Spliced feed for Security Bloggers Network |
| Biometric passports launched in Malta [Malta Info Security] Posted: 10 Oct 2008 02:02 PM CDT As reported on the Times of Malta today, the Passports Office has started issuing biometric passports, providing holders with a more secure travel document. At the moment, the new passports contain the same information as the old ones, with the difference that the information is held in a more secure manner in a chip embedded in the document. In the future, the chip will also carry an image of the holder's fingerprint. (The minister) Dr Gatt said the introduction of the new passports was also an important step by Malta to meet US requirements for eligibility to the visa waiver programme. Of some of the people correctly pointed out on the original article, that there already are some hacks out and about - More can be here however the EU is also counteracting. A recent article on The Register talks about 'second generation' electronic passports and the measures the EU are taking to ensure the encompassing security. This second-generation framework, known as Extended Access Control (EAC), is intended to combat impersonation as well as forgery through the addition of biometrics such as a finger print or iris scan. This biometric data is then digitally signed and included in an ePassport. The Register (19 Sept 2008) continues to discuss testing times ahead, but the race and challenge between them being cracked and security has only just begun --- putting to question the overall security design. Needless to say, whilst some are arguing the overall costs of this whole new implementation, this is the way forward and there is no going back. We'll have to wait and see what happens next (and I hate saying that..) More information on the hack can be found here (1st Oct 2008) Relevant links: Times of Malta Source Original Times of Malta article More official news from Ministry of Foreign Affairs Biometrics Deployment of EU-Passports Specification can be found here |
| Symantec to Buy MessageLabs (Email Spam and Web Traffic Filter) [Darknet - The Darkside] Posted: 10 Oct 2008 03:18 AM CDT Some interesting security industry news, it seems like Symantec is really setting itself up to be the Microsoft of the security world. They are buying up anything and everything and merging it into the Symantec borg…things that are successful of course. Their latest acquisition is the popular MessageLabs, a good example of both cloud... Read the full post at darknet.org.uk |
| Do tough economic times make people more religious? [StillSecure, After All These Years] Posted: 09 Oct 2008 11:03 PM CDT  Image via Wikipedia Ok here is a theory I have based upon my own observations during the Jewish High Holidays that just passed. In tough economic times, do people seek solace in God? It would seem so. This year not only did I see more people attending services, but it seemed rather than the usual social gathering that the high holidays can be in a Synagogue in Boca Raton, people were fervently praying. That is not to say that there were not the usual designer clothes, Gucci loafers and big diamonds on display. It was as if the bad economic news was like a call to prayer for the faithful and heretobefore unfaithful alike. So does the current economic climate explain the more pious attitude among the congregation members? Are any of you seeing similar trends in Christian churches? What impact will a more religious population driven by bad economic times have on our foreign policy? Could it lead to a perfect storm that makes us susceptible to a religious-economic message leading to ill-advised policy decisions or even worse, an unnecessary war? Hey don't laugh the last time there was a world wide depression, there was a world wide war to pull us out of it. I hope that isn't the case now! |
| Its Almost Time To Move On [BumpInTheWire.com] Posted: 09 Oct 2008 10:42 PM CDT One more ass kicking for the Huskers and I can put this three game stretch behind me. The Big Red take the show on the road this week with a trip to Lubbock, TX to play Texas Tech. The last time Nebraska went to those parts was 2004. 70-10 with the good guys being on the wrong end of that score. Expect more of the same. If you’re gonna play it (TT -21), lay it. Texas Tech 66 Nebraska 24 |
| The State of American Government and Politics [The Falcon's View] Posted: 09 Oct 2008 09:08 PM CDT |
| Frame Injection Fun [GNUCITIZEN] Posted: 09 Oct 2008 07:01 PM CDT Frame injection vulnerabilities, although some people might consider them the same as HTML injection/XSS or even a subset, they really are not the same. Here is why:
The best way to explain what I mean is to show an example. Most frame injection issues occur in web applications because dynamic frameset/iframe insertion is not implemented with enough filtering. For instance, say that we have the following URL on the target site: A malicious user with intentions of launching a phishing attack will try tampering the I thought that showing a live example would help our readers get an idea of what frame injection looks in action. For that purpose, I prepared a rather not elegant proof of concept which takes advantage of the Google Images service. What’s neat is that although the legitimate URL would normally use the images.google.com domain, Google also allow us to use other google.com subdomains such as mail.google.com which is used by Gmail. This is ideal, as we’re trying to accomplish a frame injection attack which can be used to perform phishing attacks against Gmail users. The previous PoC URL will cause the entered credentials to be submitted to www.gnucitizen.org when clicking on Sign in, so please do NOT submit any real credentials! Needless to say, in real-life the attacker would most likely automate the process of obtaining the harvested credentials by using a tool such as our x.php data-theft script. ---
--- Frame Injection Fun |
| Apple Security Update 2008-007 [Infosecurity.US] Posted: 09 Oct 2008 06:30 PM CDT |
| links for 2008-10-09 [Andrew Hay] Posted: 09 Oct 2008 04:02 PM CDT
|
| Large Enterprises Paying Heavily as Networks Grow [ARCHIMEDIUS] Posted: 09 Oct 2008 03:29 PM CDT A few days ago Computerworld released a MarketVibe report (sponsored by Infoblox) that showed a strong correlation between an organization's size and the amount spent per IP address to manage the network. One would think that with more users that costs per user would actually decline as additional IP addresses are added against fixed or [...] |
| SecTor - Day 2 [.:Computer Defense:.] Posted: 09 Oct 2008 02:36 PM CDT I'll start of by saying the second day of SecTor was amazing compared to the first day. We started off with Stepto giving the opening keynote. While it wasn't anything groundbreaking, it was exactly as advertised and well presented. I fully enjoyed hearing him walk through how he got into security, his time with MSRC and how things he'd learned working in security applied to other aspects of his life... it was great. Following the keynote, I was torn between Pwning the Proxy and Lock picking. In the end personal interest won out and I attended the lock picking session. There was quite a bit of interest information shared and I managed to take a couple pages of notes. One of the coolest things was the how-to on making a combination lock shim using a piece of aluminum from a pop/beer can. Following the lock picking session was lunch. The meal was much better than the day before. One thing that I didn't get was why so many tables were reserved and there was staff keeping people from sitting at them. The same thing existed on day 1 and the tables were never used, so why were they there are day 2? Lunch was also great because Johnny Long was the lunch keynote. If you've never seen Johnny speak... make every attempt you can to see him somewhere. He spoke with regards to his No Tech Hacking book (proceeds of which go to Charity) and the presentation was quite amusing and a lot of fun to watch. He gave examples of information gathered by shoulder surfing, dumpster diving, etc. It essentially centered around the non-technical side of reconnaissance or pen-testing. The entire crowd spent the time laughing and fully enjoying themselves (or at least that's how it seemed). After lunch I checked in on Hoff's virtualization talk. It actually had some interesting information and I was really glad that I'd attended it. I was unaware that there was a Cisco vSwitch for ESX but I really like the concept. It'll enable some very interesting things to happen. I had planned on attending the talk on identifying crypto in code for the last session of the day, but a old coworker showed up and we spent the session catching up in the keynote room. Following that there was some brief conversation and the wrap-up (which including the awarding of prizes). I did note that a couple of the prizes weren't given away (Checkpoint wireless router/firewall for instance), so hopefully that wasn't just a scam to get business cards. Then a small group of us (9 people I believe, both speakers and attendees) went out for all you can eat sushi, and a few drinks. I really enjoyed myself day 2 and really enjoyed the con as a whole, there were just some really bad experience on the first day. I'm definitely looking forward to SecTor 2009! |
| Cricket: We’re Now in a New Era of DNS [ARCHIMEDIUS] Posted: 09 Oct 2008 02:34 PM CDT According to Cricket Liu this new era of DNS that we've just entered will require us to be more nimble and more proactive. Things may move fast, now that hackers can target DNS. This second episode of bloxTV is an 18 minute "big picture" chat about DNS security and the impact of Kaminsky's discovery. Cricket [...] |
| Microsoft Releases Security Bulletin for October 2008 [Infosecurity.US] Posted: 09 Oct 2008 01:41 PM CDT |
| Reviews: Security scans with OpenVAS [CGISecurity - Website and Application Security News] Posted: 09 Oct 2008 01:21 PM CDT " As important as security is, remaining current with every development is hard, and evaluating possible vulnerabilities across a network can be quite a chore. You need a way to both automate tests and make sure you're running the most appropriate and up-to-date tests. Open Vulnerability Assessment System (OpenVAS) is a... |
| We Wish A Safe and Peaceful Yom Kippur To Our Jewish Friends and Their Families [Infosecurity.US] Posted: 09 Oct 2008 11:09 AM CDT |
| Recording and Stream Notice - Episode 126 [PaulDotCom] Posted: 09 Oct 2008 09:31 AM CDT The live stream should be active about 18:30 EDT, Thursday, October 9th. We should begin recording the live show at about 19:00 EDT. Please keep in mind that these times are all estimates, but we will try to do the best that we can. We even have a sepcial guest this week: International man of mystery, and alleged double "agent" Ed Skoudis! Don't forget to join in on the IRC channel during the stream - we can take live comments and discussion from the channel! Find us on IRC at irc.freenode.net #pauldotcom. When active, the live stream(s) can be found at: Ustream: http://ustream.tv/channel/pauldotcom-security-weekly Icecast: http://radio.oshean.org:8000 Please join us, and thanks for listening!  - Larry & Paul |
| Posted: 09 Oct 2008 09:06 AM CDT It also means that or your pc is infected or you have given your credentials in a phished page or the mailserver is hacked. @blub.be @finalphoenix.be decortedanyy@hotmail.be danny.vangoethem@pandora.be jelle.put@pandora.be jess.h@pandora.be jonas.vanpoucke@scarlet.be e.i@skynet.be zoidberg@skynet.be akuma@swing.be and so on and so on and so on look at the document in You know what to do ? change your password alain.grun@telenet.be
|
| 9600 emailaccounts hacked (the LIST is here) [belsec] [Belgian Security Blognetwork] Posted: 09 Oct 2008 08:32 AM CDT Hacker Farbod posted 9600 passwords with the corresponding emailaddresses for free on his website. It was only a sample he said. There was much more to get. Maybe time to change your passwords for once. Hacker gives away Aussie's passwords - New Zealand's source for ...Oct 2008 ... The distributor of the data, a hacker who uses the name Farbod, offered 9600 identities for free. His motivation? The list of the emailadresses. It is 93 pages so if you open it in Adobe you can search for your own address or better part of it
|
| The NSA Open Source Project - TOKENEER [Infosecurity.US] Posted: 09 Oct 2008 08:18 AM CDT |
| Jeremiah Grossman - Clickjacking Video [Infosecurity.US] Posted: 09 Oct 2008 08:17 AM CDT |
| Posted: 09 Oct 2008 07:51 AM CDT Someone on LinkedIn asked: My long answer goes like this:
This is certainly not the best answer. Follow the discussion over here. You are not going to learn anything technical but at least you will get a good idea how the majority of security professionals on LinkedIn think. ---
--- Frame Injection Fun |
| Posted: 09 Oct 2008 07:13 AM CDT 07/28/08: ISR-evilgrade v1.0.0 You need metasploit, but if you are a pentester, you knew that already Someone believes that dns servers are always secure because they rely on the DNS of your ISP. In fact DNS is everywhere from your machine till the server of the website where you are going to and each of them has to be patched and secured. Period. |
| clickjacking flash : how to protect yourself for the moment [belsec] [Belgian Security Blognetwork] Posted: 09 Oct 2008 07:11 AM CDT Adobe has for the time no time to develop a security update so you have to protect yourself guys and girls, there is nobody else that will protect you.
IT Administrators:IT Administrators can change the AVHardwareDisable value in client mms.cfg files from 0 to 1 to disable client Flash Player camera and microphone interactions. For more information on the mms.cfg file and AVHardwareDisable, please refer to page 57 of the Adobe Flash Player Administration Guide: http://www.adobe.com/devnet/flashplayer/articles/flash_player_admin_guide/flash_player_admin_guide.pdf#page=57. Adobe is working to address the issue in an upcoming Flash Player update, scheduled for release before the end of October. Further details will be published on the Adobe Security Bulletin page at http://www.adobe.com/support/security. http://www.adobe.com/support/security/advisories/apsa08-08.html There are already demo's of attackscripts for * webcams * twitter following boxes * your imagination because everything with an iframe |
| NetStumbler - Windows Freeware to Detects Insecure Wireless Networks [Darknet - The Darkside] Posted: 09 Oct 2008 06:31 AM CDT Another one from the old school, this tool has been around forever since way before wardriving was fashionable and when people still used pringles cans for antenna boosting. It’s a favourite amongst Windows users, although it can’t do any real hacking (like breaking a WEP key) - it’s extremely fast and effecient in the detection... Read the full post at darknet.org.uk |
| Spammers use receipt and opt-out messages [belsec] [Belgian Security Blognetwork] Posted: 09 Oct 2008 06:03 AM CDT "The first technique uses a ‘read receipt or notification' method to make the recipient think that they have received and read the message, enabling the spammer to know that the address is valid and active. If the recipient does not send the read receipt, the spammers deploy a secondary layer of confirmation techniques which uses a reference to a remotely stored image.
Should the previous two confirmation tricks fail, the third layer takes advantage, especially when the victims suspects foul play but may not be aware of the “classic” unsubscribe or opt-out scam. The alleged opt-out links do not unsubscribe the recipient from the mailing list, but confirm instead that the e-mail address is fully functional and ready to get even more spam.
Vlad Valceanu, head of BitDefender's Antispam Researchm said: “Users should be aware that without the appropriate security solution the integrity of their systems is at an extremely high risk. To validate the e-mail address means that the user has signed the death sentence of his or her inbox" source This means that you have to educate your users that they should never send an opt-out message but send the spam to you so you can block it for all. Secondly you should have a system that blocks images in email and for which the users has to confirm that he or she sees the iimage. THirdly your server should not confirm addresses or not confirm them, just drop them. Seems not very friendly, but we aren't operating in a friendly environment. |
| Fortis sold to save Dexia for political reasons [belsec] [Belgian Security Blognetwork] Posted: 09 Oct 2008 05:47 AM CDT this is what some are thinking in this country they are wondering why Fortis hasn't been saved like Dexia is and if Fortis was sold to have enough cash at hand in case Dexia would have to be salvaged. Dexia is close to the present government. "Ondertussen likken de gedupeerde Fortisaandeelhouders, en dat zijn er heel veel in dit land, hun wonden. Boos op het voormalige Fortismanagement maar ook stilaan boos op de regering-Leterme, die - zo blijkt steeds duidelijker - de uitverkoop van Fortis organiseerde om te kunnen beschikken over een oorlogskas voor Dexia. |
| Posted: 09 Oct 2008 04:01 AM CDT I think most of us are quite surprised about how deep the financial crisis is becoming. More and more of us are sitting here and wondering how it will affect us in our personal or business lives over the coming months, and I thought I would try and take a look at how it affects consumer authentication. I will cover the more obvious ones in later posts, like potentially smaller security budgets and the cost savings of using the internet as a channel, but a little gem from the BBC website really caught my eye. The upshot is that all of a sudden banks aren't lending as much money as they used to. Ok so how does that affect fraudsters? Well obviously less money available to lend manifests as tighter controls on the acceptance of applications for new credit agreements, which are falling rapidly. So with an overall decrease in credit applications then naturally that means an overall decrease in the number of fraudulent claims that get through the system. With the notable exception of Whaling, targeting high wealth individuals for nefarious gains, if you are stealing an identity you are less likely to get an application fraud accepted because the individual is less likely to be credit worthy. So as a fraudster what do I do? I need to make my money, so I target those people who already have an established relationship with the organisation. In other words I target the people with an existing account. This is where consumer authentication really becomes important. The more I follow fraudsters the more I get back to the idea of "the rational man". This is one of those stating the obvious theories hidden behind psychobabble which means if it makes financial sense everyone will do it. According to this article, which I believe, Fraudsters will switch their focus to account based relationships away from application fraud as they are unable to make money through that channel. But what is most interesting here is that the UK banking industry looked like it was winning the account takeover war. Fraud in this area had reduced from £33m to £22m from 2006 to 2007. This was mainly due to better Risk based Authentication being conducted in the back office as consumers (and yes fraudsters) try to access accounts. And then in the first half year of 2008, APACS release fraud figures showing that account takeover fraud is increasing again. Some questions, with my opinion as answers: 1) Is the rise in account takeover fraud a direct result of the credit crunch and the associated switch to account takeover from application fraud? I doubt it, the credit crunch hadn't really bit by the release of these figures. 2) Didn't the security implementations of EMV CAP (i.e. PINSentry et al) mean that Account Takeover fraud was decreasing? Well I am sure that these initiatives had a positive impact on fraud but what I guess has happened is that those who have implemented stronger authentication are experiencing less fraud but those that haven't are seeing exponential growth in fraud in this area. And this fraud is only going to get worse as fraudsters follow the rational man hypothesis and go for the easiest money route, account takeover at those banks who have not implemented more secure authentication. 3) So should all banks follow the EMV CAP model? I don't think so, I love the security benefits of PINSentry et al but hate the usability issues which are well documented (just google PINsentry and you will see what I mean), but there are other more consumer friendly devices that can achieve similar results to EMV CAP, especially when combined with Risk Based Authentication and I believe that they will become more prevalent. 4) Will fraudsters following the rational man model keep targeting the account based relationships in the banking sector? Yes, increasingly so. Do nothing and your fraud will rise. Tell me I am wrong. 5) If application fraud decreases and account takeover fraud increases will that only be in the financial sector? Absolutely not. Any account based relationship is a potential money spinner for a fraudster...see earlier post about Mexican bail bonds. So, here are a few questions which I will leave for you to answer: 1) As a bank do you believe that you should be doing more to stop account takeover fraud, given that the overall fraud is rising but competitor organisations have already implemented technology to reduce fraud making you the easier target? 2) As a non financial sector organisation do you believe that fraudsters are not looking at you as potential targets as online banking gets more secure? 3) Do you not think as fraud rises and confidence amongst your consumers is falling, threatening the cost effective internet channels you want to grow, that your business does not need to consider stronger authentication?
|
| Mexican bail bonds [Mike Davies: Online Identity and Trust in EMEA] Posted: 09 Oct 2008 03:58 AM CDT
According to the Guadalajara reporter, I presume a respected voice in the land of Tequila, fraudsters have come up with an innovative way to defraud Joe Public and it goes something like this. Step 1 - Fraudster gains control of an individuals personal email account Step 2 - Fraudster emails all personal contacts stored in the address book of taken over account Step 3 - Email contains an appeal for funds as stolen account individual is in Jail and needs money for bail "Hi friends, I need your help. Unfortunately I am in jail (again), of course I didn't do it but try persuading the Guadalajara police that. I need your help to post bail, please send whatever you can (at least 1000 pesos) to the following bank account as soon as possible XXXX XXXX XXXX XXXX. Thanks. Jose." You might think that you would never have friends that would ask you for contribution to help them out of jail and would dismiss it as a scam, so how can his be relevant to me? Well let's substitute the "bail" request for something closer to home, remember, this is an email you receive from someone you know and probably receive emails from regularly: "Hi friends, I need your help. I am running the London Marathon this year and I promised to raise £1000, so far I am only at £300 If I don't get the full £1000 there are going to be a lot more homeless children so please donate (at least £10 ) to the following bank account as soon as possible XXXX XXXX XXXX XXXX. Thanks. John."
How many times do you ignore spam from people you have never interacted with before? Probably always, you don't trust the sender, you don't trust the content. How many times do you ignore an email from a trusted friend? You may be wary of a opening a file supposedly sent from a friend, but would the above call for help go equally ignored? There is a level of trust you have established with your contacts which can be so easily abused by fraudsters, Why? Well a user name and password are so easily stolen, we need stronger authentication in the consumer space, but unfortunately it will require scams like this to occur before some businesses and consumers realise that. |
| I'm Back! [Mike Davies: Online Identity and Trust in EMEA] Posted: 09 Oct 2008 03:57 AM CDT I'm Back
It's been a really busy summer for me, here is the reason.....
She also blogs herself, and I am afraid I won't be sharing a link to her blog or her name as you would probably be able to find the blog if you knew my surname and her first name. Why don't I want you to find her blog? Well when my wife set up the blog she asked what she should or shouldn't publish, from a security perspective. We defined a policy for the new persons blog as such: Maybe I am being paranoid, but I know that is a part of my duty as a father to prepare her for for life, online or offline. If I made public her full name, the day she was born, the town we live in and other personal details like her mother and fathers name, I am already setting her up for an online fall. The amount of information that is being published by people on Facebook and other similar sites is manna from heaven for fraudsters. If you analyse what you need to take over a consumers identity the above information is a significant part. And what about if we published when we were going on holiday? It would only take a bad guy a little time to find out where we live, and know when is the best time to pay me a visit to relieve me of my treasured possessions. Just put it down to new parent paranoia... |
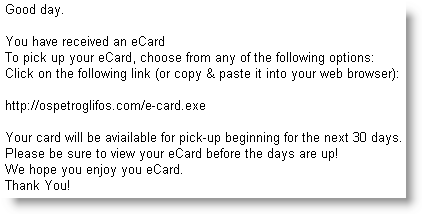
| Quickpost: Another E-card Malware Spam Campaign [Didier Stevens] [Belgian Security Blognetwork] Posted: 09 Oct 2008 03:12 AM CDT |
| You are subscribed to email updates from Security Bloggers Network To stop receiving these emails, you may unsubscribe now. | Email Delivery powered by FeedBurner |
| Inbox too full? | |
| If you prefer to unsubscribe via postal mail, write to: Security Bloggers Network, c/o FeedBurner, 20 W Kinzie, 9th Floor, Chicago IL USA 60610 | |
![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=878b6a7c-61a5-490d-9c98-5457685a42e5)



No comments:
Post a Comment