Spliced feed for Security Bloggers Network |
| IDS Signature for Wonderware Suitelink Vuln [Digital Bond] Posted: 15 Sep 2008 07:26 AM CDT We have added a new category of signatures to our SCADA IDS Signatures. Previous categories are protocol based: Modbus TCP, DNP3 and ICCP. The latest category is Vulnerability Exploit. Signatures in this category identify exploit attempts on disclosed vulnerabilities in control system applications or devices. We will write these signatures if enough information has been disclosed to allow a moderately skilled hacker to write an exploit or if the exploit is widely available in the wild. The Citect module for metasploit released last week prompted the first signature. Similarly, there is detailed information on the Wonderware SuiteLink vulnerability, and we have seen and used exploits that have been developed by others for this vuln. So here is the related Wonderware SuiteLink signature that Kevin Lackey wrote: alert tcp $EXTERNAL_NET ANY -> $HOME_NET 5413 (msg:"WonderWare SuiteLink DOS Attempt"; flow:established,to_server; byte_test:4,>,2742,56,little; reference:cve, CVE-2008-2005 ; sid:1111602; rev:1; priority:1;) These will be tracked on a SCADApedia page. Digital Bond site subscribers can download all of the SCADA IDS signatures and view the documentation page for each signature. |
| Posted: 14 Sep 2008 10:34 PM CDT A laissez-fare, hands attitude towards regulation of the financial industry is just plain naive. The outcome of this mess will be that there are going to be new regulations and rules put in place to oversee the financial industry. This will be necessary to show that the industry is worthy of the confidence of the investing public. You can count on it. What will all this mean for the security industry? Who knows for sure. On one hand under the present conditions, the financial sector, long a foundational vertical for just about every security vendor will not have a lot of spare cash for IT in general and I am sure security in particular. It will be rough sledding trying to convince financial firms that now is a great time to invest money in the latest security technologies. On the other hand, new regulations and oversight could lead to more compliance. Who can argue that Sarbanes-Oxley did not boost security spending. By the same measure any new regulation of the industry should have a corresponding element of security and data integrity as part of it. The issue is that it may be some time until legislation is passed and put into effect. Until then healthcare and some of the other traditional security verticals are going to be receiving a lot of attention from security vendors I bet. Overall, the security industry will make out better than many other IT sectors. This meltdown is going to reshape not only Wall Street but Main Street as well. But in the end there will still be storefronts selling IT security. Related articles by Zemanta
![Reblog this post [with Zemanta]](http://img.zemanta.com/reblog_e.png?x-id=3fb67ad2-844d-4f8b-897d-254325a227c1) |
| Political cartoon with an anti-spam edge [StillSecure, After All These Years] Posted: 14 Sep 2008 09:52 PM CDT |
| The office fish didn’t make it but we’re ok [Alert Logic] Posted: 14 Sep 2008 07:35 PM CDT Well the storm has passed and everyone here is ok. During the storm our Dallas team worked with the Sydney team to keep everything running smoothly. Our data center managed to keep power and managed to avoid switching to generator power. If they do require a switch they have 5+ days of fuel so there [...] |
| Posted: 14 Sep 2008 06:41 PM CDT  Eric Savitz at Barrons writes that eBay's (EBAY) business is "deteriorating" and is preparing big layoffs (like: 1500-employees big). Eric Savitz at Barrons writes that eBay's (EBAY) business is "deteriorating" and is preparing big layoffs (like: 1500-employees big).Ina Steiner seems to agree, pointing out that "Meg Whitman and her inner circle of top executives are gone." I say: good. And not a moment too soon. eBay is now a complete, unmitigated disaster zone:
Hat tip: Techmeme |
| CGISecurity turns 8! [CGISecurity - Website and Application Security News] Posted: 14 Sep 2008 02:54 PM CDT I'm happy to announce CGISecurity's 8th year providing website, and application security news as of today. What started out as an excuse to learn about web based vulnerabilities has really evolved. Here are a few things to put into perspective - The following terms hadn't been coined yet - CSRF/XSRF/Cross-site Request... |
| SNL Spoofs Palin/Hillary [Liquidmatrix Security Digest] Posted: 14 Sep 2008 01:10 PM CDT OK, this has little to do with security per se. But damn, this is funny. Enjoy! Tags: Palin, Clinton, SNL, NBC SNL, Heartbeat Away |
| CERN Website Hacked [Liquidmatrix Security Digest] Posted: 14 Sep 2008 10:14 AM CDT 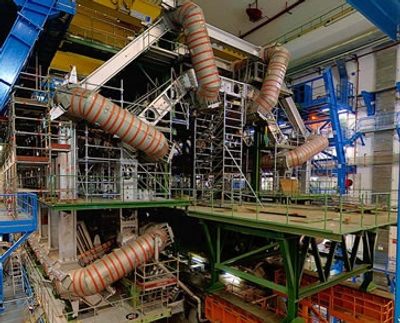 The alarm bells started ringing this week after the Hadron Collider at CERN went online. But, not for any problem with the system itself. Rather, a website related to it was defaced. From The Telegraph:
This normally wouldn’t be too much of a problem however the network hosting the webserver was a little too close to this behemoth of a machine. How close you ask?
Um, whut? Why isn’t this 3 billion € machine segregated? This seems to be akin to attaching a SCADA network to the internet. Not this wisest idea. So what was this website running on before it got taken down? Well, as of Sept 10th it was reporting “Apache/2.2.4 (Unix) DAV/2 proxy_html/2.5 mod_jk/1.2.20 mod_ssl/2.2.4 OpenSSL/0.9.8d ” on Netcraft. Well, running a pwnable version of Apache is a good indication of how they got access. So, CERN, looking for some infosec staff? For the full article read on. Tags: CERN, Hadron Collider, CMS, Defacement |
| More DRM Nonsense [Liquidmatrix Security Digest] Posted: 14 Sep 2008 09:25 AM CDT  The music industry’s attempts to lock down digital media failed in the past. So, rather than take a hint from the music biz failures. Hollywood is trying again. They’re back for more. From the LA Times:
Same crap different day. I used to use Napster and the like years ago. And my music collection swelled. Not because I was pilfering music. Quite the contrary. I would find music that I enjoyed and subsequently bought the albums. The entertainment field is constantly in a reaction mode rather than looking forward when it comes to digital media. I remember during my interview for MCA Records back in ‘94 where my future boss asked me where I saw the music industry going in 10 years. I looked at him and said, “online”. “I don’t know how it will happen but, it’ll be online”. He laughed and said, “It’ll never happen”. I’d love to run into him again. I think that would be an amusing reunion. For me anyway. Tags: DRM, DECE, Napster, Digital Media |
| nf_conntrack and the conntrack program [Robert Penz Blog] Posted: 14 Sep 2008 08:50 AM CDT Today I had a problem with my VoIP connection to my provider. The hardware SIP client did not connect for some hours. I had a look at the packets which went over my router into the internet. At the first glance it looked as everything worked right on my side, but the other side did not answer.
But at a closer look i realized that the Anyway I did at a fast
The timeout for this entry is 180 sec and 172 seconds to go, and the SIP client was all the time sending new probes and therefore the connection was never dropped. What can you do in this instance? You can install conntrack. It is a userspace command line program targeted at system administrators. It enables you to view and manage the in-kernel connection tracking state table. If you want to take a look at the manual without installing it (apt-get install conntrack) you can take a look at this webpage which contains the man page. With this program I did delete the entries with the wrong IP address and everything worked again. I think this program and the knowledge of the connection tracking is important for many of my readers, so I’ve written this post. The current cause to talk about this topic is only one of many, so take a look at it. |
| Filter the output of command line programs e.g. run by cron [Robert Penz Blog] Posted: 14 Sep 2008 01:47 AM CDT Ever had to run a program by cron which writes always stuff to stdout and you therefore get every time a mail from cron? You did an I have sometimes that problem and therefore I’ve written a small python script which is run by cron and launches itself the real program. It takes any output of that program and filters it by configured regular expression rules. Everything that matches a rules is not reported. As soon as one line does not match, this line is reported and followed by the full output of the program to make the error finding easier. I often let programs run in verbose mode, as it is filtered anyway by the python script and if an error occurs it is nice to have more information at hand. The python script also forwards any provided parameter to the real program. There is the python script filterOutput.py. Just download it, set the execute permissions and open it in an file editor. following 3 variables are interesting for you:
|
| Its Saturday Again [BumpInTheWire.com] Posted: 13 Sep 2008 04:48 PM CDT |
| More on Confirmation Bias [Emergent Chaos] Posted: 13 Sep 2008 01:43 PM CDT Devan Desai has a really interesting post, Baffled By Community Organizing: First, it appears that hardcore left-wing and hardcore right-wing folks don’t process new data. An fMRI study found that confirmation bias -- “whereby we seek and find confirmatory evidence in support of already existing beliefs and ignore or reinterpret disconfirmatory evidence” -- is real. The study explicitly looked at politics...What can I say? Following up on my post, "Things Only An Astrologist Could Believe," I'm inclined to believe this research. |
| Jeremy Jaynes gets a free pass? [Richi Jennings] Posted: 13 Sep 2008 06:27 AM CDT  It's déjà vu all over again. I see that Jeremy Jaynes has won his most recent argument in Virginia that the state's anti-spam law is unconstitutional. (Once again, thanks to Slashdot for the heads-up.) It's déjà vu all over again. I see that Jeremy Jaynes has won his most recent argument in Virginia that the state's anti-spam law is unconstitutional. (Once again, thanks to Slashdot for the heads-up.)Jaynes would have us believe that spamming is protected speech under the U.S. First Amendment. The court didn't exactly say that, but concluded that the law as written was overly-broad, because it didn't explicitly differentiate between commercial speech and any other kind of speech (e.g., political expression). While I agree that anti-spam laws shouldn't restrict political speech, I have a couple of issues with this decision:
Again, I say I find it really hard to believe that the American founding fathers intended my inbox be full of spam. More at today's IT Blogwatch EXTRA... |
| Jeremy Jaynes Lost Appeal, but... [Richi Jennings] Posted: 13 Sep 2008 05:28 AM CDT  Hmmm, so I see that Jeremy Jaynes has lost his appeal in Virginia that spamming is protected speech under the U.S. First Amendment. (Thanks to Slashdot for the heads-up.) Hmmm, so I see that Jeremy Jaynes has lost his appeal in Virginia that spamming is protected speech under the U.S. First Amendment. (Thanks to Slashdot for the heads-up.)Jolly good, and no surprise there, I think. However, why on Earth was it a 4-to-3 split decision? What were those three state supreme court judges thinking? Well, according to the AP: Justice Elizabeth Lacy wrote in a dissent that the law is "unconstitutionally overbroad on its face because it prohibits the anonymous transmission of all unsolicited bulk e-mail including those containing political, religious or other speech protected by the First Amendment."Oh, balderdash. I find it really hard to believe that the American founding fathers intended my email to be full of spam. |
| Picture of Ike [An Information Security Place] Posted: 12 Sep 2008 07:57 PM CDT |
| Fixing Vulnerabilities in the Real World [ImperViews] Posted: 12 Sep 2008 04:20 PM CDT One of things I love about IT Security is the requirement to bridge the gap between human behavior and technology. Amichai and I recently delivered a webinar on the topic of Vulnerability Scanners and Web Application Firewalls that reminded me of this balancing act. There are camps on both sides that say you should use either scanners or WAFs (depending on where you sit). Theoretically, if you lived in a vacuum, that is a valid argument. But the truth is, we live in a world run by humans, and that's the fundamental reason why WAFs and Scanners belong together. Let me illustrate fixing vulnerabilities in the real world: |
| My Picks for OWASP NY AppSec 2008 [Jeremiah Grossman] Posted: 12 Sep 2008 02:04 PM CDT OWASP NY AppSec 2008 is only week away and is going to be big, really big, bigger than anyone expected I think. So big in fact that Tom Brennan, conference organizer, had to find a larger venue this week to accommodate all the attendees. The Park Central Hotel - 870 Seventh Avenue at 56th if you hadn't already seen the updated page. What Tom and Co. also did was create a jam-packed line-up of sweet looking presentations. So much so that everyone will probably miss something they wanted see because of dueling talk. Oh well, that's what video is for! While the schedule still seems to be in a bit of flux, I thought I'd list the stuff I'm most interested in and get my personal schedule going. Disclaimer: If I don't pick your talk it doesn't mean I don't like you or the material. :) It might be that I've already seen it and/or familiar with the content. Day 1 Web Application Security Road Map - Joe White Because its initiatives like this one that will eventually serve as a template for other organizations to follow. Http Bot Research - Andre M. DiMino - ShadowServer Foundation I have a soft spot for bots, seemed interesting, and wanted to see what data they have. Get Rich or Die Trying - Making Money on The Web, The Black Hat Way - Trey Ford, Tom Brennan, Jeremiah Grossman Well, you know, I sorta have to be there. :) New Exploit Techniques - Jeremiah Grossman & Robert "RSnake" Hansen One of those presentations exposing what Web attacks in the next 12-18 month will look like. We've purposely kept really quiet about what we plan to demonstrate, but its certainly going to make people a little nervous. :) Industry Outlook Panel Curious about what these folks have on their mind. Multidisciplinary Bank Attacks - Gunter Ollmann Good speaker and I enjoy hacking backs. :) Case Studies: Exploiting application testing tool deficiencies via "out of band" injection I have no idea, though appeared to be an interesting topic w3af - A Framework to own the web - Andres Riancho I'd like to see this tool demonstrated and understand what it can really do. Coding Secure w/PHP - Hans Zaunere Want to see more about how this is done. It can be right? Day 2 Best Practices Guide: Web Application Firewalls - Alexander Meisel A big toss up between this one and Pen Testing VS. Source Code Analysis, but had to go with the WAFs. Wanted to see what their point of view is and the guidance they're suggesting. APPSEC Red/Tiger Team Projects - Chris Nickerson Sounded cool, that's about it. Industry Analyst with Forrester Research - Chenxi Wang It's always good to know how the certain enterprises will be influenced Security in Agile Development - Dave Wichers As before, is this possible? And if so, how!? TELL ME! Next Generation Cross Site Scripting Worms - Arshan Dabirsiaghi cmon Arshan, no holding back. Give me the next NEXT generation XSS worms! :) NIST SAMATE Static Analysis Tool Exposition (SATE) - Vadim Okun Tools lined-up side-by-side and tested always interested me. Practical Advanced Threat Modeling - John Steven It's been a while since I attended a threat modeling talk, especially one targeted towards webappsec, which I hope this is. Off-shoring Application Development? Security is Still Your Problem - Rohyt Belani Uh yap it is, but what to do about it is the question. Hopefully Rohyt will answer that one. Flash Parameter Injection (FPI) - Ayal Yogev & Adi Sharabani Flash security is HUGE! HUGE I SAY! Most of these speakers I've never seen present before, which I find refreshing. New talent, new ideas, and shows an emerging industry. Good luck everyone! |
| GeoTrust and thawte roots now included in Opera [Tim Callan's SSL Blog] Posted: 12 Sep 2008 12:50 PM CDT Regular readers of The SSL Blog will know that Opera 9.5 supports EV and has supported the VeriSign root from the very beginning. Well, Opera 9.5 now contains native support for GeoTrust and thawte roots as well. |
| More intel on Chrome and SSL [Tim Callan's SSL Blog] Posted: 12 Sep 2008 12:40 PM CDT As promised I've looked a little more into the SSL behaviors in Chrome.
This is probably not the site you're looking for! You attempted to reach secure.mysite.com but instead reached the server identifying itself as www.mysite.com. This may be caused by a misconfiguration on the server or by something more serious. An attacker on your network could be trying to get you to visit a fake (and potentially harmful) version of www.mysite.com. You should not proceed.
|
| iPhone 2.1 actually lists its updates?! [Random Thoughts from Joel's World] Posted: 12 Sep 2008 08:49 AM CDT Very uncharacteristic for Apple, but the update screen for 2.1 actually lists its updates. Wow.
Thanks for letting us know all these things Apple, please keep up the straightforwardness in updates! |
| iPhone 2.1 is out, and here it is [Random Thoughts from Joel's World] Posted: 12 Sep 2008 08:45 AM CDT iPhone v2.1
Available for: iPhone v2.0 through v2.0.2 Impact: An application may be able to read another application's files Description: The Application Sandbox does not properly enforce access restrictions between third-party applications. This may allow a third-party application to read files in another third-party application's sandbox, and lead to the disclosure of sensitive information. This update addresses the issue by enforcing the proper access restrictions between application sandboxes. Credit to Nicolas Seriot of Sen:te and Bryce Cogswell for reporting this issue. This issue does not affect iPhone versions prior to v2.0.
Available for: iPhone v1.0 through v2.0.2 Impact: Multiple vulnerabilities in FreeType v2.3.5 Description: Multiple vulnerabilities exist in FreeType v2.3.5, the most serious of which may lead to arbitrary code execution when accessing maliciously crafted font data. This update addresses the issue by incorporating the security fixes from version 2.3.6 of FreeType. Further information is available via the FreeType site at http://www.freetype.org/
Available for: iPhone v1.0 through v2.0.2 Impact: mDNSResponder is susceptible to DNS cache poisoning and may return forged information Description: mDNSResponder provides translation between host names and IP addresses for applications that use its unicast DNS resolution API. A weakness in the DNS protocol may allow a remote attacker to perform DNS cache poisoning attacks. As a result, applications that rely on mDNSResponder for DNS may receive forged information. This update addresses the issue by implementing source port and transaction ID randomization to improve resilience against cache poisoning attacks. Credit to Dan Kaminsky of IOActive for reporting this issue.
Available for: iPhone v2.0 through v2.0.2 Impact: Predictable TCP initial sequence numbers generation may lead to TCP spoofing or session hijacking Description: TCP initial sequence numbers are sequentially generated. Predictable initial sequence numbers may allow a remote attacker to create a spoofed TCP connection or insert data into an existing TCP connection. This update addresses the issue by generating random TCP initial sequence numbers. This issue does not affect iPhone versions prior to v2.0.
Available for: iPhone v2.0 through v2.0.2 Impact: An unauthorized user may bypass the Passcode Lock and launch iPhone applications Description: The Passcode Lock feature is designed to prevent applications from being launched unless the correct passcode is entered. An implementation issue in the handling of emergency calls allows users with physical access to an iPhone to launch an application without the passcode by double clicking the home button in emergency call. This update addresses the issue through improved handling of emergency calls. Credit to Matthew Yohe of The University of Iowa's Department of Electrical and Computer Engineering for reporting this issue. This issue does not affect iPhone versions prior to v2.0.
Available for: iPhone v1.0 through v2.0.2 Impact: Visiting a maliciously crafted website may lead to an unexpected application termination or arbitrary code execution Description: A use-after-free issue exists in WebKit's handling of CSS import statements. Visiting a maliciously crafted website may lead to an unexpected application termination or arbitrary code execution. This update addresses the issue through improved handling of document references. |
| Zero "Zero False Positives" [ImperViews] Posted: 12 Sep 2008 08:45 AM CDT  I was in Boston earlier this week, participating in a vendor panel discussion. One of the other vendor representatives tried to explain how his solution added value by having a "true zero false positive" rate. I will not mention the name of this company as I think that the novel idea of having a security system with zero false positives is so far from reality that it simply shows that their representative does not understand security. It's like Superman - great idea and I wish it could be true - but in real life, he does not exist...(Wonder Woman does though :-) I was in Boston earlier this week, participating in a vendor panel discussion. One of the other vendor representatives tried to explain how his solution added value by having a "true zero false positive" rate. I will not mention the name of this company as I think that the novel idea of having a security system with zero false positives is so far from reality that it simply shows that their representative does not understand security. It's like Superman - great idea and I wish it could be true - but in real life, he does not exist...(Wonder Woman does though :-) |
| Friday News and Notes [Digital Bond] Posted: 12 Sep 2008 08:26 AM CDT
|
| Wow, Um, So hey, how you doing? [Random Thoughts from Joel's World] Posted: 12 Sep 2008 08:06 AM CDT Haven't Blogged in awhile, I've been working on some other stuff as well over at dearcupertino.com. For those of you that haven't seen, here's a bit of mac news, Apple released iTunes 8, a new set of iPod Nano's (going back to the more vertical shape), updated and dropped the price on the iPod Touch, as well as refreshing the iPod Classic line. Basically, for the holiday shopping season. Good stuff. They also released an update to the iPod Touch software (2.1), and it has some nifty features in it (like the Genius feature from iTunes 8.0). Reports are also, that it is faster. The iPhone update 2.1 is supposed to hit today, so I might blog again with some updates about that. Otherwise, for those who know me, and know that i have been on a single customer site for the past year+, I have 12 days left (including weekends.) |
| Your iPhone Is Watching You [Liquidmatrix Security Digest] Posted: 12 Sep 2008 07:43 AM CDT  Well, inadvertently it would seem. Data forensics wonk, Jonathan Zdziarski, indicated that when the iPhone does that cool fade out, when you switch applications, it takes a screen shot. No, there are no black helicopters here. This is apparently how the effect is achieved. From Wired:
I imagine it has the potential for being a privacy issue. In all fairness though, if someone already has access to your phone you’re pretty much fubar anyway. Tags: Forensics, Data Forensics, iPhone |
| Help fund historic computers at Bletchley Park [Emergent Chaos] Posted: 12 Sep 2008 07:17 AM CDT  Bletchley Park, the site in the UK where WWII code-breaking was done, has a computing museum. The showpiece of that museum is Colossus, one of world's first computers. (If you pick the right set of adjectives, you can say "first." Those adjectives are apparently, "electronic" and "programmable.") It has been rebuilt over the last fourteen years by a dedicated team, who have managed to figure out how it was constructed despite all the plans and actual machines having been dismantled. Of course, keeping such things running requires cash, and Bletchley Park has been scrambling for it for years now. The BBC reports that IBM and PGP have started a consortium of high-tech companies to help fund the museum, starting with £57,000 (which appears to be what the exchange rate is on $100,000). PGP has also set up a web page for contributions through PayPal at http://www.pgp.com/stationx, and if you contribute at least £25 (these days actually less than $50), you get a limited-edition t-shirt complete with a cryptographic message on it. An interesting facet of the news is that Bletchley Park is a British site and the companies starting this funding initiative are each American companies. Additionally, while PGP is an encryption company and thus has a connection to Bletchley Park as a codebreaking organization, one of the major points that PGP and IBM are making is that Bletchley Park is indeed a birthplace (if not the birthplace) of computing in general. This is an interesting viewpoint, particularly if you consider the connection of Alan Turing himself. Turing's impact on computing in general is more than his specific contributions to computers -- he was a mathematician far more than an engineer. He was involved in designing Colossus, but the real credit goes to Tommy Flowers, who actually built the thing. If we look at the history of computing, an interesting thing seems to have happened. The Allies built Colossus during the war, and then when the war ended agreed to forget about it. The Colossi were all smashed, but many people involved went elsewhere and took what they learned from Colossus to make all the early computers that seemed to have names that end in "-IAC." (A major exception is the work of Konrad Zuse, who not only built mechanical programmable computers before these electronic ones, but some early electronic ones, as well.) This outgrowth from Colossus also seems to include the work that turned IBM from being a company that primarily made punched cards and typewriters to one that made computers. It is thus nice to see IBM the computing giant pointing to Colossus and Bletchley as a piece of history worth saving along with the cryptographers at PGP. It is their history, too. I think this dual parentage makes Bletchley Park doubly worth saving. The information economy has computers and information security at its core, and Colossus sits at the origins of both. Please join us in helping save the history of the information society. |
| You are subscribed to email updates from Security Bloggers Network To stop receiving these emails, you may unsubscribe now. | Email Delivery powered by FeedBurner |
| Inbox too full? | |
| If you prefer to unsubscribe via postal mail, write to: Security Bloggers Network, c/o FeedBurner, 20 W Kinzie, 9th Floor, Chicago IL USA 60610 | |



No comments:
Post a Comment