site. 2) Second target, an81.cn (The Dark Hacker Group): Netboy was able to gain access to this website because they were using Dvbbs8.1. He was thankful that it was not 8.2, because then he would not have been able to gain access to the backstage shell. Using Thunder (unclear) he was able to discover the site admin’s password, 6423987, after making several manual guesses. He also used an ASP trojan during the process but I couldn’t begin to tell you what he was talking about; didn’t understand much of the technical jargon. 3) Third target, www.163???.com (Hacker) Netboy really liked the design of this website and consider it difficult to break but still managed. Once again, he takes you through his very methodical system of cracking the website and I wish I was able to translate it but can’t. Some of you people who are more on the tech side might be able to gather what he did even better than me by the screen shots. For whatever reason, he decided to hide the target’s URL but it only took about a minute to find the site, www.163xjs.com. Wasn’t able to access the site due to a “directory listing denied” message. However, Google’s cache was not so particular about who peeked: Even though the imagery is absent, it is clearly the same website. 4) Fourth target, hacker98.cn Lot of stuff on this hack too but I’m getting bored and you get the point. He hacks other Chinese hacker websites. Conclusion: At the end of each of these attacks, Netboy posts an invitation for other skilled people to join his group. So, this all may be just to gain recruits by proving he is better than the other groups out there. |
| Posted: 10 Aug 2008 09:51 AM CDT In a story initially written up [very completely] on Wired's Blog, a Federal Judge has essentially halted (via a temporary restraining order) a bunch of MIT students from giving their presentation on the MBTA [Massachusetts Bay Transit Authority] fare cards and the vulnerabilities associated with them. The article in Wired already writes the case up nicely, and even includes a link to the (now-public-domain) vulnerability report. Given all the number of magnetic swipe cards out there for various things and the recent cases rash of "hack the card" incidents [Oyster card case, many others] there are several lessons-learned here that I think apply to every one of these cases.
Lesson-learned here, although I suspect we'll still keep seeing this stupidity in the future, is think things through and don't try and take the simple implementation - because you'll be very upset when it gets hacked and it'll be all your own damn fault. As a side note, NXP is at fault for more than one of these gaffs in security... think that through... shouldn't the MBTA be suing NXP? BTW: *great* editorial piece on this topic here [BorePatch]. |
| Black Hat Microcast 8: Raffael Marty [Network Security Blog] Posted: 09 Aug 2008 12:04 PM CDT Raffael Marty and I sat down in a quiet corridor at Defcon to talk for a few minutes about his new book, Applied Security Visualization. Black Hat Microcast 8: Raffael Marty This posting includes an audio/video/photo media file: Download Now |
| Black Hat Microcast 7 - Nate McFeters and Rob Carter [Network Security Blog] Posted: 09 Aug 2008 11:54 AM CDT Rich caught up with Nate and Rob right after their talk at Black Hat on client side exploitation. Black Hat Microcast 7: Nate McFeters and Rob Carter This posting includes an audio/video/photo media file: Download Now |
| This Is Not Writing; You Are Not Reading [Emergent Chaos] Posted: 09 Aug 2008 03:57 AM CDT The Paper of Record has a hilarious article, "Literacy Debate: Online, R U Really Reading?" which asks important questions about what Those Darn Kids are doing -- spending their time using a mixture of hot media and cold media delivered to them over the internets. I'll get right to the point before I start ridiculing the ridiculous, and answer the question. No. Of course not. It's not really reading. This is not text. It is not the product of hot lead type lovingly smearing a mix of kerosene and soot over wood pulp. It's a bunch of pixels, and those pixels are whispering directly into your brain. You are not reading, you're hearing my snarky voice directly massaging your neurons. That doesn't happen when you read. People don't see things or hear things when they read. Ask Anne Fadiman if you don't believe me. She knows. Let's look at some of the statements in the article: Few who believe in the potential of the Web deny the value of books. But they argue that it is unrealistic to expect all children to read "To Kill a Mockingbird" or "Pride and Prejudice" for fun. It is unrealistic to expect any children to read Austen. Austen is arguably the second best writer in all of English, but she requires emotional experiences that children do not have. Pride and Prejudice is no more children's reading than 1984 is. Trust me on this, I know. I read 1984 when I was ten, and when I re-read it in college, I was gobsmacked to learn that there is sex in it. Some traditionalists warn that digital reading is the intellectual equivalent of empty calories. Often, they argue, writers on the Internet employ a cryptic argot that vexes teachers and parents. Zigzagging through a cornucopia of words, pictures, video and sounds, they say, distracts more than strengthens readers. They said pretty much the same about Dickens. Until relatively recently, no serious scholar of literature (read college professor) would admit to reading Dickens. Personally, I agree. These days he's considered a classic, and the non-serious scholars won't admit to reading him. Last fall the National Endowment for the Arts issued a sobering report linking flat or declining national reading test scores among teenagers with the slump in the proportion of adolescents who said they read for fun. And of course we can fix this by denigrating what they do read, as opposed to finding things for them worth reading. "Whatever the benefits of newer electronic media," Dana Gioia, the chairman of the N.E.A., wrote in the report's introduction, "they provide no measurable substitute for the intellectual and personal development initiated and sustained by frequent reading." I'll do my part. I resolve to start writing my blog posts, okay? Do you want them in printing or copperplate? [Synopsis: Nadia's mother tries to instill a love of books in Nadia. Nadia does not respond until they get a computer, when Nadia gives up TV for fanfic.] Which the masters of modern literature such as Pynchon and Joyce would never do. Austen never had elliptical plots, they were circular, and she was merely eccentric. Nadia said she wanted to major in English at college and someday hopes to be published. She does not see a problem with reading few books. "No one's ever said you should read more books to get into college," she said. And this is a problem? Reading skills are also valued by employers. A 2006 survey by the Conference Board, which conducts research for business leaders, found that nearly 90 percent of employers rated "reading comprehension" as "very important" for workers with bachelor's degrees. I don't know about you, but I wonder what sort of people the 10+% of employers are who think that reading comprehension is not very important. What sort of Dilbert-refugees are they? I find that "nearly 90%" to be disturbing. Some literacy experts say that reading itself should be redefined. Interpreting videos or pictures, they say, may be as important a skill as analyzing a novel or a poem. Ah, the word "may." I've ranted about it before. It is true that interpreting pictures may be as important as analyzing a novel. It certainly is if you want to appreciate El Greco. But that's not the point. As much as I like sneering at moderns who think Dickens is literature, times change. It may, indeed. Joyce may have written grammatically. Austen may be suitable for children. Reading comprehension may be important for workers with bachelor's degrees. And Shakespeare's works may have been written by another man of the same name. I am disdainful of hot media, but the Web is the rennaissance of cold media. It's an aberration in a slide to hotter and hotter media. Also realize that cold media is relatively recent. Most of human history had its literature in songs and pantomime. Lastly, remember that kids have been no damned good for as long as we've been writing at all. The pinnacle of civilization was when we were in the caves, and it's been a long slow slide into perdition ever since. Every generation is worse than the previous one. It will continue to be that way. These kids are going to sigh with exasperation and not understand why their kids roll their eyes at Sailor Moon. And they just not going to understand the true art form of fanfic and slashfic. Tsk. |
| Why Can't Hackers Spell? [Digital Soapbox - Security, Risk & Data Protection Blog] Posted: 09 Aug 2008 12:33 AM CDT Seriously? Why? If you haven't been keeping score, the 'hackers' who set of various viruses, worms and other malware over the past several years just can't seem to spell right, and clearly don't have any regard for proper grammar... As I was reading about this latest FaceBook "worm"... I came across an article on TechCrunch that details some of the messages being left on the "wall" of hacked users. The messages are hillarious.. ."LOL. You've been catched on hidden cam, yo"Who writes like that? This isn't the first time, and definitely won't be the last time some [presumably foreign] hackers have had incredibly poor grammar and spelling... oh well. |
| You are subscribed to email updates from Security Bloggers Network To stop receiving these emails, you may unsubscribe now. | Email Delivery powered by FeedBurner |
| Inbox too full? | |
| If you prefer to unsubscribe via postal mail, write to: Security Bloggers Network, c/o FeedBurner, 20 W Kinzie, 9th Floor, Chicago IL USA 60610 | |


















No comments:
Post a Comment