Spliced feed for Security Bloggers Network |
| Security Briefing - October 29th [Liquidmatrix Security Digest] Posted: 29 Oct 2008 07:23 AM CDT  Dear Higher Powers, Could you please release me and El Jefe from these craptacular symptoms now? I know I’ve had enough and I’m pretty sure he has too, though I’m sure you’ll have to assess each case separately. The Intern Click here to subscribe to Liquidmatrix Security Digest!. And now, the news…
Tags: News, Daily Links, Security Blog, Information Security, Security News | |||||||||||||||||||||||||||||||||
| Posted: 29 Oct 2008 06:00 AM CDT Objective vs. Subjective Approaches: Strengths and Weaknesses As we have seen, quantitative risk analyses can be subjective and qualitative risk analyses can be objective. The purpose of this slide is to summarize and discuss some of the advantages and disadvantages of both the objective and subjective approaches to risk analysis.
Read the rest of The Difference between Quantitative and Qualitative Risk Analysis and Why It Matters (Part 2) (972 words) © jlowder for BlogInfoSec.com, 2008. | Permalink | No comment | Add to del.icio.us Feed enhanced by Better Feed from Ozh | |||||||||||||||||||||||||||||||||
| RSA Europe 2008 - Day 3 [Infosec Ramblings] Posted: 29 Oct 2008 03:51 AM CDT Today is the last day of RSA Europe 2008. I have really enjoyed being here and have attended some very interesting sessions which I will be posting about in the near future. Today’s agenda is shortened since the last keynote ends at 13:30. For those who are interested, here are the sessions I will be attending. Lessons Learned from Société Générale - Preventing Future Fraud Losses Through Better Risk Management Virtual HIPS are Growing - Whether You Like It or Not Crash Course: How to become a Successful Online Fraudster Don’t Bother about IPV6? Beware: It is Already in Your Networks ICO - Higher Profile? Stronger Powers? More Effective” Security Cultures and Information Security Kevin Technorati Tags: rsa europe 2008 Posted in awareness, rsa europe 2008 Tagged: agenda, rsa europe 2008 | |||||||||||||||||||||||||||||||||
| Happy Birthday Dave! [Liquidmatrix Security Digest] Posted: 28 Oct 2008 07:24 PM CDT 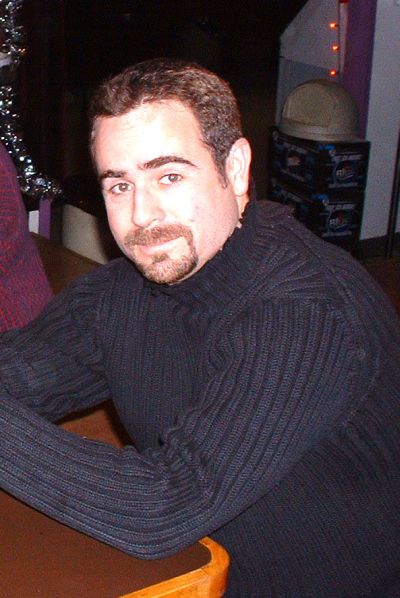 David Chuckles Lewis was born on October 28, 1970 in a foggy hamlet north of Toronto on a dreary Monday evening. Like him or loathe him (what’s not to love?), Mr. Lewis possesses all of the qualifications needed for birthday well-wishes on this blog: He is a Dad (father of a gorgeous daughter) and he is definitely a Geek. In addition, it’s his birthday so this day seems most appropriate. Lewis founded Liquid-Matrix Security Digest in 1998. (The hyphen was never actually used.) Throughout the early years of the Digest, he wrote every post, exploit and headline single-handedly while working full-time for the corporate machine. As the site grew he added contributors, reeling them in with a forceful crack of the whip when their opinions don’t match his own. Liquidmatrix got its start by being a source of exploit code and links to other security related websites. After a significant lobbying effort, Liquidmatrix turned to the new fad, "blogging", and the rest as they say, is computing history. In 2008, Lewis removed his picture from the front page of the Digest, in order to share the Happy Birthday Dave. | |||||||||||||||||||||||||||||||||
| XKCD: Secretary of The Internet Part One [Infosecurity.US] Posted: 28 Oct 2008 04:03 PM CDT | |||||||||||||||||||||||||||||||||
| ENISA: Network Resilience Stock Taking in the EU [Infosecurity.US] Posted: 28 Oct 2008 03:37 PM CDT | |||||||||||||||||||||||||||||||||
| Is security so boring that vendors have to resort to gimmicks? [StillSecure, After All These Years] Posted: 28 Oct 2008 01:25 PM CDT OK, I was never a big fan of the Wall Street Journal. I know some people consider it the bible of the business world, but personally I was more of a NY Times as the official word. nevertheless I respected what the Journal had to say. Since the WSJ was recently sold, I had serious misgivings that it would retain its objectivity. My friend Dr. Stanley Feld in discussing their recent writing on healthcare insurance coverage calls their objectivity into question. All in all though, an article I read today is I have to admit right on. The article says that tech security companies are resorting to gimmicks to get people aware and moving on security issues. They give a few examples. F-Secure calling for an international cyber-security police force, Panda making a connection between cyber attacks and stock market crash and the most gimmicky of all, McAfee appointing a chief cyber security Mom. That's right a mother. Agree or disagree with the gimmicks. You have to ask yourself why. With all that we read and see about data breaches, with all of these compliance regulations and rules around, why can't people take security seriously enough? Here is one mans opinion. Security is a bad news generator of an industry. We focus on what happens when things go wrong. We focus on adding to the process. We don't focus on the positive and the profitable. There is enough bad news in the world for people to focus on right now. They don't want the bad news that security makes them confront. If we can figure out how to make security a way of bringing a message of good news, we wouldn't need to resort to gimmicks. | |||||||||||||||||||||||||||||||||
| Chris Hoff Waxes Poetic: Cloud Computing Iambic Pentameter [Infosecurity.US] Posted: 28 Oct 2008 01:20 PM CDT | |||||||||||||||||||||||||||||||||
| We Don't Need Gimmicks [ImperViews] Posted: 28 Oct 2008 08:38 AM CDT The Wall Street Journal reports that some security software companies are turning to gimmicks to try to raise awareness around the problem of data breaches. The article states: "Breaches are up despite the fact that the percentage of businesses that encrypt laptop computers, databases, and back-up tapes--all places where sensitive data are kept--increased about 10 percentage points over the last year, according to a survey of corporate security executives by PricewaterhouseCoopers" It goes on to add: "The survey numbers underscore how technology can get a business only so far. Real security is a result of people understanding the nature of the threat and acting responsibly. Unfortunately, most people seem to be tuning out security news." In my opinion, the major issue is not the lack of awareness, but the fact that the majority of existing market solutions can not prevent data breaches and are not able to protect against web application attacks or data theft from a database. There is a reason that the PCI council mandates firewalls and Anti Viruses and Web Application Firewalls and Data access control and activity monitoring and strong encryption.... | |||||||||||||||||||||||||||||||||
| Posted: 28 Oct 2008 08:14 AM CDT
What could be more appropriate than stopping people from using software that they either pirated or are using in violation of copyright?
Are you kidding me? Is this the same country that just put on that Olympic spectacle, to show they have "arrived" on the world scene. The same country that runs billions of dollars in trade surplus with most every country in the world? The same country sending people to the moon? The same company taking jobs away from our own economy everyday because of their lower prices? Sure their prices are lower, they don't follow the same rules we do. What about if most American companies decided they didn't need licensed software. Why stop there. Lets not honor patents either. The heck with it, lets bypass our electric and water meters and don't pay that either. Do you think it might make us more competitive? Hey, if you want to play with the big boys, you should be playing by the rules. Inequalities and unfair advantages like not complying with copyright laws should not be tolerated. Either we all play by the same rules or don't play at all! | |||||||||||||||||||||||||||||||||
| Security Newsiness - October 28th [Liquidmatrix Security Digest] Posted: 28 Oct 2008 08:12 AM CDT  Good day - See you tomorrow! Signed, Click here to subscribe to Liquidmatrix Security Digest!. And now, the news…
And because I know at least one person is following this series, Part Two: Tags: News, Daily Links, Security Blog, Information Security, Security News | |||||||||||||||||||||||||||||||||
| Chinese hackers and the Saffron Uprising [The Dark Visitor] Posted: 28 Oct 2008 05:18 AM CDT Sorry, missed this when it first came out on 25 September 08. IntelFusion posts an article concerning pre-emptive Chinese DDOS attacks on websites that support the monks of the Saffron Uprising. Also planned counter attacks:
| |||||||||||||||||||||||||||||||||
| Posted: 28 Oct 2008 12:00 AM CDT
| |||||||||||||||||||||||||||||||||
| xKungfoo 2008 [The Dark Visitor] Posted: 27 Oct 2008 10:11 PM CDT The xKungfoo computer security conference will take place from 20-21 November 2008, at the C-Kong Hotel in Beijing. XKungfoo is being sponsored by Xfocus and HYXA (Beijing) Science Technology Co. Contact e-mail address for registration is: xkungfoo@xkungfoo.org. It is 500 yuan prior to Nov 1st, 600 yuan before the Nov 15th and 800 yuan if you pay on the 20th. Don’t know anything about the conference but I can get you the schedule and speakers’ info if needed. Once again, if you attend, we would like to hear about it!!! | |||||||||||||||||||||||||||||||||
| Desktop spoofs of Microsoft’s black screen [The Dark Visitor] Posted: 27 Oct 2008 09:01 PM CDT Hat-tip: Cherry (thanks) New reader Cherry points out that not everyone in China is raging over the infamous “black screen.” Some Chinese users are showing a sense of humor about the whole situation by creating desktop spoofs. The official Microsoft black screen comes with the tag-line, “You are possibly the the vicitim of pirated software.” The spoof reads, “I am possibly the beneficiary of pirated software.” Below,”Black Screened?” | |||||||||||||||||||||||||||||||||
| PCI Scanning After "Any Change" Makes A LOT of Sense [ImperViews] Posted: 27 Oct 2008 06:57 PM CDT Rafal recently gave his perspective on PCI and, among other things, he wrote that the requirement to perform a scan after every update to the site does not always makes sense: "... after any changes" - so if I change the background, or add new legal verbiage I have to re-submit my site to inspection? That makes no sense from a business perspective... does it? In my opinion, this requirement actually makes a lot of sense. While there may be changes that are minimal and do not affect the security of the site (e.g. changing the background color ), we all learned (the hard way) that developers have this habit of changing code even when they were told not to do so. Furthermore, some change control procedures might commit more than one code fix. In other words, while developer A might have changed just the background, developer B might have changed something that will be merged into the code in a way that would change the application. There have multiple cases where a 'simple' change has led to undesired and unexpected results. In this case, I feel that the PCI council did the right thing by enforcing a strict change control policy and using the words "any change" to resolve conflicts over when and what to scan. This policy makes the one auditor and programmer meeting essentially frictionless. | |||||||||||||||||||||||||||||||||
| Microsoft Publishes Webcast Q&A - Out-of-Band Security Bulletin (MS08-067) [Infosecurity.US] Posted: 27 Oct 2008 06:49 PM CDT | |||||||||||||||||||||||||||||||||
| Cutting Through E-Voting Semantics [Security Provoked] Posted: 27 Oct 2008 06:16 PM CDT The United Kingdom’s government said unequivacobly that UK will not now, nor in the forseeable future, adopt electronic voting. According to today’s story at The Register:
I did a story about e-voting a few years ago, and found it quite a vexing, exhausting process, because one had to viciously hack through a thicket of semantics to find out what e-voting proponents and e-voting opponents were really arguing about so vociferously. So I’ll now attempt to save you (and your machete) the effort, and give you the gist of the semantic debate. If you want a much more thorough minutiae-rich account (and you’re a member of the Computer Security Institute) you can read that here. First off: not all e-voting machines are created equal. “Optical scan” voting machines are technically e-voting machines, but are actually heartily recommended by many people who are often lumped into the category of “e-voting opponents.” What we most often think of as “e-voting machines” are DREs (Direct Recording Electronic machines). In essence the debate is all about whether or not meaningful audits of the voting machines’ accuracy and integrity can be conducted. Meaningful. After the polls close, a voting machine spits out a summary report of how many votes were cast for each candidate. There should be a way to verify that a) the machine’s count is accurate (like if 500 voters cast votes for Candidate A, the summary report will actually say that 500 voters cast votes for Candidate A), b) the machine recorded each individual vote accurately, and c) the machine/votes have not been tampered with. Most e-voting opponents say that the only way to conduct meaningful audits is for the voting system to create a “Voter-Verified Paper Trail” or VVPAT. In a basic DRE system, a voter presses a button (or types in a write-in ballot) to cast their vote, and then the DRE system pops up a little message on the screen saying “You voted for ‘Upstanding Citizen’ for ‘Senate.’ Is that okay?” and then the voter will press either “okay” or “decline.” The voter simply has to trust that when they pressed “Upstanding Citizen” the machine did not record “Evil Mastermind.” In a DRE-with-VVPAT scenario, the voter doesn’t see the “Is that okay?” thing just on screen. The machine, rather, prints the voter’s votes on a slip of paper, which appears behind a glass window. If the printout has it right, you hit okay, and the slip of paper is then dropped into a secured box. If for some reason–either because there’s a call for a recount, or because the polling place has been randomly chosen for a manual audit mandated by the state–the votes need to be verified, the human-count of the little slips of paper can be verified against the machine’s count. (And presumably, in the event of an incongruity, the paper count will be considered the official number.) Here’s where we really get into semantics. Here’s an excerpt I’ve lifted directly from my November 2006 Alert story:
So, technically speaking, a DRE can provide the necessary elements of a recount. The individual votes can be printed from the machine’s internal memory and hand-counted. The DRE even goes one step further, because the votes could also be printed from the removable memory card in case the internal memory was destroyed or corrupted. These devices are encrypted to make them resistant to tampering of stored data. However, there is still no way to assure the integrity of any of the data. If some error or fraud happened between the time that a voter cast their vote and the time the vote was stored, then a recount would simply retabulate the same erroneous or fraudulent data. Some say a VVPAT (or other form of voter verification) captures the intent of the voter, but once again, this isn’t exactly true. Paper doesn’t magically divine a voter’s will. If it did, there wouldn’t be questions like “Does this dimpled chad indicate a vote for this candidate or that the voter abstained from casting a vote in that race?” “If the voter filled in equally dark circles for two candidates in the same race, which one did they actually want?” What a VVPAT does capture is what vote the voter actually cast. If the voter leans on the keyboard, types in “”Aa;KJF” for governor and clicks “OK” it’s their error, not the machine’s, so it’s still a valid vote. As Avi Rubin, author of Brave New Ballot, told the Associated Press in 2006, “The problem is not that elections have been rigged, necessarily; it’s that you can’t say for sure that they weren’t.” | |||||||||||||||||||||||||||||||||
| LA Times Blog Reports Hamas Declares CyberWar On Israel [Infosecurity.US] Posted: 27 Oct 2008 04:46 PM CDT | |||||||||||||||||||||||||||||||||
| Amrit Williams Blog: Todays MustRead [Infosecurity.US] Posted: 27 Oct 2008 04:15 PM CDT | |||||||||||||||||||||||||||||||||
| ISSA eSymposium Scheduled Focusing On Log Management [Infosecurity.US] Posted: 27 Oct 2008 04:01 PM CDT | |||||||||||||||||||||||||||||||||
| Exploit status for MS08-067 [spylogic.net] Posted: 27 Oct 2008 04:00 PM CDT I won't go into detail about the new Microsoft vulnerability...you all know it's pretty serious and there are a ton of blogs and websites talking about the dirty details. Hopefully you have all read about it and are getting the word out about patching. However, there are some updates on the status of currently available exploits for the vulnerability that I found interesting. Public exploit code? Yesterday Microsoft posted this update to their blog on the MSRC. Microsoft says that there is currently no public exploit code available. The code mentioned that causes a denial of service attack was the code posted on Milw0rm I believe. The only working code released was from Immunity CANVAS and Core Impact if you are a paying customer. Core Impact does mention that the exploit is in early release and may contain bugs or limited functionality (not 100% reliable). Gimmiv.A - Is it a worm or a trojan? Don't let the thought cross your mind that you can perhaps delay patching your systems because public exploit code is not working/available! You still need to patch as there is malware that is currently out in the wild (Gimmiv.A) being used in "targeted" attacks. Whether or not this is a trojan or a worm is up for debate. Microsoft says this is not a worm but a trojan. However, other researchers are saying that this is worm because of the way it attacks other hosts on a network via RPC. I guess you could call it a "network-aware" trojan as ThreatExpert mentions. Either way, malware authors are most likely developing more powerful payloads as I write this. As a final reminder we all know based on past history with RPC vulnerabilities...reliable public exploit code will be out before you know it! Make sure you take your patching seriously... UPDATE: If you follow HD Moore on Twitter you will see that he has just released MS08-067 PoC code for Metasploit. | |||||||||||||||||||||||||||||||||
| CSI Needs Your Help on Web 2.0 Security [Security Provoked] Posted: 27 Oct 2008 03:43 PM CDT We're always particularly interested in what our readers are thinking. We're hoping you'll help us out by taking this survey about your Web 2.0 practices and perspectives. (It's only eight questions, and you can answer as many or as few as you'd like.) http://www.surveymonkey.com/s.aspx?sm=gRr0L0jG0BwO0SiqZ2fBaw_3d_3d. The results will be discussed during our CSI members-only call. To become a member and join the call, visit http://www.gocsi.com/membership. We'll review and discuss the results of the survey, give a brief overview of what we discussed/discovered in the October Alert, and then have callers openly talk shop about their challenges, successes, (and failures) as they relate to Web 2.0. After that call and survey are complete, we'll add the info to an updated issue of the October Alert, all about client-side Web 2.0 issues and secure browsing. http://gocsi.com/membersonly/showArticle.jhtml?articleID=211600271&catID=14144 | |||||||||||||||||||||||||||||||||
| WordPress 2.6.2 Flaw Revealed - Fixed With 2.6.3 Update [Infosecurity.US] Posted: 27 Oct 2008 01:51 PM CDT | |||||||||||||||||||||||||||||||||
| Netcraft Reports Phishing Attacks Expose Yahoo Accounts [Infosecurity.US] Posted: 27 Oct 2008 01:17 PM CDT |
| You are subscribed to email updates from Security Bloggers Network To stop receiving these emails, you may unsubscribe now. | Email Delivery powered by FeedBurner |
| Inbox too full? | |
| If you prefer to unsubscribe via postal mail, write to: Security Bloggers Network, c/o FeedBurner, 20 W Kinzie, 9th Floor, Chicago IL USA 60610 | |




No comments:
Post a Comment