Spliced feed for Security Bloggers Network |
| The Network Is the Computer...(Is the Network, Is the Computer...) [Rational Survivability] Posted: 21 Sep 2008 03:01 AM CDT
The precipitate convergence of virtualized compute, network and storage is really beginning to take significant form; after five hard years of hungering for the materialization of the technology, enterprise architecture, and market/business readiness, the notion of a virtualized datacenter OS with a value proposition larger than just " cost-optimized infrastructure" has now become a deliciously palpable reality. The overlap and collision of many leading technology providers' "next generation" datacenter (OS) blueprints is something I have written about before. In many cases there's reasonable alignment between the overall messaging and promised end result, but the proof is in the implementation pudding. I'm not going to rehash this here because I instead want to pick on something I've been talking about for quite some time. From a network and security perspective, things are about to (again) fundamentally and profoundly change in terms of how we operationally design, provision, orchestrate, manage, govern and secure our infrastructure, applications and information. It's important to realize that this goes way beyond just adding a 'v' to the name of a product. What's incredibly interesting is the definition and context of where and what makes up the "network" that transports all our bits and how the resources and transports interact to deliver them securely. It should be clear that even in a homogenous platform deployment, there exists an overwhelming complex conglomerate of mechanisms that make up the machinery enabling virtualization today. I think it's fair to say that we're having a difficult time dealing with the non-virtualized model we have today. Virtualization? She's a cruel mistress bent on reminding us we've yet to take out the trash as promised. I'm going to use this post to highlight just how "complexly simple" virtual networking and security have become using as an example the last two days' worth of announcements, initiatives and demonstrations of technology and solutions from Intel, VMware, Cisco and the dozens of security ISV's we know and love. Each of the bumps in these virtual wires deserves its own post, which they are going to get, especially VMware's vNetwork/VMsafe, distributed network switch, and Cisco's Nexus 1000v virtual switch announcements. I'm going to break each of these elemental functions down in much more detail later as they are simply amazing. Now that networking is abstracted across almost every layer of this model and in many cases managed by separate organizational siloes and technologies, how on earth are we going to instantiate a security policy that is consistent across all strata? We're used to this problem today in physical appliances, but the isolation and well-definable goesinta/goesouta perimeterized boundaries allows us to easily draw lines around where these policy differentials intersect. It's used to be the devil you knew. Now it's eleven different devils in disguise. As you visualize the model below and examine how it applies to your experience, I challenge you to tell me where the "network" lives in this stack and how, at a minimum, you think you're going to secure it. This is where all those vendor roadmaps that are colliding and intersecting start to look like a hodgepodge: In the example model I show here, any one of these elements -- potentially present in a single VMware ESX host -- can directly or indirectly instantiate a set of networking or security functions and policies that are discrete from one another's purview but ultimately interrelated or even dependent in ways and using methods we've not enjoyed before. In many cases, these layered components are abstracted from one another and managed by separate groups. We're seeing the re-emergence of network-centricity, it's just that the network is camouflaged in all its cloudy goodness. This isn't a story where we talk about clearly demarcated hosts that plug into "THE" network, regardless of whether there's a hypervisor in the picture.
Here's where it gets fun... In this model you have agents in the Guest OS interacting with security/networking virtual appliances on the ESX host either inline or via vnetworking APIs (switching or security) which in turn uses a fastpath networking kernel driver connected to VMware's vSwitch while another VA/VM is connected to a Cisco Nexus 1000v vSwitch implemented as a second distributed virtual network switching fabric which are all running atop an Intel CPU utilizing SR-IOV via VT-d in the chipset which in turn allows VM's to direct attach (bypassing the VMM) to NIC cards with embedded switching connected to your network/storage fabrics... Mass hysteria, cats and dogs living together... So I'll ask you again: "Where's the network in that picture?" Or, more precisely, "where isn't it?" This so hugely profound, but that may because I've been exposed to each of the bubbles in this diagram and see how each of them relate or do not. When you step back and look at how, as an example, Cisco and VMware are both going through strategic sea changes in how they are thinking about networking and security, it's truly amazing but I think the notion of network intelligence is a little less cut and dry as some might have us believe. Is this as mind-blowing to you as it is to me? If not, wait until I rip open the whole vNetworking and Nexus 1000v stuff. Very, very cool. /Hoff |
| Our "Near" Economic Depression and What Its Likely Cost Us [The Converging Network] Posted: 21 Sep 2008 01:46 AM CDT
After concerns for my own investments, my next thoughts turned to my hopes we would fix our out of control health care insurance system and make serious moves to becoming the global leader in alternative energies. If the federal government is willing to plop down $1 trillion of our money to save our economic system from utter collapse, will we have the focus, willpower, and cahoonas to invest in alternative energy development and reforming health care? My fear is we'll spend the next 3-4 years tied up with hearings, investigations, commissions, and work on legislation to re-invent our financial system. Will we have the national will to address health care and energy or will we be consumed by the fallout and responses to our current economic meltdown? Certainly, fixing our governmental and financial system failures is top priority. We've also got to get the economy growing again, and get the unemployed back to work. But no matter who you choose to blame, Republicans or Democrats, the Congress or the White House, under enforced government regulations, lax oversight, sub-prime mortgage lenders, or corrupt Wall Street companies, etc., we still have to get our economy moving again. Fixing our financial crisis may costs us a lot more than just the $1 trillion we're putting down right now. We may have sacrificed our chances for healthcare reform and energy independence in the process. I certainly hope that's not the case. |
| VMWare's VirtSec Vision...Virtual Validation? [Rational Survivability] Posted: 20 Sep 2008 11:52 PM CDT Rich Miller from one of my favorite blogs, Telematique, wrapped up his VMworld 2008 coverage in a post titled "What Happens In Vegas..." Rich made a number of very interesting observations, one of which caught my eye: The theme I noted most at VMworld 2007 a year ago was "security." This year, it seemed noticeably absent. My sense is that the industry has yet to catch up and capitalize on VMsafe. Because all of the "next generation" of offerings from VMware and the independent providers are still in development, no one made too much of security issues.
As I alluded to in my post titled "VMWorld 2008: Forecast For VMware? Cloudy...Weep For Security?" the messaging associated with this years re-branding certainly had the word "security" front and center under the Application vServices pillar:
I think, however, this would be a rather short-sighted perspective. While the tremendous amount of re-branding and messaging certainly "clouded" the horizon in some cases, it was clear that the underlying technology roadmap that was shown (and demonstrated as being real in the labs I participated in) lays down some pretty significant clues as to what's in store from VMware in regards to security. More on that in a minute... You might recall my debate with Citrix's CTO, Simon Crosby, on what, where and how virtualization platform providers should invest in terms of security. Our divergent views were quite passionate, but I maintain that my perspective is that echoed by the majority of the folks I've spoken to over the last 3 years. My position, presented in this post, is best summarized thusly: "...that it is the responsibility of virtualization platform providers to ensure that their [virtualized] data center operating system platforms of the future" don't become the next generation of insecure infrastructure. ... It's important to understand that I'm not suggesting that virtualization platform providers should secure the actual guest operating systems but they should enable an easier and more effective way of doing so when virtualized. I mean that the virtualization platform providers should ensure the security of the instantiation of those guests as "hosted" by the virtualization platform. In some cases this means leveraging technology present in the virtualization platform to do things that non-virtualized instances cannot. That's more than just securing the hypervisor." What did I mean by that? Obviously since I was using VMware as the model for my position, I was referring to VMsafe as the ecosystem enabler, but I was also referring to VMware's prior security acquisition in 2007 of Determina as a fundamental building block for the virtualization platform's security efforts. Pair that with the root of VM/VMM introspection that Mendel and Tal Garfinkel envisioned back in the day, and things start to make sense... So back to the original point of this post, which is where VMware's efforts are focused in terms of security. I think that this year's show concreted a two definites in my book:
What this ultimately means to me is that within the next 24 months with the delivery of VI4, a mature VMsafe API and shipping ISV code, we'll see some of the natural market consolidation activity occur and VMware will lock and load, snap up one or more of the emerging security players in the VirtSec space and bolster their platform's security capabilities. I think we've just seen the beginning of what VMware has to offer from a security perspective. They (and us) have a tremendously long way to go, but every cloud's got a silver lining... /Hoff |
| Judge: Cheney Must Preserve Records [Liquidmatrix Security Digest] Posted: 20 Sep 2008 06:56 PM CDT  It has been a weird long ride with the current US administration. We have seen some odd tech security things like the missing email saga and Cheney’s attempt to reclassify this documents as being beyond the reach of the national archive. Well, one of those things has been rectified. On paper at least. From CNN:
A very interesting turn of events. I wonder if he/they will comply. |
| New technique to perform universal website hijacking [GNUCITIZEN] Posted: 20 Sep 2008 09:56 AM CDT I’m really excited that HITBSecConf2008 Malaysia is coming up soon: end of October to be precise. I highly recommend our readers to attend such event, as it’s organized by one of the finest security event crews I have ever dealt with. There are tons of talks I want to attend, which I will cover in another post. The GNUCITIZEN team would like to thank the Hack in the Box (HITB) staff for inviting us to the Malaysia edition of the conference, making this the second time pdp and I will speak at HITBSecConf. The HITBSecConf crew includes Dhillon, geek00l, spoonfork, Belinda, Prabu, RuFI0 and Amy among others. Thank you guys, we’re really humbled by your invitation. I will be delivering the updated version of my Cracking into Embedded Devices and Beyond! presentation, which will include a quite special - i.e.: unusual - 0day vulnerability which I have successfully reported via Zero Day Initiative. The 0day vulnWell, I cannot give full details on the vulnerability at this moment, due to ZDI’s advisory not being published yet. I’m planning to release the full details for the first time on 30th October at HITBSecConf2008 Malaysia. However, there are a few things I can tell you for the moment being. First of all, the affected system is an embedded device, which is quite obvious by reading the name of my presentation. More precisely, the vulnerability affects appliances of a well-known firewall vendor. Usually, web cross-domain vulnerabilities, affect either a server-side service/application, or client-side software. For instance, we might have a cross-domain vulnerability on the target site itself (i.e.: XSS/HTML injection), or on a client-side component present on the victim’s user component. i.e.: web browser itself or web browser plugin. In the case of my finding however, the targeted website can still be hijacked even if the site is NOT vulnerable to XSS, and even if the client-side software on the victim’s computer is not vulnerable to any cross-domain vulnerability. In this case, the attacker exploits a vulnerability which doesn’t affect the targeted website, nor the software installed on the victim user’s computer. Instead, the attacker exploits a vulnerability on the firewall appliance in charge of In summary, by exploiting this vulnerability the attacker:
There is virtually nothing the victim user can do to protect against this attack if his/her connection is “protected” by a firewall appliance affected by this vulnerability. There are other factors that make this vulnerability quite special, but as I said, I can’t give too many details for now. All in all, this finding is a good reminder that our online security not only depends on end-point systems such as the client and server that have established a connection, but also all the hops/devices in between! |
| Oprah got pwned by Anonymous [Vitalsecurity.org - A Revolution is the Solution] Posted: 20 Sep 2008 09:26 AM CDT Anonymous are really chalking up the victims this week. "We do not forgive, we do not forget" is a well known Anon phrase. Similarly, "Over 9000" is an extremely well known net meme. Put the two together, post extreme trollbait onto Oprahs forum during an Anon invasion and you end up with this. An amazingly stupid prank, but once again proving people will say anything on television without actually stopping to think about it first. Apparently the forum trolling got so bad that they had to take the forum offline while they cleaned it up, too (they claim its down for "maintenance" but meh). (Thanks to Sammi_Babe for the tip and screenies). |
| Joomla hack to remind you [belsec] [Belgian Security Blognetwork] Posted: 20 Sep 2008 09:25 AM CDT that you need to update and patch your Joomla and if that is done, you need to review all the external templates that you use and try to be as standard as possible. http://cms-joomla.webservice4you.eu/ Joomla hacking is still going on and on
|
| hack of the day dereporters.be [belsec] [Belgian Security Blognetwork] Posted: 20 Sep 2008 09:22 AM CDT |
| Cisco Buys Open Source IM Service Jabber [Infosecurity.US] Posted: 19 Sep 2008 06:06 PM CDT
News , yesterday morning, of Cisco Systems, Inc.’s (NasdaqGS: CSCO) purchase (or at least an announcement of a definitive agreement…) of Jabber, the open source instant messenger service.
|
| Frank Robben nieuwe presentaties [belsec] [Belgian Security Blognetwork] Posted: 19 Sep 2008 04:22 PM CDT |
| Deze week op De Standaard [belsec] [Belgian Security Blognetwork] Posted: 19 Sep 2008 04:19 PM CDT Deze stukken werden deze week exclusief op destandaard.be gepubliceerd.
De belsec van Belgian security bloggers is hier
Onze vragen bij onze electronische identiteitskaart (EID) 3/5Onze vragen bij onze electronische identiteitskaart (EID) deel 2Onze vragen bij onze Electronische Identiteitskaart (EID) Deel 1Emailarchivering wordt steeds noodzakelijkerGeen e-discovery bij Koekelberg onderzoekenOver banken, online bankieren en risicoEr zijn gehackte websites en gehackte websites |
| Posted: 19 Sep 2008 09:04 AM CDT |
| Security Briefing: September 19th [Liquidmatrix Security Digest] Posted: 19 Sep 2008 08:14 AM CDT  Arrr me hearties. A fair morning to ye says I. OK, there, I got it out of my system. The pirate talk, not the head cold. Yes, as I’m sure you may have heard today is “international talk like a pirate day“. Fill yer boots. And a good weekend to all. Click here to subscribe to Liquidmatrix Security Digest!. And now, the news…
Tags: News, Daily Links, Security Blog, Information Security, Security News |
| Napera @ Interop NY 2008 [Napera Networks] Posted: 19 Sep 2008 07:15 AM CDT
Interop NY has been a great show this year. Although always a little quieter than the West Coast event, there were plenty of familiar faces and the combination of Interop with the Web 2.0 conference in the same venue kept the Javits Center busy yesterday.
Mike Fratto hosted an interesting and well attended panel on NAC yesterday, and there was plenty of spirited interaction from the audience. Steve Hanna from Juniper did a great job of explaining the Trusted Computing Group standards around NAC, and along with the audience asked the obvious question of why Cisco hasn’t done more to support TCG’s TNC standard. According to Cisco the jury is still out until the IETF ratify their variant sometime in 2009.
I’m speaking on building products with SaaS at 10:15 this morning, a topic I’ve written on before. Come by and say hello!.
|
| Fujitsu Siemens Amilo - RIP..... for now..... [miekiemoes] [Belgian Security Blognetwork] Posted: 19 Sep 2008 05:52 AM CDT  This was going to happen some day anyway... I finally managed to spill a full mug of coffee (big size) all over my laptop. In less than a second, the coffee had covered my entire computer desk. Luckily, my other laptop next to it was on a notebook cooler pad, so that one was saved. The screen went black immediately, strange noises from underneath... and I sweared like never before. Unfortunately, the swearing didn't work, so instead, I immediately disconnected the power supply and took out the battery. I put the unit on its side and the coffee was dripping out. I left it in that position for at least an hour. I cleaned the rest of the mess I made, apart from the stains on the wall (Mr Proper can take care of that). Then I turned it upside down, opened it and I'm going to let it dry for at least 24 hours. In a way, I'm glad I don't like milk and sugar in my coffee, so maybe there's still hope... but I doubt it. My dear Fujitsu Siemens Amilo, May The Force Be With You. UPDATE! I couldn't wait any longer (waited for two days to let it dry)... so... it's up and running again!! No issues so far - everything works. I was really lucky :-) |
| Information Security Training [GNUCITIZEN] Posted: 19 Sep 2008 05:10 AM CDT This is a quick announcement regarding GNUCITIZEN’s training events. Now you can book an event of your choice from the form over here. We will get in touch with you as soon as we have a set date for the course of your choice. We are also planning to launch an initiative which have been on the drawing board for long time now. This is the |
| His name was... [Vitalsecurity.org - A Revolution is the Solution] Posted: 19 Sep 2008 03:17 AM CDT |
| Posted: 18 Sep 2008 10:59 PM CDT |
| A Long Day [BumpInTheWire.com] Posted: 18 Sep 2008 10:53 PM CDT Just a few quick notes tonight… Had an odd behavior on one of our new LANenforcer 2024s today. For whatever reason it would not resolve our domain controllers by just hostname. The fully qualified domain name would resolve but the hostname would not. A quick solution was to add the domain controllers by IP address or FQDN. Sunday we will be upgrading our two older LE 2024s to the latest 5.1 code. We’ve got some fairly good testing done on the new code release with over 100 users on LEs with the new code. I think its time to get the rest of the environment current. One thing that would be a really nice and seemingly simple “feature” to add to the LANsight/LANenforcer solution would be a place for a description of what is going through each port pair. Its easy enough to figure out what switch is going through what port pair by searching for the management IP address of the switch but a description would be a real nice luxury. And from my non-programming point of view it can’t be to terribly tough to add. There is a decent chance I’ve mentioned that before in these ramblings but the squeaky wheel gets the grease. Ever seen Shawshank Redemption? I’m Andy Dufraine and I’m gonna write the State a letter every week until they allocate funds for some books add a field for a description! |
| Hacktivism: Offensive Computing and the Rise of the Political Hacker [Amrit Williams Blog] Posted: 18 Sep 2008 07:44 PM CDT As I am sure most have heard Sarah Palin’s yahoo account was recently hacked and the contents posted online. There has been a lot of debate about the legality of such action (by both the hacker misguided youth - who couldn’t care less, although his father is probably pissed (here) - and by Palin for using a private email account for government business) neither are terribly interesting in the context of cyber security and from a political perspective it isn’t like Obama is immune to email hacking either (here). But again the mainstream media is missing the most important point - aside from the raucous cries of partisanship, which reverberate through every election, the reality is that malicious hackers may have a material impact on a US presidential election if not in 2008 then certainly within my lifetime. The current state of cyber security is abysmal, the lack of confidence in the US political process has been strained and this election has played the social *ism cards, such as terrorism, racism, sexism, ageism, and lipstick on a pigism, more than any other in recent history. You know it is getting ugly when a Republican political strategist like Karl Rove states that the Republicans have “gone too far” (here), this is like Ted Bundy telling Joseph Francis, the creator of “Girls Gone Wild”, that he mistreats women. The conditions are ripe for digital election manipulation in multiple forms, this is not to say that voter manipulation is new, nor is hactivism (here), what is new is the impact it may have on a US presidential election. So what has changed and why now? 1. Information integrity: First and foremost there has been a sea change in how information is shared, manipulated, and redirected. Traditional media is now facing extinction against a flood of new media outlets, from blogs to social media to social networking, information flow is fast and pervasive. The problem with an information rich environment is the quality of the information is dramatically reduced. In the frenzy to quickly post a story fact-checking may be haphazard, if done at all, and something may propagate from rumor on a blog to discussion on chat rooms to the front page of a global media’s online edition in a matter of hours. Imagine this “information” sharing during the critical moments of a campaign - it would have a material impact on when, how, and even if some citizens vote. 2. Counterfeit reality: Photoshop and similar technologies have dramatically expanded the ability for people to manipulate images, in many cases to the point that it becomes nearly impossible, without sophisticated methods, to determine the validity of such images. Just like in years past there has been no shortage of political Photoshop, for the most part these have been more for humorous purposes, but it wouldn’t be difficult to imagine counterfeit reality being used to demean a candidate, misrepresent a situation, or create an international incident (here) 3. Vote manipulation: The most significant impact hackers may have on a political election is manipulation of the actual votes themselves. There have been many stories of security problems related to electronic voting machines and at the end of 2007 California Secretary of State, Debra Bowen, withdrew approval for multiple electronic voting machines citing significant security concerns (here). Although some may argue that the impact would be isolated since the theory is that these voting systems would only be deployed in an air-gap network, the reality is that electronic media is generally transferred, correlated and eventually archived and throughout this process additional attack vectors become available. None of this is new; propaganda, voter fraud, data modification, counterfeit reality, and all manner of manipulation have been used for centuries, what has changed is that the electronic medium introduces levels of speed, pervasiveness and quality of fraudulent material that is very difficult to replicate in traditional mediums. I have no doubt that we will see a significant electronic “incident” occur during either this or an upcoming presidential election. <update 9/19/2008: Although not terribly relevant, apparently Bill “Papa Bear” O’Reilly, the Fox News savior of the downtrodden and misaligned conservative right and Stephen Colbert inspiration, has been hacked for making disparaging comments about Palin being hacked (here) - ha!>  |
| Untangle for Windows - Exploding the Myths [untangling the future...] Posted: 18 Sep 2008 07:34 PM CDT
I suppose that we should consider it a success of sorts that so many people are talking about it — and we do. But please allow me to set the record straight in several areas…. Here are some of the claims being made, along with my responses to them:
So that’s how we see it. We think that the “small business” market (10-100 users) will see it this way too. And their networks will be safer, more reliable, and less expensive to operate because of it.
|
| Noscript vs SurfJacking [Hackers Center Blogs] Posted: 18 Sep 2008 06:00 PM CDT |
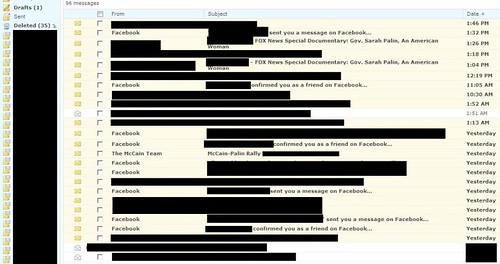
| Another Republican Hacked? [Vitalsecurity.org - A Revolution is the Solution] Posted: 18 Sep 2008 02:51 PM CDT It's funny that Sarah Palin should get owned via a freebie Yahoo account, because I've been dealing with a similar situation for the best part of a week now. There's some Republican guy who lists himself as a candidate for President (though I'm sorry to say I've never actually heard of him). He seems to have been using hotmail for some of his dealings - when will people learn not to use free email accounts for anything important? - because a number of hacking forums have been posting up this screenshot:
If the screenshot is legit - and the email address mentioned on forums matches up as something this person has been using - then someone has indeed taken it over. Sources are informing me its likely to be used in a bidding war, the winner taking home all the contacts in the address book and anything else in there that's remotely interesting. I've blanked out anything that's more personal than a mailshot, but I can say that there's a lot of folders down the side with all sorts of names related to travel, insurance, credit and who-knows-what else. I'd imagine those folders contain information the owner doesn't want other people to see. I tried emailing his campaign people, repeatedly - everything bounced. All the phone numbers listed either disconnect or leave you with voicemails that cut you off (no way you can try and explain something like this to some old dude on a phone in 25 seconds or less). His official website is down. I can't risk sending him a message on Facebook or anywhere else in case the hackers own those accounts too. I finally got hold of some random guy who apparently works for the individual in question. Rather depressingly, the conversation went something like this: Me: "Hi, we believe the person you work for has had their email compromised". Them: "I'm busy right now, call back later". Me: "...." / Click Yeah, this is going well so far. |
| You are subscribed to email updates from Security Bloggers Network To stop receiving these emails, you may unsubscribe now. | Email Delivery powered by FeedBurner |
| Inbox too full? | |
| If you prefer to unsubscribe via postal mail, write to: Security Bloggers Network, c/o FeedBurner, 20 W Kinzie, 9th Floor, Chicago IL USA 60610 | |
 600,000 jobs lost already this year.
600,000 jobs lost already this year.  Everybody hinted at it but no one would use the word "depression" until Senator Chuck Schumer publicly said on Saturday that a depression was a possible result if the federal government didn't take the action of buying up bad mortgage debt from banks. I only hope congress will not only put the mortgage debt legislation in place, but also include some obviously needed regulatory oversight controls, help for the likely mortgage defaults and personal bankruptcies still to come, and recoup the executive compensation of the officers and execs at the failed institutions the taxpayers now own. In a relatively few days our financial market system will have gone from an unfettered, corrupt and under enforced market to one that we the taxpayers own and operate a great deal of.
Everybody hinted at it but no one would use the word "depression" until Senator Chuck Schumer publicly said on Saturday that a depression was a possible result if the federal government didn't take the action of buying up bad mortgage debt from banks. I only hope congress will not only put the mortgage debt legislation in place, but also include some obviously needed regulatory oversight controls, help for the likely mortgage defaults and personal bankruptcies still to come, and recoup the executive compensation of the officers and execs at the failed institutions the taxpayers now own. In a relatively few days our financial market system will have gone from an unfettered, corrupt and under enforced market to one that we the taxpayers own and operate a great deal of.





 In the 48 hours since its release, several myths have already begun to emerge about “Untangle for Windows” and its patent-pending Re-router™ technology.
In the 48 hours since its release, several myths have already begun to emerge about “Untangle for Windows” and its patent-pending Re-router™ technology.
No comments:
Post a Comment