Spliced feed for Security Bloggers Network |
| Wall Street bailout - Do we need it? [StillSecure, After All These Years] Posted: 25 Sep 2008 06:44 AM CDT Writing this one on the plane, where I just watched President Bush address the American people on why the Wall Street bailout plan is necessary. I think that the President actually did a good job of explaining how we got in this mess, what the consequences are of doing nothing are and even a decent job of explaining what his plan will try to do. He also was very clear about the fact that he is willing to accept changes to the plan suggested by a bi-partisan Congress. All of this is good but frankly scares the hell out of me! Things must be truly bad to bring about such a coalition as we have forming here. In that case I hope that what they have to do, they do quickly and smartly. With everyone suspending everything to see this crisis through and put their 2 cents in, I wanted to put mine in too. For my part I would like to see something in the oversight of the financial industry that says all of these financial institutions must do something about information security and data protection. Personally I think requiring intrusion detection/prevention, vulnerability management and network access control (especially if they all work together) for each each of these companies should be part of the package. Of course if they do require that, I demand that they have no limits on the compensation paid to security company executives ;-) Related articles by Zemanta | |
| European data retention : protest are organizing [belsec] [Belgian Security Blognetwork] Posted: 25 Sep 2008 04:18 AM CDT | |
| USA EGOV best projects [belsec] [Belgian Security Blognetwork] Posted: 25 Sep 2008 04:09 AM CDT 2008 Best Practices in the Use of Information Technology in State Government Released in conjunction with NASCIO's 2008 Best Practices in the Use of Information Technology in State Government Awards, this booklet contains summaries of innovative state government programs in the following areas: Business Continuity and Disaster Recovery ; Cross-Boundary Collaboration and Partnerships; Data, Information and Knowledge Management; Digital Government – G to B; Digital Government – G to C; Digital Government – G to G; Enterprise IT Management Initiatives; Information Communications Technology Innovations; Information Security and Privacy; and IT Project and Portfolio Management. http://www.nascio.org/publications/documents/NASCIO-2008Awards.pdf | |
| the stupidity of putting everything on email [belsec] [Belgian Security Blognetwork] Posted: 25 Sep 2008 04:06 AM CDT The scandal around our interior minister is only starting. After the top of our policeforce it is now his cabinet that is coming in the searchlight of the parliament and the press. Several of his collaborators have resigned yesterday, among which his press officer. Normally he will have several press officers so this wouldn't be that disasterous. But the real angle is always in some words - and the reading behind the lines. When the minister sanctioned someone of the top of the policeforce because he didn't abide by the strict interpretations of the laws and statutes in the promotion of some secretaries to highlevel positions, the police officer responded that he had emails from the cabinet of the minister that instructed him to do exactly that. This is very smart. Writing illegal instructions in an email. Never write in an email what you wouldn't write in a letter. Period. There is no difference. And never accept that email doesn't follow the same procedures as letters. Email is no different nowadays. | |
| Free today PDF to html [belsec] [Belgian Security Blognetwork] Posted: 25 Sep 2008 03:37 AM CDT PDF to HTML is an easy-to-use software for converting PDF into HTML. The software supports all Adobe PDF modifications. The PDF to HTML converter retains the layout, images, text and formatting of the original PDF file. PDF to HTML is a highly efficient standalone software which doesn’t require Adobe Acrobat or Adobe Acrobat Reader installed. You do not need any special skills to operate the software. Just drag and drop the document you want to convert to the main PDF to HTML window and click Start Conversion. | |
| Links for 2008-09-24 [del.icio.us] [Anton Chuvakin Blog - "Security Warrior"] Posted: 25 Sep 2008 12:00 AM CDT | |
| Security Provoked Video Episode 7 [Security Provoked] Posted: 24 Sep 2008 09:23 PM CDT | |
| IDS/IPS - is it Vitamins? [Musings on Information Security] Posted: 24 Sep 2008 08:35 PM CDT Alan Shimel's post on "IDS - the beast that just won't die" triggered my hidden thoughts about IDS. Rather than thinking about IDS as a piece of device/software that provides fancy features. Let me try to summarize some assertions about IDS:
| |
| US Custom agents can now also seize hardcopy document [Security4all] [Belgian Security Blognetwork] Posted: 24 Sep 2008 07:57 PM CDT  We know that digital 'searches' were possible at (US) border control. Now it seems that all documents, even hardcopy can be seized, read or copied at will. From SFGATE: The Bush administration has overturned a 22-year-old policy and now allows customs agents to seize, read and copy documents from travelers at airports and borders without suspicion of wrongdoing, civil rights lawyers in San Francisco said Tuesday in releasing records obtained in a lawsuit.Previous articles: (Photo under creative commons from Mark Demeny's photostream) | |
| (IN)SECURE Magazine Issue 18 released [Security4all] [Belgian Security Blognetwork] Posted: 24 Sep 2008 07:34 PM CDT  Covered topics are:
| |
| Google’s Project 10ˆ100 [Amrit Williams Blog] Posted: 24 Sep 2008 07:28 PM CDT As part of their 10 year anniversary, Google is offering $10million for the next great idea (here), the FAQ is (here)…
I have already submitted the idea of an organization that includes representative countries around the world that can come together in a single place and discuss issues that impact everyone, such as peace & security, economic & social development, human rights, humanitarian affairs, and of course international law. Additionally I suggested a method of government where the supreme power is held by the people under a free electoral system where every person is provided fair and equal representation and the ultimate responsibility of the elected officials is to the people themselves. Finally I submitted an idea for edible garbage - I am so going to win!  | |
| E-discovery, belgische politie en comité P [belsec] [Belgian Security Blognetwork] Posted: 24 Sep 2008 04:50 PM CDT De Belgische politie is in een aantal schandalen verwikkeld waarover een externe inspectiedienst in opdracht van het parlement een aantal onderzoeken heeft gedaan. Het is momenteel niet duidelijk of het roddels zijn, maar uit de onderzoeken blijkt wel dat om bepaalde dames in hogere posten te benoemen dan wettelijk mogelijk is er - al dan niet met medeweten van o.a. de minister - wetten zijn overtreden. Of hier ook nog sex mee te maken heeft is een ander paar pantys. Wat wel opvalt in de rapporten is dat uitgezonderd de ondervragingen - zelfs onder eed - de onderzoekers op geen enkel moment zelf het emailverkeer en de emails zijn gaan onderzoeken tussen de beschuldigden/betrokkenen. Aangezien er momenteel in de Belgische administratie geen enkele verplichting is met betrekking tot het bijhouden van dergelijke emails en het dus niet zeker zou zijn of alle emails zouden zijn bijgehouden, zouden deze emails geen sluitend bewijs geweest zijn, maar ze zouden wel indicaties kunnen zijn en kunnen geholpen hebben bij de ondervragingen en de opvolging van de antwoorden. Nu blijkt dat sommige van de hoofdpersonen die geschorst of vervolgd zullen worden in interviews verwijzen naar emails of emailverkeer over de betrokken zaak en waarin zij rugdekking zouden vinden (en dus een hogere politieke of administratieve verantwoordelijkheid). In De Morgen stond dit vandaag "Dedecker citeert de woorden van Closset: "De diensten van de Algemene Inspectie hebben, wat betreft de aanwerving van mevr. Debeck, toen adviseur op het kabinet van de minister, nauwgezet de instructies gevolg die ze via mail hadden ontvangen van drie leden van het kabinet van de minister." In de volgende blog vindt je trouwens meer informatie over emailarchivering. | |
| Interesting Information Security Bits for 09/24/2008 [Infosec Ramblings] Posted: 24 Sep 2008 04:00 PM CDT Good afternoon everybody! I hope your day is going well.
That’s it for today. Have fun!  | |
| Simple Universal Authentication System [GNUCITIZEN] Posted: 24 Sep 2008 03:29 PM CDT This idea is perhaps stupid. Nevertheless, I rather document it here for good than not documenting it at all. Here is the story. I had to reset the credentials of an online account I have. As usual, I went on the vendors’ site, clicked the forgotten password feature, typed my email address and clicked I am so used to this routine that I no longer think when performing it. It takes me virtually 20 seconds to get my account back. It is not a secret that once an attacker has access to an inbox, s/he can easily obtain access to other sites/applications the victim has registered with the compromised email. However, what if we turn this well know principle to solve a quite rudimentary and very old problem - authenticating on the Web. Let me explain. Technically speaking your inbox is an universal authentication system. Mail and HTTP are so tight nowadays that they cannot function normally without each other. We use SMTP to reset forgotten password credentials, which basically works like this: we receive a one-time password (in the form of a link with a token), which we use to create a username/password pair. Alright then. Instead of going through the a middle man (your username/password pair) why don’t we use the password reset mechanism to authenticate with the any web enabled system? It will work like this. First, when you signup you just type your email address, nothing more. You receive an email with a link to login. You login and you do your thing then you log out. At some point in the future you decide to come back to the system. You type your email address again and you receive another link in your inbox to login. Limitations and Security ImplicationsI started this post by saying that this is merely an idea and I wont recommend it to anyone at this stage, although if implemented correctly, the solution may actually work. There are many things that needs to be considered. First, tokens have to be expired once they are used. Second, we need some kind of self-destruct feature in order to prevent authentication spam. 3rd, it wont be obvious when one of your accounts is compromised. Today, if one of your accounts is compromised via password reset you can detect that something wrong is going on due to the fact that you cannot login normally anymore. However, this only have implications in the long term. Some Benefits on the Top of my HeadWell, it is trivial to implement very strong authentication systems on the top of this framework. PKI is what comes to mind. Imagine the following. When the application authenticates with you, you receive the message encrypted with your public key. The only way to read it is to have your private key at hand and this is much better way of authenticating then using simplistic and prone to failure username/password-based authentication mechanisms. Some Words About AccessibilityObviously, this approach is not very convenient. However, the process can be abstracted to the extend where the user doesn’t have to do or know anything. Of course, security might be an issue. There you have it. | |
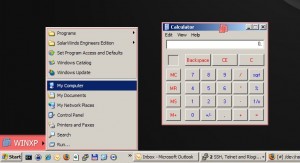
| New VMware Workstation Feature: Unity! [/dev/random] [Belgian Security Blognetwork] Posted: 24 Sep 2008 01:38 PM CDT
VMware Workstation 6.5 is out! One of the new features is a display mode similar to the “seamless” mode in VirtualBox! For those who are not aware of this feature, it allows you to “hide” the guest machine main screen encapsulated in a windows and open applications directly on the host GUI! Here is an example of a Windows XP guest running in another Windows XP screen: The guest’s graphical objects have a red border and a VMware logo in the titlebar (this is customizable). Note that only 6.5 virtual machines can use this mode (you need to convert your old VMs first!). | |
| Bluetooth Headset Vulnerabilities Reminder… [Nicholson Security] Posted: 24 Sep 2008 12:35 PM CDT As I find another one of my hands-free bluetooth headsets in the washing machine again (yes, again, I think this is #11 or #12) I wanted to remind everyone about the risks associated with using bluetooth devices. With the new laws here in California that require drivers to use hands-free devices while driving, I’m starting to [...] | |
| The Training Events are Up [GNUCITIZEN] Posted: 24 Sep 2008 11:22 AM CDT If you are following with the latest updates on GNUCITIZEN you’ve probably noticed that we have most of our training events up now. You can even book online, which is neat. At GNUCITIZEN we try to organize local training events almost every week where we teach the arts of offensive and defensive information security practices and research. All of our course offerings, even the core ones, are based on our extensive research work so there is a lot to learn. We’ve got a couple of events lined up already and I was wondering if anyone may be interested in joining us. As usual, we are all about quality, which means that we try hard to give the best of us. I personally enjoy the events as they are an excellent opportunity to meet some great people with great personalities. I try to learn something myself on these training events although I am lecturing. | |
| Can the big European banks be saved [belsec] [Belgian Security Blognetwork] Posted: 24 Sep 2008 02:53 AM CDT | |
| OT: Workflow for Interesting Bits posts… [Infosec Ramblings] Posted: 23 Sep 2008 08:30 PM CDT This weekend I decided I wanted a more automated way to publish my ‘Interesting Information Security Bits’ posts. To do that I decided I needed two things 1) a workflow process and 2) some tools to do the dirty work for me. So that is what I set out to setup. The rest of this post gives details of the work flow and the script that I came up with to create the posts. Workflow I decided to use Delicious to collect the things that I want to appear in the posts. They were going to end up there anyway and an API exists to get at them in an automated fashion. In order to be able to selectively get just the posts I wanted for a given day, I had to come up with a tagging scheme that would differentiate these bookmarks from any others I might save. I did this by tagging them by date, in YYYYMMDD format, and with ‘iisb.’ For this first iteration of the script, I am only using the date portion. The iisb tag will be used later as I expand this effort. So my workflow goes like this:
A couple notes about how I bookmark things on Delicious. I use the Firefox add-in for this. It makes it so much easier. When I bookmark something, I make sure to enter a description. This becomes the text explaining why I think that particular item is interesting. Finally, I also tag the item with other tags. These tags are for my personal use and also will be used in future expansions of the script. So, now I have a bunch of things that I believe are interesting that I want to tell all of you about. Instead of having to spend a lot of time with a blog post editor, I simply login to my linux machine and execute ./dailypost.pl Tada, magical blog post. This script is written in perl because that’s the language I can churn things out quickly in at this time. It uses several CPAN modules, but the most important ones are Net::Delicious and WordPress::XMLRPC. Why reinvent the wheel. Eventually, the posting part will be automatic using cron, but I still have some things I want to do before I turn it loose. For those interested in the guts of the script, here it is. It consists of the dailypost.pl perl script and a config file. Obviously, replace my comments below with your info if you want to try it. I currently have it set to create the posts as drafts and I then go and publish them manually. Again, this is because this is a pretty young process. Config file (must be named dailypost.cfg and in the same directory as the script at this time) [delicious] user="username" pswd="delicious password" count=100 [wordpress] prefix="What you want the opening to be." postfix="What you want the ending to be." category="WordPress category" title="post title prefix. The date will be appended" publish=0 username="username" password="wordpress password" xmlrpcurl="http://<your site>/xmlrpc.php" Script. (I apologize for the complete lack of comments. Quick and dirty was what I was after.) That’s basically it. I’m happy to have discussion about this with anyone who has questions and feel free to take and use anything you want. I am also happy to email the config file and script to anyone who wants it. Just drop me a note a kriggins _at_ infosecramblings.com. Kevin Posted in Tips Tagged: autopost, delicous, xmlrpc | |
| Dismantling an XML-Bomb [Didier Stevens] [Belgian Security Blognetwork] Posted: 23 Sep 2008 04:49 PM CDT No breaking news in this post, but I’ve found enough applications vulnerable to XML-bombs and not enough awareness around it, that I feel it justifies another web page documenting the principles behind it, together with suggestions to protect your applications from it. The XML-bomb is a small XML document designed to expand to a gigantic size when parsed by an (unprotected) XML-parser. The huge amount of resources (memory) consumed when parsing the XML-bomb can cause a DoS or BoF. Take this simple XML document:
And take this Document Type Declaration defining an entity e0 with value A:
Including this DOCTYPE in our simple XML document enables us to reference entity e0 in our document, for example like this:
When this document is parsed by an XML-parser supporting DTDs, the entity reference is replaced by its value. Here is Internet Explorer rendering our XML document:
Notice that &e0; has been replaced by A. This entity definition and referral mechanism is one essential ingredient of an XML-bomb. The second ingredient is an expression that will grow exponentially and consume huge amounts of resources when evaluated. We define a second entity, e1, referring twice to our first entity e0:
Include this definition in our XML document:
And this is how it is parsed:
e0 evaluates to A e1 evaluates to AA Now define e2 referencing e1, e3 referencing e2, …, and then we get e2 evaluates to AAAA e3 evaluates to AAAAAAAA … We have achieved exponential growth! An XML-bomb with 31 entities is less than 1K in size, but entity e30 is 1GB (2^30 bytes) in size when it gets evaluated by the XML-parser! How do you protect your application from an exploding XML-bomb? If you don’t need support for DTDs, just disable DTDs or use a parser without DTD support. If you need support for DTDs, try to prevent XML-bombs from entering your XML-parser by known-pattern scanning (like classic antivirus software does, for example an application firewall) or limit the impact of an expanding XML-bomb by hardening your XML-parser by restricting its consumption of resources. You’re aware of the limitations of known-pattern scanning. This is a text-book XML-bomb, with exponential growth finding its origin in the binary tree structure. But there are many other data type structures …  | |
| Love what you do [Room362.com] Posted: 23 Sep 2008 03:54 PM CDT | |
| Introducing the Ecommerce Evangelist Blog by Bob Angus [Tim Callan's SSL Blog] Posted: 23 Sep 2008 03:36 PM CDT I'm very pleased that the ranks of the VeriSign bloggers have recently been joined by VeriSign SSL product marketer Bob Angus. Bob shares the insights from more than twenty years selling and marketing Internet and software products, including a wealth of experience in e-commerce enablement. Bob describes the Ecommerce Evangelist blog this way: The Ecommerce Evangelist is about what our customers do. Bob looks like he's already off to a strong start. His most recent entry is Three of the 24 Tactics You Can Do to Make More Money Next Week. | |
| Interesting Information Security Bits for 09/23/2008 [Infosec Ramblings] Posted: 23 Sep 2008 02:32 PM CDT Good afternoon everybody! I hope your day is going well.
That’s it for today. Have fun!  | |
| Posted: 23 Sep 2008 01:03 PM CDT I talked about Pecha Kucha a few times before. The concept is simple, 20 slides 20 seconds per slide amounting to 6m 40s to deliver your message. Other concepts like elevator speech come to mind. There is a similar movement called ignite. With a bit simpler name, what is ignite?
More information on http://ignite.oreilly.com/ Matt is known from the 'Where the hell is Matt' website. Matt started a website showing videos of him dancing on locations all over the world. If you don't know him or his website, you should watch his latest video. Related posts:
| |
| Posted: 23 Sep 2008 12:43 PM CDT It's been a bit of a bumpy ride on the Dutch part of the internet over the last couple of days. One blog - www.geencommentaar.nl - decided to set up something I like to call a 'web 2.0 honeypot' in the form of a petition. The idea behind this was to attract the attention of the biggest blog in the Netherlands - www.geenstijl.nl - and get GeenStijl readers to comment. GeenCommentaar logged the IP addresses of users who made offensive comments on the blog and created a database. (A lot of the offensive comments came from GeenStijl users). Other bloggers could then check the database to see if a particular IP address had been tagged as offensive. Supposedly the idea behind this was to make life easy for other site/ blog owners, by offering an automatic way to filter out (probably) unwanted comments/ content. When GeenStijl realized what was happening, they responded with a vengeance by adding a piece of Javascript to their page. This meant when anyone visited the GeenStijl site, a random IP address was generated, and the GeenCommentaar database would be queried to see if the IP address had been tagged as offensive. All of this was done automatically and without visitors to the site knowing anything about it. The result? GeenCommentaar's server couldn't handle the load; as well as GeenCommentaar getting hit, some other sites running on the same server were overloaded. In addition to the obvious ethical objections, both the parties involved are breaking the law. BTW Kaspersky Lab added detection for this DDoS script as Trojan-Clicker.JS.Small.p . If you want to read more about it please look at my colleague Roel's comment at Kaspersky Virus Analyst's Diary or read my own comments in Dutch at webwereld.nl A lot of people seems not to think anymore about what seems to be good or bad on the internet. They just act and play like 'criminal' children without notice! Unbelievable! Well ... at least their names are well chosen: no comment with no style. |
| You are subscribed to email updates from Security Bloggers Network To stop receiving these emails, you may unsubscribe now. | Email Delivery powered by FeedBurner |
| Inbox too full? | |
| If you prefer to unsubscribe via postal mail, write to: Security Bloggers Network, c/o FeedBurner, 20 W Kinzie, 9th Floor, Chicago IL USA 60610 | |
![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=b170b650-daed-4013-8430-5d356a36f085)









No comments:
Post a Comment