Spliced feed for Security Bloggers Network |
| Why Cloud Security Matters [GNUCITIZEN] Posted: 09 Oct 2008 07:11 AM CDT I asked on LinkedIn what security professionals think about Cloud Security. The answer was as expected. Nobody really knew what I was talking about. Cloud security is different because the rules of the game are totally different. The recourses involved are totally different. Money is not an issue. I believe that anyone can afford $0.15 per month for 1TB of storage. Networking capabilities are not an issue. The cloud can be as big and as small as we want it to be. Visualizations and utility computing are the norm. In such a vivid and complex field, vision is what is most important. I will leave it up to you to decide what is cloud security and why it matters. If you are the sharing type of a person, drop your comments bellow. If you are looking for cloud computing services from a bunch of professionals with an interesting and vivid background, then get in touch with us. ---
--- More Advanced Clickjacking - UI Redress Attacks |
| Book Review: Fuzzing | Brute Force Vulnerability Discovery [Nicholson Security] Posted: 09 Oct 2008 01:24 AM CDT I really enjoyed reading Fuzzing. The book has a ton of really great information. The majority of the content I was interested in pertained to the application and web application fuzzing. The book starts with a background on vulnerability discovery methods. It then covers the different methods and types of fuzzer's. The good stuff starts in [...] |
| You can't just tell the board anything you want [StillSecure, After All These Years] Posted: 08 Oct 2008 11:35 PM CDT Came across an almost unbelievable story tonight. The title of the story was that 40 people were laid off at a software company. I figured it was going to be about the economy, but no. This one is crazy. Seems the CEO and CFO of Entellium decided that they were were going to tell the board that their revenue was 400k a month higher than it really was! Over time the revenue of the company was stated to be over 15 million, when it was just over 3 million. I know there are used car salesman type of companies that might overstate revenue to a reporter or analyst, but it takes some set of stones to lie to the board about it. Now Entellium is not a public company, so there was not public stockholder fraud. The fraud came into play when the investors including the well known Ignition Partners, claimed they would not have invested in the company had they known the real revenue numbers. It was based upon this claim that the charges were bought. But I ask myself, what kind of venture company would invest money and keep investing more money (they raised about 50m total), without some sort of audit of the books? We have yearly audits here at StillSecure. I can't imagine with raising that kind of money, no one asked for an audit. It just seems incredulous. I think before the dust settles on this one, we may find out that there was more here than meets the eye. I would not be surprised if someone was not turning a blind eye towards the revenue reports to facilitate an exit or something else. If that is the case, these two guys may be just the tip of the iceberg here! In the meantime, 40 more people are out of a job. Related articles by Zemanta |
| Where'd ya go - I miss you so [Donkey On A Waffle] Posted: 08 Oct 2008 10:26 PM CDT To quote a great song by the band Fort Minor: "Where'd ya go, I miss you so. Seems like it's been forever, since you've been gone". Well it hasn't quite been forever, but it has been nearly a month. I have all sorts of good reasons why I've been too busy to give you kind reader (note the intentional use of singular) the type of interesting infosec jibber jabber that you deserve... BUT.. I'm not going to tell you about them. Frankly it's none of your business. Instead I'm going to give you a pointer to an interesting piece of research journalism conducted by business week. In a previous post to this blog (here) I commented on the dangers of fake chips and hardware entering the market from China and the potential security implications of these pieces. Well now business week has conducted a multiple week research piece tracking back the origin of a number of chips that caused malfunctions in equipment provided through BEA to the US military. With an interesting video and five fact filled pages of story, this is a very good read indeed. (*Thanks to Chris Eng for pointing this story out to me*). |
| SecTor - Day 1 [.:Computer Defense:.] Posted: 08 Oct 2008 10:05 PM CDT I debated what to write here, and if I would present the positive or negative points but I figured the only fair way was to describe both, so without further ado, I present SecTor Day 1 - The Good, The Bad and the Ugly. I figured I'd describe my day from start to fishing, instead of breaking it up by what I did or didn't enjoy. The day started off with breakfast at Cora's, a group of us met there only because this years SecTor schedule made no mention of a breakfast similar to the one provided last year. Of course, when we showed up, it turned out there was a provided breakfast... at least we know for tomorrow. The initial keynote was done by the RCMP and I don't even know what to say. Last year's RCMP presentation was depressing (many people that I spoke to today said it was the worst part of last year, and there was a debate over which RCMP keynote was actually worse. This years was made worse by the fact that it was first thing in the morning. It was presented with little enthusiasm and I'll say it... it sucked. When the RCMP speaks, you'd expect to learn something interesting, in fact a number of attendees mentioned that to me today. Yet nothing interesting was learned. I was eager for this talk (as I was eager for the keynote last year), I figured they had learned from last year and that this year the RCMP would do better. I took about a page of notes, but got nothing of interest. The names of a few councils (ITAC Cyber Security Forum and CBOC's Council on Security & Tech) and learned that there was a Cyber Security Conference in Gatineau on Nov. 5 & 6. That could have been a single slide, or better yet a hand-out. The rest was useless, this was evident by the people falling asleep and the notes left on Twitter.m I was also rather offended by a closing remark that David Black made regarding them looking for trained University graduates. I attempted to open my notebook and write down his email address to contact him but unfortunately the slide was removed from the screen. If anyone wants to pass this along to him, it would be appreciated. [Begin Side Rant] I'm getting really tired of this biased hiring practice in many places that requires a University degree, it's a useless, archaic requirement (much like the requirement for various certifications [which we see more and more people dropping from job postings]). Many of the really bright IT/IS people that I know have no formal education or a college education... it's a shame to see so many places discriminate... especially places like the government. I'd think that workplace equality would include method of education, and place the importance on actual skills and knowledge[End Side Rant]. Needless to say... KeyNote #1 was a fail. Up next was the first session. None of the session interested me, so I decided to check out the lock picking village. I was in the hall by the vendor displays, so I visited each display on my way over, and failed to make it to the lock picking village before the first session was over. I did have some great conversations with the vendors that were present though. A big thank you to all of them for the sponsorship that they provide. While there was nothing that caught my interest, I know people that attended both 'Double Trouble: SQL Rootkits and Encryption' and 'Network Security Stripped: From layered technologies to the bare essentials". I can say that I didn't hear negative reviews about either presentation. In fact most people liked what they saw, and those that didn't like it were fairly neutral in their comments. Lunch and a Panel Discussion were up next. The lunch was Monday's left overs... my chicken fell off the plate and bounced; there was Twitter discussion around having a chicken bouncing competition. Yet that was almost the highlight of the lunch. The real saving grace on the panel was Hoff. I understand why everyone was up there; a number of them were sponsors and probably wanted to say their piece, but still... We basically had 8-minute, extremely dry lightning talks. A panel usually involves some sort of discussion or interaction, they was basically everyone bragging about themselves and drew quite a bit of twitter traffic Following lunch, we had what I would call worst organizational decision made by the organizers. They did fairly well this year... there is some good content (you just have to dig to find it -- My favourite part of today was hearing (a couple of times), 'the talk that you submitted would have been much better than this'), the swag was cool, a lot of people had positive comments about the notebooks and the bags and there's an increased social aspect. The mistake however, was a really bad one... it was the mistake of placing the bulk of the good speakers in competing time slots. This happened today by having HD Moore, Jay Beale and Raven in the same time slot. Those are three talks I would have gladly gone to see, and I had to pick one. From what I hear this happens tomorrow as well. I'm really looking forward to Hoff's talk, however I've been told that James Arlen is quite the impressive presenter as well. In the end I decided to go with Jay Beale's discussion of the concepts behind his new tool, 'The Middler'. It was everything that a tool presentation should be. The tool wasn't shown or mentioned... the concepts and techniques were discussed. Not only did the presentation have some interesting information (I filled three pages in my notebook) but Jay did an amazing job with his presentation. This presentation alone made up for the lackluster performances up to that point (although I was quite disappointed about the stacking of the time slot). To briefly go back to the time slot, I believe the concept that was tried was to put the big speakers up against each other and then everyone else was grouped together, this was to ensure a somewhat even distribution of attendees and to avoid empty rooms. My feeling on this... if the persons presentation runs the risk of an empty room, regardless of what they are up against... don't accept the presentation. I'll stop ranting on this now... it's done and unfortunately it can't be fixed. For the next time slot, I decided on attending Googless. I was excited... it seemed really relevant to some of the work that I do. I don't even want to talk about this presentation... the slide show background was disturbing, and Christian had no life to him, as well he asked for donations on like the third slide (also the first time I've seen a license on a presentation) and informed us that would have to wait until December to see obtain the slide deck. I guess Christian thought that this was the most popular presentation at SecTor... judging by how many of us walked out during the presentation, I really doubt that. It wasn't good. I spent the last portion of that presentation speaking with colleagues before the rooms emptied out and the last series of sessions were to begin. I had originally intended to see the RFID presentation, however I managed to catch up with Jay Beale to further discuss the Middler as I was rather intrigued. So we were able to sit and discuss it for a short period of time. A few more people joined us and we moved to the keynote room for discussion and to await alcohol. This once again was an amazing opportunity to network with people, and proved to be more useful than attending the talks (or so I read (and heard)). I once again have to say kudos to the organizers for this... Anything that lets you get together with other people to basically 'talk shop' is a great thing and many opportunities were presented. During the Microsoft sponsored reception our table grew and we had a lot of fun. Then speakers departed and the bar closed, and unfortunately I wasn't able to make it to the party, however the day still had a number of high points. I realize this may seem like a griped a lot, but given that this was year two, I had higher expectations than last year and I'm not sure those expectations were fully met... but as I said, I did enjoy quite a bit of it. Tomorrow is another day, and there are a number of time slots where I'm interested in more than one presenter, so we'll see how it goes. |
| Asking The Cisco Systems IPICS and JPS Raytheon ACU-2000 Experts: Questions 36-40 [Voice of VOIPSA] Posted: 08 Oct 2008 06:34 PM CDT
Welcome to the eighth installation of Asking The Cisco Systems IPICS and JPS Raytheon ACU-2000 Experts, security questions derived from publicly available information such as vendor documentation, news/media, and other open sources. For your information, this will be the final post of this series for the remainder of this calendar year, and possibly longer. My reasons for this choice are many, but suffice to say that I believe there is too much going on in the US right now (elections, financial strife, etc., etc.) and that these blog posts and security questions will not receive the attention that I think they should at this time. The questions certainly have not garnered the attention of the vendors Cisco and JPS that I would have liked to have seen. Perhaps the situation is indeed, as one foreign national working for a major company in the US critical infrastructure space often stated, “It’s all the same. Nobody cares.” I’ve also gotten a bit busier with security consulting work and technical editing for a forthcoming book. In any event, I plan on continuing my research into this technology and will compile everything into a paper and presentation that I’ll take to security conferences. I’ve already been invited to speak on this subject at a well-respected security conference next year — I won’t disclose the conference name as I don’t wish to steal the organizers’ thunder, but suffice to say I am both honored and humbled for the invite. With that said, I am willing to discuss providing early drafts of my research to entities whom I deem are appropriate, but they will have to take the initiative and contact me directly. Frankly, I’ve grown a bit weary of trying to get the “right” entities’ attention on this subject, and rather than taking the piecemeal and assertive approach that I’ve done so far, instead I’ll gather all the information and questions into a single body of research for public dissemination in 2009. Moving on…. Question 36: When does Cisco Systems plan to release IPICS version 3.0? Question 37: Are there any Cisco Systems PSIRT advisories for the IPICS “in the works” and if there are advisories released that came about because of the VOIPSA blog posts will that be noted in the final advisory? Question 38: According to the “Technical Evaluation of the TRP-1000 and ACU-1000″ one of the several security findings states the following:
Has this issue been addressed in the TRP-1000 and ACU-1000? Further, is this security issue present in the ACU-2000? Is the issue present in any of the other ACU variants? Question 39: JPS makes available for download software for several products without requiring any registration or proof of license. As a result, anyone may download the software and perform analysis and reverse-engineering to discover potential vectors of exploitation, sensitive information, etc. For an extremely simple example, the software upgrade for the SIP Control Module SCM-2 I discussed in Question 33 could be downloaded and strings run against the image that could theoretically disclose information that an attacker might find “interesting” — such as the following:
Question 40: JPS does not have a specified security contact (i.e. security@jps.com) or a product security policy statement (i.e. like Cisco Systems’ PSIRT). Further, there has never been a publicly-disclosed security vulnerability with any JPS product either in public databases (i.e. NIST NVD) or on the JPS site. Does this mean that there has never been a security vulnerability concerning any JPS product reported to JPS? Thank you, |
| Google's "obfuscated TCP" [Errata Security] Posted: 08 Oct 2008 02:43 PM CDT Google's "obfuscated TCP" (ObsTCP) has appeared in the news again (on Slashdot). This is a good example of something that's a bit too subtle for people to understand. Security is a tradeoff. This means that security never comes for free, and that you must pay for it. That's why SSL isn't the default. It adds too much delay, and the additional processing power is too costly for websites. ObsTCP is the idea is to add the maximum amount of encryption within the same amount of delay/processing budget we already have for TCP connections. That means establishing encrypted TCP connection with an additional round-trip delay or CPU power. Why don't they use IPsec or better crypto algorithms? The answer is simply "because that would add more latency/CPU". Can this encryption be broken? Yes, of course, that's why it's called "obfuscation". I can still break into your TCP connection if you are surfing the web in a coffee shop using ObsTCP. However, I would no longer be able to do so in a completely passive way like Sidejacking. I'd have to instead transmit some packets. This means you could catch me if you were paying attention (such as surfing to a site for which you already have a key and see if they match). Widespread government wiretapping would have the same difficulty. They can do it now completely passively. With ObsTCP, they would either have to invest billions of dollars in breaking the ciphers, or they would have to actively transmit packets and reveal their wiretapping. ObsTCP doesn't protect the individual so much as protect society. I'm bothered by the fact that they are avoiding some solutions because the IETF won't like them. This contravenes the principles that the IETF was based upon. It's not the IETF's job to dictate standards, but instead to document working protocols that people come up with. It's like dictionaries: their role is to document how people use words, not dictate how they SHOULD use words. The ObsTCP project should be mindful of stepping on other people's toes, but if need be, go forward. If they won't assign you a TCP option, just pick one and use it. |
| Am I chopped liver compared to Sarah Palin? [StillSecure, After All These Years] Posted: 08 Oct 2008 02:33 PM CDT One of the foundations of our system of laws is that we are all equal under the law. The USA has no class or caste system that is recognized by our laws and our courts. We are all entitled to equal protection under the law, right? So why did the Justice Department indict the kid who p0wned Wasilla Wolverine's Yahoo email account, yet they refused to take action against the people who did to me? I don't know, maybe I don't wink enough when I speak or maybe it is time I "put on the heels and take off the gloves", but I find it a true double standard that the Federal Government would take action against the people who did this to her, but not the people who did the same thing to me. Is it a sexist thing? Are only woman entitled to protection under the law? Are only Republicans? Only people running for office? If this is a crime (and I believe it is a crime for sure), than the government should not be selective in who is eligible for its protection. Enough of catering to special interests! I am not a second class citizen and want the same rights that Sarah Palin has! Let me be clear, I don't condone what this person did to "that ones" (isn't that the term to use) Yahoo mail. It is a crime, it is wrong and should be punished. But I was told by multiple law enforcement personal that unless there was financial theft or fraud over 10k the federal government will not get involved. Any one who hacks into someone's private email or accounts should be prosecuted under the law. No Double Standards! Related articles by Zemanta |
| China’s TOM-Skype Surveillance [Voice of VOIPSA] Posted: 08 Oct 2008 01:42 PM CDT According to a report published on October 1st by Citizen Lab, full chat text messages from TOM-Skype users were found on publicly-accessible web servers as well as the encryption key required to decrypt the data. Additional data such as millions of IP address, user names, and land-line phone numbers, and records of international users who regularly communicated with Chinese users were found alongside the chat logs. From an Ars Technica article about the report:
While troubling from an overall Skype security standpoint, it’s not much of a surprise that the Chinese government had a way to monitor their Skype users, especially with Skype being partnered with TOM Online, a Chinese company. Since around September 2005, Chinese users attempting to download the Skype client were blocked from doing so, instead being redirected to a modified Chinese version hosted by TOM. Did anyone really think that this modified version wasn’t backdoored? Who wants to bet that they have keys to decrypt the voice channels as well? |
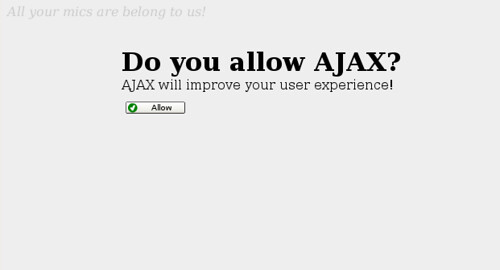
| More Advanced Clickjacking - UI Redress Attacks [GNUCITIZEN] Posted: 08 Oct 2008 01:08 PM CDT This will be a quick post just to share some POCs and more information regarding the recent Clickjacking technique, i.e. UI Redress Attack, a name suggested by Michael Zalewski. Clickjacking is an oldie but, a goodie. You can track the origin of the attack back at the beginning of this decade. Clickjacking is essentially the ant-CSRF killer. It is also the killer of Flash, AJAX (because AJAX apps are sometimes easier to clickjack, look at Google) and some other technologies. The picture that you see in this post is basically a UI redress attack against Flash. It works flawlessly on Ubuntu with the latest Firefox, Flash and the latest NoScript with the applied fixes against the clickjacking technique, i.e. ClearClick. I do not know why it works but it works. Btw, the POC that you’ve probably seen to circulate in the last couple of days does not work on my setup. The attack depicted above is very, very simple. All I do is UI redressing an evil iframe with preloaded malicious Flash file. In order to do that I use blank, absolute positioned iframes. At the end I color the entire page with the same color the standard Flash security dialog is using for displaying security messages. As you can see the user cannot do anything else but to click the You can download my POCs from this page (GNUCITIZEN Labs). ---
--- More Advanced Clickjacking - UI Redress Attacks |
| Reflections on Guernica [Got the NAC] Posted: 08 Oct 2008 05:30 AM CDT In Madrid for the ISSE 2008 conference, I found myself losing sleep over the state of our global economy. What a mess! With two free hours, I decided to visit the art museums. A quick cab ride brought me to the Reina Sofia Museum, which houses Guernica. No words or JPEG can do justice to Picasso’s masterpiece. Although the work was inspired by the brutality of war, to me today it spoke to the tragedy and beauty of life. Our current financial crisis will bring years of pain on a small and large scale. We must do what we can to avoid such tragedies but they will inevitably happen. Still, a small flower grows at the center of the painting. New life and creativity will spring from this tragedy as it always does. Please treat each other with kindness and patience for the next few months. Be an island of calm. Spread hope not fear. Nothing physical has changed in recent weeks, only a psychological change. Let’s keep it that way and support each other. We will come out of this crisis stronger and wiser than before. Tags: General, general |
| Nice Citibank phishing attempt example [mxlab - all about anti virus and anti spam] Posted: 07 Oct 2008 05:53 PM CDT We intercepted a nice Citibank phishing attempt. The email contains the notification that 1 message is waiting for you in the mail section so you will need to login.
This link brings us to the first step in the whole process, the login page. Notice that there is no secure HTTPS in use. The whole phishing web site is hosted on a blog server.
After a succesfull login (with a non real login and password of course) we get the security notification message to see.
This message explains that our account is temporary locked for security reasons after detection login attempts of foreign IP addresses. So, we need to update our account. When clicking in Continue we can fill in all our private details such as our address and more important our credit card details.
Again, we continue with dummy data and get a response page that the submitted details will be verified.
The green button at the end of the page contains a link to an external web site and leads us to a log out confirmation page. This domain appears to be registered by Citibank and contains a secured HTTP connection.
As you can see, it’s that easy to steal your information if you don’t pay any attention at all. Phishing attempts can be detected by following some simple rules:
 |
| 5th Emergency Services Workshop to be held Oct 21-23 in Vienna [Voice of VOIPSA] Posted: 07 Oct 2008 06:32 AM CDT How does an emergency call to 9-1-1 or 1-1-2 (or whatever your local emergency number may be) work in a world of voice-over-IP? It’s not a topic we cover hardly at all here on this blog, yet it’s definitely one of the security and social/cultural aspects of our migration to IP that we definitely have to get right. If we as an industry don’t, people can die. (Or the migration to VoIP will be significantly delayed.) To that end, a number of emergency services experts are meeting to discuss ongoing work on IP-based emergency services in Vienna, Austria on 21st to 23rd October 2008. The first workshop day is focusing on tutorials to help those interested in the classical 1-1-2 (or 9-1-1) emergency call to get up-to-speed with architectures and standards developed for next generation emergency calling. During the second day various recent activities of standardization organizations around the world will be presented. The third workshop day is dedicated to early warning standardization efforts and the outlook to future emergency services activities. Participation from those working in standardization organizations as well as persons with interest into the subject is highly appreciated. The event is open to the public and anyone may attend. More information about the workshop can be found behind the following link: This page also points to previous workshops that took place in New York, Washington, Brussels and Atlanta. (Thanks to Hannes Tschofenig for providing the majority of this text.) |
| The Return of the TCP Sockets [GNUCITIZEN] Posted: 07 Oct 2008 03:46 AM CDT Here is a common problem. You have to write an web-based email, im, ssh, xmmp, SMB, etc. client which must connect to a server other then the originating one. What do you do then? Hint: You cannot use Java! Well, due to the fact the the browser has no idea how to spawn a tcp socket, you are stuck in the proxy-land. Typically you will write an application that will do a lot of transcoding and state management. You need to come up with your own messaging protocol to speak to the backend, and the backend needs to be programmed to respond back in the same way. As you can guess, this is a difficult problem which requires a lot of work. Lucky for developers, there’s a way to quickly employ the power of tcp sockets without the need to deal with all the complexity. There are a few projects that already do that but the most interesting one is js.io, a JavaScript Network Library. I am not planning to get into any details of how the technology works. It is based on push-back AJAX and you if you want to learn more just Google it. Anyway, undoubtedly this is a very exciting, new technology. And like any other new technology it will be full of bugs and it will take some time to understand it completely. However, due to its sexiness, I can see how it may soon become part of the standard AJAX stack of technologies. Perhaps you can already see the problem. Perhaps you can even think how this can be exploited. Perhaps you are thinking right now that Wireshark does not have TCP over AJAX over TCP dissector. Well, at least this is what I am thinking. But no matter what you and I think soon we may have to rediscover all TCP vulnerabilities of the past. ---
--- More Advanced Clickjacking - UI Redress Attacks |
| Security Certifications [GNUCITIZEN] Posted: 06 Oct 2008 11:33 AM CDT Security Certifications - should you get some? Well, this is what I think. IMHO if you go for a certificate then you pretty much put a box around yourself and your abilities. I am sorry, this is my personal opinion. People will perceive you as such and such because of your certifications. While having a cert might be a good idea for your career and in particular your CV, showing off with it could be a bit harmful. I am not saying that you shouldn’t get certified. I am saying that most people get certified because of the certificate and not the knowledge they get with it. Everybody know that and it is hard to convince people otherwise. And this is the main reason why security certifications are significantly devalued over time, apart from the fact security knowledge needs to be constantly updated. The more people get certified the less valuable certifications are. What about CISSP? CISSP can certainly help you get good understandings of security processes but when it comes to real-world security what matters the most is your experience. Anything else is irrelevant. At the end of the day you have to solve someone’s problems. Well, in order to pass CISSP you do need to have some experience in the field, at least on paper. The bottom line is - if you want to make a career in the infosec industry than getting a certification might not be such as bad idea. Just be honest that you’ve got the certificate for the certificate itself. :) I hope that this post helps. ---
--- More Advanced Clickjacking - UI Redress Attacks |
| Fact Checking Helps [Sunnet Beskerming Security Advisories] Posted: 06 Oct 2008 09:31 AM CDT In the last few weeks there have been a handful of standout cases where poor reporting on an issue, including fake reports, led to significant negative outcomes for the companies involved. A couple of weeks ago it was a poorly dated news article about a United Airlines bankruptcy from several years ago that led to massive stock market losses for United Airlines, and most recently it has been a fake report about Steve Jobs having a heart attack that led to an immediate drop of 2% on Apple's stock, which recovered but still closed down 3% for the day. Apple's famed reputation for secrecy makes it more likely that rumour and speculation will gain traction amongst Apple-watchers, but if investors allow themselves to be led based on nothing more than baseless rumour, it might go someway to explaining some of the volatility in recent stock and commodity markets. Any time an incident such as this takes place there are immediately whispers about stock market manipulation having taken place. It is often said that people are smart and reasonable as individuals, but place them in a group and they become dumb, panicky herd-driven creatures. With the stock market being made up of a massive herd of investors, panicky and flighty responses can take place based on speculative and poorly referenced rumours, leading to major changes in the value (at least in the short term) of a stock. On a smaller scale, malware authors and distributors have been spamming our inboxes for some time with fake news stories in an attempt to gain hits on their sites for drive-by downloads or clicks on malware-loaded content. Pink sheet stock pump and dump scams are also very similar, but on a smaller scale. In each case, falsified or exaggerated "news" is being pushed to users in an attempt to compromise a system or manipulate a stock. What stands out from the recent cases is the seeming unwillingness for reporting organisations to admit responsibility for spreading the false or outdated news. If they hadn't picked up on the story, then nothing would have happened, yet when it comes time to apportion blame, it seems like they can't point the finger fast enough at someone else. In both of the recent cases it wasn't until the misrepresented story appeared on "legitimate" and "trustworthy" sites that the problems really began for the companies involved. Rather than stand up and admit that they contributed to this latest event, CNN have handed over as much detail as possible on the alleged source of the Steve Jobs rumour to the SEC. You can argue as much as you like about whether it is "New Media" versus "Old Media", but ultimately it is a case of poorly verifying content that has been published. The same problems still take place in print and broadcast media and it doesn't take too much searching to turn up errata columns where these errors are hopefully addressed. |
| Governments Listen to You - Just Not The Way You Think [Sunnet Beskerming Security Advisories] Posted: 06 Oct 2008 09:28 AM CDT It should have come as no real surprise that Skype's China-based partner had been intercepting, logging, and even blocking text messages traversing the Skype network through China. A Canadian research group discovered the activity after breaching the insecure Chinese servers (which in itself was a dubious activity, but since the data was available from a web server that was outward facing, it can be argued that it was permissable). Based on a previously disclosed set of text filters, the modified filters allowed for a broader set of communications to be intercepted and logged, apparently without Skype's knowledge. As the original filter was described, it was meant to drop text messages that had been deemed inappropriate and not transmit them anywhere. The modified system seems to have resulted in the messages being transmitted to centralised servers for further storing. It is interesting that the tracking servers appeared to have been compromised by others before the research group came along. This opens up some interesting possibilities to pressure people of interest, based on intercepting already intercepted messages. It would be possible to alert people to the fact they are being routinely logged, even for traffic that does not match any filterable words, as well as lean on people by blackmailing them into doing what you ask them to - after all, you have copies of their text conversations. |
| Exploiting trust in social networks [spylogic.net] Posted: 06 Oct 2008 08:05 AM CDT Over the weekend I posted my first article on Social Network/Media security over at Blogsecurify. You can check out the post here. My next article will talk about the security of third-party applications and widgets for social media applications. |
| Clickjacking and Flash [GNUCITIZEN] Posted: 06 Oct 2008 03:22 AM CDT I heard of clickjacking a couple of weeks back when the media blast started. At that time a had a very vague idea what it was and just recently I saw some POCs coming out to show how it works in practice. Clickjacking, if I may categorize it, falls into the category of GUI attacks. I associate the clickjacking attack with the focus stealing attack which allows attackers to steal any file from the disk as long as they trick the victim to type enough characters. Ok, this is not a razor-sharp exploit but it is an exploit nevertheless. In essence, the clickjacking technique allows attackers to trick the victim to click on areas of a disguised HTML elements such as an IFRAME preloaded with let’s say your Facebook account information. If nothing else, clickjacking is the killer of most anti-CSRF techniques. I haven’t been thinking about clickjacking at all. I mean the attack is quite obvious and the potentials for damage are there. However, this morning when woke up, an interesting question started to circulate in my head. The simple truth is that Adobe are worried about the clickjacking technique because Flash’s current and even future and a lot more enhanced security model relies on user interactions, i.e. clicks performed by the user. Therefore, today attackers can trick the user to allow the microphone to survey the sound in the room where the victim’s equipment is located. They can use clickjacking for that! But there is more. If you have been following the development of the Flash platform, you are probably aware that Flash will soon become practically the most powerful web tool out there. Seriously, Adobe are revolutionizing the way we interact with the Web. Not only Flash will support a primitive P2P streaming protocol (I need to think of something malicious to do with that…), but they will also allow users to open and save files from and to their local disk. The only catch is that this feature is available via the IMHO I do not think that this security model is bulletproof. The potentials for abuse are obvious, and since clicks are the driving force of future Flash’s security model, then clickjacking is what it comes to mind if you want to abuse them. Perhaps, in the future we might be able to connect to TCP sockets as long as the user clicks? In conclusion, clickjacking is not a killer problem and it does not break the web, well not entirely. However the clickjacking problem is hard to solve. IMHO, I believe that it is even harder to solve then any overflow you may have to deal with. Why? Because we are dealing with user interaction and graphic design related problems. The solution has to be so clean that it doesn’t break half of the Web. ---
--- More Advanced Clickjacking - UI Redress Attacks |
| You are subscribed to email updates from Security Bloggers Network To stop receiving these emails, you may unsubscribe now. | Email Delivery powered by FeedBurner |
| Inbox too full? | |
| If you prefer to unsubscribe via postal mail, write to: Security Bloggers Network, c/o FeedBurner, 20 W Kinzie, 9th Floor, Chicago IL USA 60610 | |

![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=93a9de7c-e088-4f9a-9223-4e58e51df3e8)
![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=dc504d80-bbf4-48f4-8e33-c9d544b0d9ea)






No comments:
Post a Comment