Spliced feed for Security Bloggers Network |
| SSAATY - Podcast #56 - Michael Montecillo of EMA [StillSecure, After All These Years] Posted: 08 Sep 2008 07:22 AM CDT Send to Friends | Leave a Comment | Download |Play
If you like the content of these shows or have any other comments or questions, please drop us a line at podcast@stillsecure.com Thanks to Pod0matic for hosting our podcast. Tonights music is the usual, To the Summit by Jon Schmidt. You can hear more from Jon at http://www.jonschmidt.com. Music transitions between segments are by our own Mitchell Ashley! Enjoy the podcast!
This posting includes an audio/video/photo media file: Download Now | |
| Google Chrome Flagged As Dangerous in Germany [/dev/random] [Belgian Security Blognetwork] Posted: 08 Sep 2008 02:48 AM CDT
So much has already been written over the new Google browser (Chrome) that I did not write anything about it on this blog until now. The “BSI” (Federal Office for Information Security in Germany) warned users about the new Google toy. They recommend to not use the browser in professional and even personal environments! Source: Spiegel Online (Translation by Google Translate). | |
| Global Security Week… Go go go!! [/dev/random] [Belgian Security Blognetwork] Posted: 08 Sep 2008 02:08 AM CDT
The Global Security Week announced by L-SEC starts today! Check out the press release for more details (fr or nl). It’s a good opportunity for all of us to promote security in our environments and ’stick the knife in deeper’ with key facts:
Spread the word! | |
| Document of the day free starbucks recipe book [belsec] [Belgian Security Blognetwork] Posted: 08 Sep 2008 01:45 AM CDT | |
| SOLUTIONS Series on Information Assurance Infosec Conference Event [NovaInfosecPortal.com] Posted: 07 Sep 2008 09:37 PM CDT AFCEA International will be holding their SOLUTIONS Series on Information Assurance infosec conference event this week. I know this posting is sort of late but the good news is that it will be broadcast live for free. Here are the logistics for this year’s conference:
For more information on the SOLUTIONS Series on Information Assurance, see its description in our Infosec Conferences section. See AFCEA’s SOLUTIONS Series wiki page for more information. | |
| Backtrack/Nessus/Persistent Changes goodness… [Infosec Ramblings] Posted: 07 Sep 2008 08:50 PM CDT Hi everybody, Some of you know that I have been working on a document that describes how to build a bootable USB thumbdrive with Backtrack 3, persistent changes, Nessus, Firefox 3 and Fyodor’s Blackhat 2008 nmap on it. Well, it is ready for real world testing :) I have tested it to make sure it isn’t a complete waste of your time, but no warranties or guarantees are granted or implied Now, please feel free to send comments or suggestions to me at kriggins [at] infosecramblings.com or just leave a note on either the how-to page or this post. If you look in the header of this page you will see a tab titled “Backtrack 3 - USB/Persistent Changes/Nessus/Firefox 3/BH08 Nmap”. That is where the how-to is going to live. Direct link below. Backtrack 3 - USB/Persistent Changes/Nessus/Firefox 3/BH08 Nmap Good luck and have fun. Kevin  | |
| Twitter Weekly Updates for 2008-09-07 [/dev/random] [Belgian Security Blognetwork] Posted: 07 Sep 2008 04:59 PM CDT | |
| Posted: 07 Sep 2008 03:35 PM CDT Unlike all the previous generations, the Asus Eee PC 901 (or 1000) doesn't include atheros based wifi anymore. Which is kind of sad, since the new RaLink rt2860 doesn't support packet injection. Luckily, the onboard wifi of the Eee PC is a mini-PCI express which is easily accessible through the backpanel. So I ordered a GIGABYTE Aircruiser GN-WI01GT from oxfordtec.com (UK) after checking the madwifi compatibility page. Here is a quick walkthrough of how I installed the card.  The wlan card is easily accessible though the panel on the backside (only 2 screw). Click on the pictures for more details. The wlan card is easily accessible though the panel on the backside (only 2 screw). Click on the pictures for more details. Step 1. Remove the battery (just to make sure) Step 1. Remove the battery (just to make sure)Step 2. Remove the 2 screws and open the back panel. The shiny card on the upper left is the RaLink rt2860 card which is going to be replaced.  Step 3. Gently push the antenna connectors up so they will come off and remove the 2 screws on the card. Calmly shift the card in the direction of the screws and you will be able to take it out.   Step 4. Reverse your steps. Take your new atheros card and slide it into place. Fix it with the screws and (gently) push the antennas in place until you hear a small 'pop'. You can close everything up and boot your system. Step 4. Reverse your steps. Take your new atheros card and slide it into place. Fix it with the screws and (gently) push the antennas in place until you hear a small 'pop'. You can close everything up and boot your system.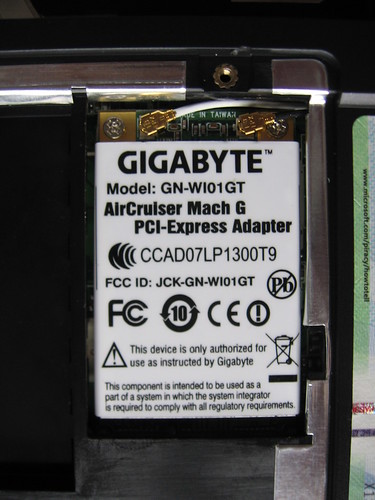 Step 5. Install the correct driver for XP/Vista or get the latest madwifi drivers for Linux and you're set to go. Step 5. Install the correct driver for XP/Vista or get the latest madwifi drivers for Linux and you're set to go.I must say that I get better range/signal strength then with the previous Azurewave card. Now I can really start with the rest of my lab experimentations. Upcoming tutorials:
| |
| Defcon 16 Media Coverage [Security4all] [Belgian Security Blognetwork] Posted: 07 Sep 2008 03:14 PM CDT  Defcon's comprehensive list of all articles known to have been written about DEFCON has been updated to include the 16th edition. Some of the topics you will find are:
Related articles:
| |
| Fedora 9 Upgrade Snaffus! [The Falcon's View] Posted: 07 Sep 2008 02:15 PM CDT | |
| Hacking Laptop Passwords [/dev/random] [Belgian Security Blognetwork] Posted: 07 Sep 2008 12:09 PM CDT
Interesting paper found via USB Hacks: Hacking Password Protected Laptops. That’s right: It’s easy to protect your laptop with a password (at BIOS or OS level). But if your laptop is stolen, your data are unsafe! It’s very easy to bypass or recover your passwords and access your data as usual. To increase your data privacy, your have to encrypt them! Using Truecrypt for example. And for even more security, don’t put your laptop in standby! Passwords can even be recovered by bringing your laptop at very low temperature! | |
| Mister P and Q’s Excellent Solution [Didier Stevens] [Belgian Security Blognetwork] Posted: 07 Sep 2008 10:49 AM CDT Mr. P and Q has solved my Authenticode Challenge. You can download his solution here, I copied his howto here below. I’ll add my own details in an upcoming post, but in the meantime, be sure to do a web search for the modulus. What you need: An internet connection A windows system A CPP compiler OpenSSL installed Step 1: Export the certificate used by Didier from ac.exe to didier.cer Select AC.EXE, Right click properties, Digital Signatures tab, "Details button", "View Certificate" button,Details tab, "Copy to File" button, select the "DER encoded binary X.509(.CER)" option and export to didier.exe Step 2: Use OpenSSL to extract the modulus of the certificate used OpenSSL>x509 -modulus -inform DER -in didier.cer Step 3: Use OpenSSL to convert didier's certificate in PEM format (for later use) OpenSSL>x509 -inform DER -in didier.cer -outform PEM -out didier.pem Step 4: Copy the modulus extracted in step2 into FindPQ.cpp, build the application, execute and (wait ... wait ... wait ...) ^1000 or download http://www.boo.net/~jasonp/msieve.exe. Start msieve msieve -v -n 0xD0EA1ABA978DF0065B2009F75C846F28B04ED5143B237B3FC24272245ADE837EFE0271E1A2854E0C81BA9F70A83AD86D47B0EACD062BC15BC61A99DC83124EC9 and (wait ... wait ... wait ...)^100 until it finally displays: prp78 factor: 102639592829741105772054196573991675900716567808038066803341933521790711307779 prp78 factor: 106603488380168454820927220360012878679207958575989291522270608237193062808643 Step 5: Create a 'real' RSA key so we can re-sign the modified ac.exe (remember the first part of this challenge) Copy the two factors found(step 4) into CreatePEM.cpp, build the application and excute. The application will produce newkey.pem Step 6: Use OpenSSL to combine newkey.pem and didier.pem (step3) into a PKCS12 keyfile (you will need to provide a password of your choice) OpenSSL>pkcs12 -export -in didier.pem -inkey newkey.pem -out magic.p12 Step 7: Import magic.p12 into your Windows system Simply double click magic.p12 select all the default options specify the password you defined in Step 6 when asked. Step 8: Download signcode https://www.thawte.com/dynamic/en/images/support/inetSDk5.zip unzip Step 9 Start signcode, select the modified ac.exe, select the "Didier" key and you're done ... Good luck Mister P and Q.  | |
| Goodie Security Picture of the Month [WAVCI] [Belgian Security Blognetwork] Posted: 07 Sep 2008 09:09 AM CDT Further on I was cleaning up a little bit my attic where I found a lot of old and newer security goodies (the free give-aways at conferences). So from now on I am going to use the good ones after I throwed away some other rubbish. For this job I got the wonderful help from a Symantec display box. On the picture you can see how you could use it in a creative way. ;-) BTW It's just coincidence that I used a Symantec 'box' for it. Other display boxes are also quite good. This time this picture becomes the Security Goodie of the month! | |
| Tietoturva 101 [Liquid Information] Posted: 07 Sep 2008 09:00 AM CDT (Sorry for Finnish announcement) Olen vihdoin saanut kirjoitettua perusasioihin paneutuvan tietoturva-paperin, joka on suunnattu tietokoneen loppukäyttäjille ja pienille yrityksille. Tämän paperin piti alunperin valmistua Joulukuussa mutta venyikin sitten näin pitkälle syksyyn, johtuen työkiireistä ja inspiraation uupumisesta. Nyt sen voi kuitenkin käydä lukemassa täältä ja sen nimi on "Tietoturva 101". Kommentteja voi kirjoittaa tähän blogi-kirjoitukseen tai vaihtoehtoisesti lähettää sähköpostia. On hyvä tiedostaa, että tämä on ensimmäinen paperi minkä olen kirjoittanut suomeksi ja se osoittautui yllättävän vaikeaksi kun pääsääntöisesti termit ynnä muut ovat englanniksi. | |
| Document of the day how US states are organizing ehealth [belsec] [Belgian Security Blognetwork] Posted: 07 Sep 2008 04:15 AM CDT This short overview gives an overview of the state of the different ehealth initiatives and the methods used in the different ehealth projects in the different US states. There are some interesting ideas.
| |
| (banali) Intercettazioni [varie // eventuali // sicurezza informatica] Posted: 07 Sep 2008 03:05 AM CDT ABC News: Ex-Dem Chair Apologizes for Hurricane Remark Scena: su un aereo Don Fowler (già presidente della convention del partito democratico) dice, a proposito dell'uragano che si sta dirigendo verso new orleans e farà cancellare la convention repubblicana: "The hurricane's going to hit New Orleans about the time they start. The timing is -- at least it appears now that it'll be there Monday. That just demonstrates that God's on our side. [..Risate..] Everything's cool."Ma qualcuno lo registra e lo mette su youtube. A Fowler non resta che chiedere scusa... "If this offended anybody, I personally apologize. It was a mistake, and it was a satirical statement made in jest. And one that I clearly don't believe."E constatare che può succedere che qualcuno ti registri, mentre parli. "One doesn't anticipate that one's private conversation will be surreptitiously taped"Ecco perché io, da bravo paranoico, non accendo il telefono immediatamente appena aprono le porte in aereo, ma aspetto di sbarcare; non parlo di cose confidenziali se non sottovoce se sono in una zona molto affollata e faccio le contorsioni del polso se scrivo SMS o email sul palmare per non farli leggere. Cosa c'entra su questo blog ? Semplice, si tratta di confidenzialitá delle informazioni e del fattore umano. Anzi l'esempio di Fowler é fin troppo banale. | |
| The Process of Writing the Applied Security Visualization Book [Raffy - Security Data Visualization] Posted: 06 Sep 2008 03:55 PM CDT
If you read the book, you will notice that this is pretty much what I ended up with. More or less. An interesting fact is that at the time of submitting the TOC, I had no idea what to exactly write about in the compliance and insider threat chapters. The even more interesting fact is that a lot of people told me that their favorite chapter is the insider threat chapter.
After a few days, I received an ISBN number for the book and a ton of material about style guides and how to go about writing the book. All very exciting. I decided to not write my book in TeX, unlike my masters thesis. That was definitely a smart decision. It turned out that using Word wasn’t that bad. The template from Addision made it really easy to format the text correctly. I actually ended up using VI to write the original text without any formatting. Once it was all done, I copied the raw text into Word and started formatting. The reason for doing this is that I am so much quicker in VI than I am in Word. (And hitting the ESC key in Word is not something you want to be doing too much.)
I definitely enjoyed the process of writing the book. The folks at Addison Wesley were awesome. They kept motivating me along the way and provided great insights into the writing process. What I am still very impressed with is the PR aspects. Early on, they hooked me up to film a video cast about the book. After publishing the book, I get about an email a week for some press opportunity. Keep them coming Here is a fun fact: In ~/Data/projects/vis_addision, where I have all the material for the book, I accumulated 1.1GB of data. Pretty crazy.
I haven’t seen the book in my local Barnes and Nobles yet. Well, I checked two weeks ago. But a friend (@jjx) sent me this picture. So, apparently some book stores have it in stock: | |
| Chrome [vandeneynde.net] [Belgian Security Blognetwork] Posted: 06 Sep 2008 03:15 PM CDT
First of all: No I am not dead and yes I will continue to blog here. I just took a bit of a ‘blogging sabbatical’ the last couple of months. That said, I (and many others so it seems) downloaded Chrome, Google’s vision of a web browser this week and played around with it for a while. A new browser always means new (or old) vulnerabilities and Chrome does not seem to be an exception to this. Google has a pretty good track record in following up on vulnerabilities so they will hopefully fix them soon. On the positive side, it seems that Google really thought about security in Chrome by isolating processes for different tabs and enforcing a security model. They explain most of it in a cartoon you can find here. Although I like the layout, the speed and the software design of Chrome, I will not be moving away from Firefox just yet. Even if all known vulnerabilities were to be fixed, there is one feature in Firefox which I think every browser should have and Chrome hasn’t: a decent password manager. As a security conscious person, I use different passwords for each website I use on the internet. Unfortunately, I can’t remember all of them, so I store some of them in Firefox. I know I could use a tool like KeePass (and I do) but for most sites I find this overkill. Now what I like about Firefox is that you can specify a master password. Without this master password, you cannot unlock the password file (signons3.txt, passwords, and key3.db, the key, in your profile folder). This even survives a copy of the files. When you copy both files to another computer, you still have to specify the master password before getting access to the stored (encrypted) passwords. Now back to Chrome. The profile data (in Vista) seems to be stored in C:\Users\username\AppData\Local\Google\Chrome\User Data\Default. There is an SQLite file called ‘Web Data’ in that folder and this seems to contain the URLs and (obfuscated) saved passwords. Since there is no master password functionality as there is in firefox, this file can be copied to another computer. Doing this gives the other computer access to all websites were there is a password stored for in the file (yups, I verified this). So I’ll stick to Firefox for now | |
| FIT-IT Gesucht: Sicheres und Sichtbares [Raffy - Security Data Visualization] Posted: 06 Sep 2008 03:15 PM CDT
While talking about RAID and VizSec, the conferences are taking place in a week at MIT in Boston. I will be giving a short presentation on DAVIX with Jan Monsch and will also be part of a panel discussion. Looking forward to make my points about visualization there. I am going to stay for RAID and hope to catch up with my former collegues from IBM research. Drop me a note if you are attending as well. | |
| Blind Acceptance of Mediocrity [The Falcon's View] Posted: 06 Sep 2008 11:08 AM CDT | |
| Follow Hack.lu 2008 on Twitter or IRC (updated) [Security4all] [Belgian Security Blognetwork] Posted: 06 Sep 2008 10:02 AM CDT  The hack.lu 2008 conference is nearing. There are several ways to follow or participate (remotely).
| |
| Planned CTF competition for Hack.lu 2008 [Security4all] [Belgian Security Blognetwork] Posted: 06 Sep 2008 06:43 AM CDT  I read that there will be another CTF at Hack.lu just like last year. This years CTF will again be organised by Hackerjoe of the famous Kenshoto group. For a view on last years CTF, read my post on 'Capture The Flag at Hack.lu 2007'. I should have BackTrack 3 Final running by then on my Eee PC 901. I'm working on some tutorials. Soon to follow. Related posts:
| |
| document of the day : Internet governance in the OSCE region [belsec] [Belgian Security Blognetwork] Posted: 06 Sep 2008 06:00 AM CDT This 200p plus book from 2007 gives a good overview of the history and basis of Internet governance on the international level and in some countries. Some specific issues are also tackled even if some of this information may be old by now. | |
| Big Iron is Dead...Long Live Big Iron? [Rational Survivability] Posted: 05 Sep 2008 11:42 PM CDT
Many of them argued "All you need is a COTS PC, package up OS/Applications and voila! Instant appliance! Ready for the edge, ready for the core." Not surprisingly, many of the networking/security/application delivery companies that these folks worked for ultimately introduced custom-engineered hardware solutions, melding their software with custom hardware and COTS elements to produce a piece of big iron of their own... About a year ago, I wrote a blog on this topic highlighted by a post titled "All your COTS multicore CPU's with non-optimized security software are belong to us," in which I extrapolated some very interesting points regarding Moore's law and the hubris surrounding the gluttony of compute power offered by higher density chipsets without the corresponding software architecture to take advantage of it. This is a little tickler to that post. I come from the land of servicing large enterprises, service providers, municipalities and nation states and not the SME. While there are certainly exceptions to the "rule," and it's reasonable to suggest that my perspective is skewed, I've always been careful to ensure I framed my discussions this way, so debating/contrasting the architectural slants of an SME with a Fortune 10 doesn't really move the discussion along any. So, sticking with the large enterprise theme, there are two interesting divergent themes emerging: the centralization of compute and storage with the distributed nature of connectivity and information. Without muddying the water too much about how these scenarios are not all that mutually exclusive, let's stick with the "centralization" theme for a moment. The mainstream adoption of virtualization as an enabler brings us full-circle back around to the centralized mainframe model* of compute, networking and storage. Now that reasonably reliable, high speed and low latency connectivity is available, centralization of resources makes sense since people can generally get access to the assets they require and the performance to get from point A to point B is for the most part acceptable (and getting more so.) Once again, the natural consolidation of functionality and platform architecture follows suit -- we're back to using big iron to deliver the balance of cost, resilience, performance and simplified management that goes along with squeezing more from less. To wit, let's examine some recent virtualization-inspired, big iron plays:
These are just a few examples. Each of these solutions delivers the benefits of hefty amounts of virtualized service, but what you'll notice is that they do so in massive scale, offering consolidated services in high-density "big iron" configurations for scale, resilience, manageability and performance. In this period of the technology maturity cycle, we'll see this trend continue until we hit a plateau or an inflection point -- whether it is triggered due to throughput, power, heat, latency, density or whatnot. Then we'll start anew and squeeze the balloon once more, perhaps given what I hinted at above with clusters of clouds that define an amporphous hive of virtualized big iron. But for now, until service levels, reliability, coherence and governance are sorted, I reckon we'll see more big iron flexing it's muscle in the data center. What about you? Are you seeing the return of big iron in your large enterprise. Perhaps it never left? I for one welcome my new blinking dark overlord... /Hoff * There's even a resurgence of the mainframe itself lately. See IBM's z/10 and Unisys' ClearPath for example. | |
| Botnets sizes have skyrocketed [Security4all] [Belgian Security Blognetwork] Posted: 05 Sep 2008 06:36 PM CDT  Recent statistics from Shadowserver.org are showing that the size of botnets have quadrupled. Possible causes are the latest malware email campaigns like the CNN spam, the infected pages through recent SQL injections and possibly the start of the new school year. This is an opinion, not proof of course. So this translates into more infected PCs under control of the bad guys. More spam, more credit card theft, bigger DDoS, etc.... It doesn't look good. Related posts:
| |
| it's time for Holidays [remes-it] [Belgian Security Blognetwork] Posted: 05 Sep 2008 05:59 PM CDT |
| You are subscribed to email updates from Security Bloggers Network To stop receiving these emails, you may unsubscribe now. | Email Delivery powered by FeedBurner |
| Inbox too full? | |
| If you prefer to unsubscribe via postal mail, write to: Security Bloggers Network, c/o FeedBurner, 20 W Kinzie, 9th Floor, Chicago IL USA 60610 | |











 Next Tuesday I will be speaking in Graz, Austria at the
Next Tuesday I will be speaking in Graz, Austria at the 





No comments:
Post a Comment