Spliced feed for Security Bloggers Network |
| Posted: 18 Sep 2008 03:01 AM CDT Ronen Bachar, from our own IBM Rational AppScan team, gave a presentation on the (*hot*) subject of automated Flash/Flex application security testing, at the recent OWASP IL conference that was held last week (I have a strange feeling of a Deja-Vu). The presentation gives a high level overview of Flash, Flex and the AMF protocol, and dives into some gory details (although some gore is missing from the online presentation) regarding the challenges and possible approaches for performing automated crawling and security testing of web applications that were built using these technologies.
And while we're on the subject of Adobe Flash & Flex web applications - if you happen to be in New York next week for the OWASP AppSec conference, be sure to attend another presentation by our team (Adi Sharabani & Ayal Yogev), on the subject of Flash Parameter Injection. |
| Blackbox vs. Whitebox - OWASP IL Presentation [IBM Rational Application Security Insider] Posted: 18 Sep 2008 01:59 AM CDT Adi Sharabani and Yinnon Haviv, both from IBM Rational Application Security, gave a very interesting presentation on the subject of Blackbox and Whitebox application security scanners, at the recent OWASP IL conference that took place last week. Since our team is working on both technologies, we believe that we can provide an unbiased and thorough overview of the difference between both scanning approaches, and also to point out how they complement each other. You can view the presentation here, or download it from the OWASP IL conference site (will soon be uploaded). We will soon upload another OWASP IL presentation given by our own Ronen Bachar, which talks about the challenges and solutions for automated Flash/Flex application security testing, so stay tuned! |
| Turn off your computer tonight [The Converging Network] Posted: 18 Sep 2008 01:48 AM CDT Chris Dawson at ZDnet links to an article in the Boston Globe about the state saving money by turning off computers at night. From the Globe Staff written article: Massachusetts officials say they have found a simple way to save $2 million a year and reduce carbon emissions by more than 5,000 tons annually: turn off computers that aren't being used. I recently did a podcast and put up a blog post about Power IT Down Day, an awareness day event sponsored by HP, Intel and Citrix to help the federal government save money by powering down users' computers at night. Since then, I've powered all my unnecessary equipment down each night to save energy by turning them off at the power strip. That way laptop and other power supplies don't sit there and still consume power. It's small step but a good practice to get into, and actually it only took a day or two to get used to the change. So turn off your unused computer at home and at work tonight. |
| VMWorld 2008: "Introducing Cisco's Virtual Switch for VMware ESX"... [Rational Survivability] Posted: 17 Sep 2008 07:07 PM CDT
It's the night before VMworld 2008 and the Technology Exchange/Partner day begins and I'm pawing through the stuff in my bag, separating the "keep it" from the "toss it" schwag. There's an innocuous little flyer stuffed in the bag on Cisco letterhead titled "Introducing Cisco's Virtual Switch for VMware ESX." Fantastic. Let's call it the 'cSwitch' ;) A year and a month ago in August of 2007, I blogged about this very thing in a post titled: "VMware to Open Development of ESX Virtual Switches to Third Parties...Any Guess Who's First?" based on a hint from virtualization.info. Given that VMworld 2007 came and went without this announcement, I'm very excited that we're actually going to get a look at what Cisco will offer; I think this is huge news and ultimately offers some profound game-changing (for good and bad) implications on the network and security fronts. I have dozens of questions like: I wonder how much of the Nexus (7000 series)/NX-OS code cross-pollinates over (if any) to this solution and if we'll see capabilities such as STP/PVST+/Private VLANs, HSRP, Multicast, etc. make their way into Cisco's vSwitch and how this virtual switch with integrate/interoperate with the vkernel. Further, as Ed Haletky and I unofficially bet over drinks this evening, I wonder if it will be a direct replacement for VMware's at-boot loadable module or it will co-exist? I bet the former. ;) In addition to the "cSwitch," there are a couple of sessions I am very, very interested in attending given my exposure to VFrame and some Cisco engineers/architects at last year's show: Simplify VMotion with Virtual Machine–Aware Network and Storage Services ESX Server in a Unified Fabric Environment VFrame: Enriching ESX Deployment with End-to-End Orchestration See the second topic above? Remember when I mentioned in prior posts about virtualizing applications directly within the Nexus? Should be a very interesting couple of days. /Hoff Update: So there was no direct news/mention specifically of Cisco today in any of the distributed virtual networking (DVN) sessions -- there's a lot of messaging collisions because the re-branded 'v-everything' strategy has things being renamed. Hopefully we'll see/hear more from Cisco tomorrow. Many of the underlying functions that will enable 3rd party virtual switches as well as any network interface to the vkernel via API were discussed today under the capabilities described by vNetwork (this includes the vNetwork Appliance API's and what you've known as VMsafe.) You can see more about vNetwork here in this post. All I can say is that I got a lot of my suspicions confirmed, questions answered and conclusions affirmed in today's sessions. Some good, some bad. It's going to be a bumpy ride, kids. The Four Horsemen live! ;) |
| The Network Is the Computer...(Is the Network, Is the Computer...) [Rational Survivability] Posted: 17 Sep 2008 07:04 PM CDT
The precipitate convergence of virtualized compute, network and storage is really beginning to take significant form; after five hard years of hungering for the materialization of the technology, enterprise architecture, and market/business readiness, the notion of a virtualized datacenter OS with a value proposition larger than just " cost-optimized infrastructure" has now become a deliciously palpable reality. The overlap and collision of many leading technology providers' "next generation" datacenter (OS) blueprints is something I have written about before. In many cases there's reasonable alignment between the overall messaging and promised end result, but the proof is in the implementation pudding. I'm not going to rehash this here because I instead want to pick on something I've been talking about for quite some time. From a network and security perspective, things are about to (again) fundamentally and profoundly change in terms of how we operationally design, provision, orchestrate, manage, govern and secure our infrastructure, applications and information. It's important to realize that this goes way beyond just adding a 'v' to the name of a product. What's incredibly interesting is the definition and context of where and what makes up the "network" that transports all our bits and how the resources and transports interact to deliver them securely. It should be clear that even in a homogenous platform deployment, there exists an overwhelming complex conglomerate of mechanisms that make up the machinery enabling virtualization today. I think it's fair to say that we're having a difficult time dealing with the non-virtualized model we have today. Virtualization? She's a cruel mistress bent on reminding us we've yet to take out the trash as promised. I'm going to use this post to highlight just how "complexly simple" virtual networking and security have become using as an example the last two days' worth of announcements, initiatives and demonstrations of technology and solutions from Intel, VMware, Cisco and the dozens of security ISV's we know and love. Each of the bumps in these virtual wires deserves its own post, which they are going to get, especially VMware's vNetwork/VMsafe, distributed network switch, and Cisco's Nexus 1000v virtual switch announcements. I'm going to break each of these elemental functions down in much more detail later as they are simply amazing. Now that networking is abstracted across almost every layer of this model and in many cases managed by separate organizational siloes and technologies, how on earth are we going to instantiate a security policy that is consistent across all strata? We're used to this problem today in physical appliances, but the isolation and well-definable goesinta/goesouta perimeterized boundaries allows us to easily draw lines around where these policy differentials intersect. It's used to be the devil you knew. Now it's eleven different devils in disguise. As you visualize the model below and examine how it applies to your experience, I challenge you to tell me where the "network" lives in this stack and how, at a minimum, you think you're going to secure it. This is where all those vendor roadmaps that are colliding and intersecting start to look like a hodgepodge: In the example model I show here, any one of these elements -- potentially present in a single VMware ESX host -- can directly or indirectly instantiate a set of networking or security functions and policies that are discrete from one another's purview but ultimately interrelated or even dependent in ways and using methods we've not enjoyed before. In many cases, these layered components are abstracted from one another and managed by separate groups. We're seeing the re-emergence of network-centricity, it's just that the network is camouflaged in all its cloudy goodness. This isn't a story where we talk about clearly demarcated hosts that plug into "THE" network, regardless of whether there's a hypervisor in the picture.
Here's where it gets fun... In this model you have agents in the Guest OS interacting with security/networking virtual appliances on the ESX host either inline or via vnetworking APIs (switching or security) which in turn uses a fastpath networking kernel driver connected to VMware's vSwitch while another VA/VM is connected to a Cisco Nexus 1000v vSwitch implemented as a second distributed virtual network switching fabric which are all running atop an Intel CPU utilizing SR-IOV via VT-d in the chipset which in turn allows VM's to direct attach (bypassing the VMM) to NIC cards with embedded switching connected to your network/storage fabrics... Mass hysteria, cats and dogs living together... So I'll ask you again: "Where's the network in that picture?" Or, more precisely, "where isn't it?" This so hugely profound, but that may because I've been exposed to each of the bubbles in this diagram and see how each of them relate or do not. When you step back and look at how, as an example, Cisco and VMware are both going through strategic sea changes in how they are thinking about networking and security, it's truly amazing but I think the notion of network intelligence is a little less cut and dry as some might have us believe. Is this as mind-blowing to you as it is to me? If not, wait until I rip open the whole vNetworking and Nexus 1000v stuff. Very, very cool. /Hoff |
| Google and GE Think Green but Is There Enough Research? [The Converging Network] Posted: 17 Sep 2008 05:44 PM CDT Google and GE announced today they are collaborating to help promote the development of more power transmission lines for wind farms, smart-grid technology, software for a more flexible power grid that can accommodate demands of hybrid vehicles, and geothermal visualization software. I know one of the big issues for wind power generation is getting the generated power transmitted from wind farms to cities where it's needed. There's a good sized wind farm north of Ft. Colins (north of Denver) but from what I've heard, it's growth limited because the power transmission runs east and west, and doesn't have enough capacity to deliver the power south to the Denver area. But one of the disturbing factoids I saw in the CNET article was from GE's CEO. "Immelt [GE CEO] noted that the energy business typically spends about 1 percent of revenues in research and development, compared to 7 percent in health care." 1% investment in research? Yikes, that's atrocious. Not only does congress need to renew the tax credit incentives for renewable energy investments, we need to demand our energy companies heavily invest in renewable energy. Why isn't Xcel Energy building transmission lines so we can have more wind farm power generation? What about government incentives for other investments? To become the renewed kind of USA Tom Friedman talks about in Hot, Flat, and Crowded, our investment and startup capital has got to drastically move into renewable energy and technologies. I'm sick of the extreme green makeover TV commercials by Exxon Mobile purporting them as somehow doing great research into alternative energies. Don't get me wrong, I'd love it if the oil companies really did invest heavily into developing alternative energies and technologies, but I find their TV commercials trying to just do an image makeover offensive. I do applaud Google and GE for taking a stand and collaborating in the private sector. |
| Hey, it can happen to anyone ;-) [StillSecure, After All These Years] Posted: 17 Sep 2008 02:40 PM CDT 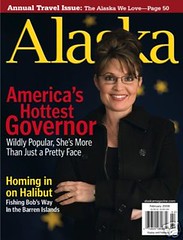 I had to at least smile reading this article by Ryan Naraine in ZD Net today. It seems that private email account that Sarah Palin was using to conduct State of Alaska business was in fact her own Yahoo mail account. Today some group of anonymous hackers broke into and posted Governor Palin's emails. After what I have been through all I can say is, it can happen to anyone ;-) In case anyone from Mrs. Palin's office is interested, I am willing to come up to Alaska and help them deal with getting their Yahoo account back under control. It could take a few days. Also let me recommend a good password manager and upgrading the strength of all of your passwords. Moose would probably not be a good password, but m00$e might be better for instance. Also I would change the ebay password before someone buys back that state owned jet ;-) I guess it is a lucky thing John McCain doesn't do computers and email. ![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=8d6c7d9c-cdfe-4d4e-95c5-658ddaa00c97) |
| Think Like An Attacker? [Emergent Chaos] Posted: 17 Sep 2008 11:49 AM CDT One of the problems with being quoted in the press is that even your mom writes to you with questions like "And what's wrong with "think like an attacker?" I think it's good advice!" Thanks for the confidence, mom! Here's what's wrong with think like an attacker: most people have no clue how to do it. They don't know what matters to an attacker. They don't know how an attacker spends their day. They don't know how an attacker approaches a problem. Telling people to think like an attacker isn't prescriptive or clear. Some smart folks like Yoshi Kohno are trying to teach it. (I haven't seen a report on how it's gone.) Even if Yoshi is succeeding, it's hard to teach a way of thinking. It takes a quarter or more at a university. I'm not claiming that 'think like an attacker' isn't teachable, but I will claim that most people don't know how. What's worse, the way we say it, we sometimes imply that you should be embarrassed if you can't think like an attacker. Lately, I've been challenging people to think like a professional chef. Most people have no idea how a chef spends their days, or how they approach a problem. They have no idea how to plan a menu, or how to cook a hundred or more dinners in an hour. We need to give advice that can be followed. We need to teach people how to think about security. Repeating the "think like an attacker" mantra may be useful to a small class of well-oriented experts. For everyone else, it's like saying "just ride the bike!" rather than teaching them step-by-step. We can and should do better at understanding people's capabilities, giving them advice to match, and training and education to improve. Understanding people's capabilities, giving them advice to match and helping them improve might not be a bad description of all the announcements we made yesterday. In particular, the new threat modeling process is built on something we expect an engineer will know: their software design. It's a better starting point than "think like a civil engineer." |
| A NAC in hand is worth two in the bush [StillSecure, After All These Years] Posted: 17 Sep 2008 09:14 AM CDT Mike Fratto, fresh off hosting the NAC festivities at NY Interop (wanted to make it up there but had to go to St Louis instead) has an interesting article up called "Beating the NAC Standards Bush". Mike relates his experience hosting a panel of paid sponsors for NAC day. Like other fairy tales, this story has three characters, one was Cisco (too big), one was Sophos (too small) and one was Symantec (just right). The discussion on the panel, as invariably happens at Interop got around to NAC standards. Of course Cisco is Cisco and is working with IETF. So what if it moves on geological time frames. Symantec and I guess Sophos are part of the TCG/TNC (as is StillSecure, in the spirit of full disclosure). It seems some people gave Rich Langston of Symantec a tough time because the TCG is a "closed" group, as opposed to the IETF. Rich responds that the closed group allows them to move forward faster and more efficiently. At the end of the day, Mike says customers want "a standard" to come to the forefront and don't care much which one it is, as long as it is one. He seems to be partial to the TCG. My view as in the title, is it is more important today to get a NAC product that works. People are tired of the alphabet soup of NAC standards. Though Symantec and 45+ others are members of the TCG, the perception is that it is still the Juniper standard. Yes, it would be nice to have a dominant standard and I hope it is the TCG standard too. But Mike is right on with his last sentence in the article. Only when customers are truly making decisions based upon these standards will NAC vendors fully support them. |
| Getting fired due to a breach? [Data-Centric Protection and Management] Posted: 17 Sep 2008 07:53 AM CDT Just got an email inviting me to a seminar - hosted by SecureState. But what caught my eye was this statement, "7 out of every 10 breaches ends with someone losing their job" I was shocked! 70% of all breaches result in the firing of someone involved in the breach? Or is it the failure to defend this breach resulting in the CISO losing her/his job? I had never seen this research before and did not know this problem was so acute. Be very interested to know the source of this research. The seminar information is here. Will post again when I find out more... |
| Interesting way to put it [Vitalsecurity.org - A Revolution is the Solution] Posted: 16 Sep 2008 02:47 PM CDT This. In particular, "In addition to independently lead investigations, EstDomains, Inc relies on the information available from such influential anti-malware organizations and listings as webhelper4u.net, malwaredomainlist.com, hosts-file.net, malwaredomains.com, malwarebytes.org and many others." That sounds very much like there's some sort of formal arrangement or datashare in place, and less like "some random dude turned up on a couple of forums or whatever after Brian Krebs wrote about stuff for a while". |
| The Beatdown Stick Awards [Vitalsecurity.org - A Revolution is the Solution] Posted: 16 Sep 2008 02:13 PM CDT Okay, I've randomly decided to have a vote on who should be awarded the Beatdown Stick for having suffered the most at my cruel, cruel hands. Shall we begin? Helgib: What happens when I pretend to be Batman and take down a huge-assed hacking ring from the inside? The answer is, of course, hilarity for all. Not only did I turn it into a form of interactive spyware hunting (Do you want them punished or let off the hook? YOU DECIDE!) I served up an evening of what was no doubt sheer terror for the poor kids involved. You can see the whole epic tale here, but all you need to know in a nutshell can be summed up by Helgi himself once the penny finally dropped:  ...says the phisher / hacker / scumbag ring extraordinaire. The Punisher: What happens when you use the same username for your hacking as you do for your Myspace trolling? The answer is, of course, that you crap your pants. The following screenshot says it far better than I ever could:  Important safety tip, kids: When naming yourself after comic characters, pick Batman to slightly increase your chances of success. Yogangster50: In some alternate Universe, there is a hacker called Yogangster50. He is rich, he is surrounded by hot women (who are probably naked go-go dancers) and he alone commands the hackers of the world. His skill is beyond reproach, his reputation immaculate. White hats fear him, black hats avoid him for his word is law. Unfortunately, we got the "now with 100% extra suck" edition who was still undergoing a course of LERNIN2INTERNET when I happened to come across his hacking exploits on Youtube. Yogangsta50 quickly became the poster boy for how not to hack. I also broke his brain:  .....which only helped seal his "Living Legend" status, though probably not in the way he'd hoped. Mark Arruda: This is the guy who was sticking Zango installers on a bunch of Myspace pages. I'd rather select him than Zango as the contender for the Beatdown Stick Awards, because he's a great example of how affiliates don't seem to understand the technology they play around with on a day to day basis. Speficially, claiming he's "had no involvement with Zango for some time now" while thinking I'd be dumb enough not to, you know, check the sites in question to see if he's telling the truth or not. Also, the final paragraph is loltacular. Trust me on this. Rahul: This guy was the main point of contact with regards trying to shut down Helgis forum for good. Imagine my dismay, then, when it seemed "Rahul" was doing everything in his power to keep the forum they were hosting up and running as long as he possibly could. I smelt something fishy and sure enough, it turned out there was some dealing going on behind the scenes. In a vaguely cheeky moment of bravado, I gave him 60 minutes to shut down the website OR ELSE. Oh, the excitement.... "Hackboy": You know what makes me laugh? When people claim to be in Anonymous, then go around with their face all over the place. You know what makes me annoyed? When those same people mix an unhealthy dose of arrogance with a general sense of invincibility. I eat invincibility for breakfast. I still have that Youtube vid open on a laptop, too. Finnish It: Oh dear, someone decided to play arrogant hacker (there's a theme here somewhere) and set up a bunch of websites for scumbags to play around on. Unfortunately for him, he wasn't too smart about it and enjoyed a helping of Epic Fail. That concludes the selection. There were one or two others I considered throwing in, but the above provided the most hilarity (they did for me, anyway). Voting is open until Sunday, 11PM... |
| Let's talk Software Serviceability [Jeremiah Grossman] Posted: 16 Sep 2008 01:25 PM CDT Financial Times graciously invited me to write an opinion piece for their publication entitled "Learn from today's software flaws to protect corporations tomorrow", where I discuss a bit about Software Serviceability. In the wake of Dan K's vulnerability announcement (and others like it), I couldn't shake the notion that no matter how hard to try to write perfectly secure code, given a long enough time line we'll always fall short. We will miss a bug, there will be a new attack technique, hackers will exploit our systems. To me this says our important systems must have speedy and adaptive security measures to identify threats as they happen and the ability to quickly service our deployed software (preferably within days or hours). Some systems have this capability, but it's too few and far between. "So in the case of the issues found by Dan, Tony, and Alex it is hard to put a top-end market value on them, but consider that other less severe issues have sold for five and six figure sums. Would seven figures be out of the question? Will the next security researcher be influenced by the potential financial reward instead of giving it away for free? We know for sure that there will be a next time, because software is imperfect. Vulnerabilities will be found and long standing encrypting algorithms will be broken or at least weakened. And it's difficult, if not impossible, to future-proof our code against attack techniques that don't yet exist." |
| Testing,testing,1,2,1,2 [IT Security: The view from here] Posted: 16 Sep 2008 01:09 PM CDT 4 or 5 years ago a friend of mine approached me with the idea of going into the penetration testing business: "Let's go into the penetration testing business", he said, and we did some market research. We could buy the required tools, a server, a shed, and a reasonably large internet connection, install a free copy of Nessus and be up and running by the end of the week. Of course we looked a little further than that, and realised that everyone and his dog was already doing it, and like every other business, it was just a case of whoever was shouting the loudest would make the biggest bucks. Steve and I were total techheads and neither particularly interested in making noise at the time, so we went back to the day jobs... A couple of years later, a new friend at a new company asked me about my background. We got around to talking about my close call with pen testing and he said: "yep, I thought about that for a while, no money in it." All of us remain firmly under the employ of other entrepreneurs, some large, some small, but none of them us. Today I saw a quote from a pen testing company, not one for dropping names, let's just say they do secure tests. My jaw dropped when I saw the price for 4 days work. An amazing return for them, but just like Starbucks charge more for a coffee I could make at home because of their ability to make it in bulk and present it better than I can, so they can do a much better job than we can, make a pretty report, tailored to our needs, and there's probably negligible real cost difference to us anyway. Not that we could do our own tests, but it did strike me that the only reason we have to do them anyway is because our security team (now disbanded) had identified the need in the first place... The MD of this testing company often writes for a magazine that I have written for in the past. He shouts louder than I do, and makes his presence known. He's also very good, knows the market and knows what makes a good product. I'm not sure I could have built a business out of it in such a cutthroat market. Still, it would have been nice, wouldn't it? |
| SDL Press Tour Announcements [Emergent Chaos] Posted: 16 Sep 2008 12:15 PM CDT Steve Lipner and I were on the road for a press tour last week. In our work blog, he writes: Last week I participated in a “press tour” talking to press and analysts about the evolution of the SDL. Most of our past discussions with press and analysts have centered on folks who follow security, but this time we also spoke with publications and analysts who write for software development organizations. I was struck by the extent to which the folks who focus on development have been grappling with many of the issues about developing secure software that we’ve focused on here at Microsoft.The announcements are here. I am particularly excited about the third announcement, the availability of the SDL Threat Modeling Tool v3. |
| "That. Is. Officially. Fantastic." [Vitalsecurity.org - A Revolution is the Solution] Posted: 16 Sep 2008 10:16 AM CDT |
| DRM In The Cloud [Information Centric Security] Posted: 16 Sep 2008 10:07 AM CDT |
| You are subscribed to email updates from Security Bloggers Network To stop receiving these emails, you may unsubscribe now. | Email Delivery powered by FeedBurner |
| Inbox too full? | |
| If you prefer to unsubscribe via postal mail, write to: Security Bloggers Network, c/o FeedBurner, 20 W Kinzie, 9th Floor, Chicago IL USA 60610 | |
No comments:
Post a Comment